Apply DA Tag

This article was updated on January 30, 2024. Income verification is a critical step in determining a consumer’s ability to pay. The challenge is verifying income in a way that’s seamless for both lenders and consumers. While many businesses have already implemented automated solutions to streamline operations, some are still relying on manual processes built on older technology. Let’s take a closer look at the drawbacks of traditional verification processes and how Experian can help businesses deliver frictionless verification experiences. The drawbacks of traditional income verification Employment and income verification provides lenders with greater visibility into consumers’ financial stability. But it often results in high-touch, high-friction experiences when done manually. This can be frustrating for both lenders and potential borrowers: For lenders: Manual verification processes are extremely tedious and time-consuming for lenders as it requires physically collecting and reviewing documents. Additionally, without reliable income data, it can be difficult for lenders to accurately determine a consumer’s ability to pay, leading to higher origination risk. For borrowers: Today’s consumers have grown accustomed to digital experiences that are fast, simple, and convenient. A verification process that is slow and manual may cause consumers to drop off altogether. How can this process be optimized? To accelerate the verification process and gain a more complete view of consumers’ financial stability, lenders must look to automated solutions. With automated income verification, lenders obtain timely income reports to accurately verify consumers’ income in minutes rather than days or weeks. Not only does this allow lenders to approve more applicants quickly, but it also enables them to devote more time and resources toward improving their strategies and enhancing the customer experience. The right verification solution can also capture a wider variety of income scenarios. With the click of a button, consumers can give lenders permission to access their financial accounts, including checking, savings, 401k, and brokerage accounts. This creates a frictionless verification experience for consumers as their income information is quickly extracted and reviewed. Retrieving data directly from financial accounts also provides lenders with a fuller financial picture of consumers, including those with thin or no credit files. This helps increase the chances of approval for underserved communities and allows lenders to expand their customer base without taking on additional risk.1 Learn more 1 Experian Income Verification Product Sheet (2017).

This article was updated on January 26, 2024. Marketers are facing new challenges as third-party cookies crumble, and people use more devices throughout the day. Someone might comparison shop on their laptop in the morning, do more research on a tablet in the afternoon and finally decide to make a purchase on their phone before falling asleep at night. Being able to track these movements and insert yourself where appropriate can be difficult, but it's not impossible. One solution that's becoming increasingly attractive is creating a unified identity for each customer — and matching every piece of data and touchpoint to the single profile. For this to work, you need identity resolution. What is identity resolution? Identity resolution is the ongoing process of linking various identifying elements to create and expand a unique identity. The multi-step process can include: Securely onboarding data into a system Hashing or tokenizing personal information to improve security and privacy Setting aside information that can't be matched to an identity yet Matching or linking identifiers to a known unique identity Verifying that the identities and identifiers are accurate An identity graph (ID graph) is an essential part of identity resolution. It's the proprietary database that can pull in and store data from different sources and link them to a unique identifier — also known as a persistent identification number. Depending on the system and purpose, identity resolution may focus on creating a single identity for a person, household, or business. The information can come from internal sources, including a customer relationship management (CRM) tool, email marketing platforms, event management platforms, social media accounts, point-of-sales systems, and other digital and offline touchpoints. Additionally, third-party data sources, such as credit or demographic data, can contribute to building a more complete identity. And second-party data — information that's shared between brands or companies — can also be helpful. As new digital and offline information is created or found, it's linked to the existing persistent identification number in the ID graph. The process can happen in different ways. The resolution system could accurately match an engagement to a person with deterministic data, such as a hashed email address, assuming they logged in. If the person didn't log in, a probabilistic model may be able to accurately attribute the session to the person's identity based on indicators that it's likely the same person, such as a device ID or behavioral data. A hybrid approach combines deterministic and probabilistic approaches, which could be important for scaling. The goal and end result is often called a holistic, single-unified, or 360-degree view of a customer. READ MORE: Making identities personal Why does identity resolution matter? Identity resolution lets you know with whom you're connecting, which can be important throughout a customer's lifecycle. From marketing to collections, you want to be able to engage the right person on the right channel with the right offer. And that's only possible when you can accurately identify people. Consistent and accurate identity resolution is difficult, though. Experian's 2023 Identity and Fraud Report found that 92% of businesses have a strategy in place for identifying consumers online. But 63% of consumers are either "somewhat confident" or "not very confident" that businesses can accurately recognize them online. What are the benefits of identity resolution? It's a worthy goal to push toward, because you can use identity resolution solutions to: Consolidate your view of customers Companies may have multiple profiles of the same customer — one from an email list, another from their loyalty program and a third from an outdated system. Your customers are also interacting with you in different ways, perhaps logging into an account from their laptop in the morning while visiting your site from a phone at night. Identity resolution lets you connect all these elements to create a single profile. Build targeted and measurable marketing campaigns Once you have a single and consistent view of your customers, you can more accurately segment and target your marketing campaigns. Personalizing messages can increase engagement and effectiveness. And, equally important, knowing to who you don't want to send messages can help you avoid wasting marketing spending. Some identity resolution services can also help you track anonymous visitors and customize your marketing with look-alike models, which can identify people who are likely part of your target audience. You'll also be able to more accurately measure the effectiveness of a campaign. With a single customer view, it's easier to know if and how a targeted social media ad, television spot and emailed coupon worked together to create a sale. Increase customer experiences across brands When implemented throughout an organization, you can also use the single view of a customer to create a consistent experience across brands and business units. Each can benefit from a more holistic understanding of the customer and can contribute to building out customers' profiles. Seamlessly confirm identities Identity resolution can also create a more frictionless experience for customers who want to create or log into your site, and it can help with detecting fraud and high-risk consumers. But keep data security top of mind. Consumers rank privacy (79%) and security (78%) much higher than login convenience (38%) when considering their online experience. What does an identity resolution solution look like? The need for and type of identity resolution can vary depending on a business' challenges and goals. For instance, large retailers often have a lot of first-party data — so much that it may be overwhelming. For them, an identity resolution solution that can organize internal data while enhancing it with external data points could be a priority. In contrast, a business with infrequent touchpoints might not have as much first-party data and could benefit from a solution that offers as much external information as possible. Some organizations are building their own internal identity resolution services to address these challenges, but many are looking to outside partners for identity resolution. When comparing partners, consider: Flexibility and scalability: Understand which data the solution can onboard and how quickly it can onboard data. Consider whether you'll want to be able to use real-time APIs or batch processing, and the limitations on how much data the provider can process at a time. Additionally, consider whether the ID graph will use persistent IDs that can change as you scale. Matching and analysis: Ask about the solution's approach and success with matching online and offline data and the options to integrate or append second and third-party data. If you want to be able to securely and privately share anonymized identities internally or with partners, make sure that's an option as well. Integration: Research whether the provider can easily integrate your existing services and vendors. Privacy: 73% of consumers say it's a business's responsibility to protect them online. Ask about the provider's experience and approach to storing and anonymizing data. Some solutions also have built-in activation tools. These let you build and launch omni-channel campaigns. They also analyze and report on how well your campaigns are performing. Get started today To learn more about the importance of digital identity and Experian's identity solutions, visit us today. Learn more

In today’s complex business landscape, data-based decision-making has become the norm, with advanced technologies and analytics tools facilitating faster and more accurate modeling and predictions. However, with the increased reliance on models, the risk of errors has also increased, making it crucial for organizations to have a comprehensive model risk management framework. In this blog post, we will dive deeper into model risk management, its importance for organizations, and the key elements of a model risk management framework. What is model risk? First, let's define what we mean by model risk. Many institutions use models to forecast and predict the future performance of investments, portfolios or consumers' creditworthiness. Model risk can happen when the results produced by these models are inaccurate or not fit for the intended purpose. This risk arises due to several factors, like data limitations, model assumptions and inherent complexities in the underlying modeled processes. For example, in the credit industry, an inaccurately calibrated credit risk model may incorrectly assess a borrower's default risk, resulting in erroneous credit decisions and impacting overall portfolio performance. What is a risk management model and why is it important? A risk management model, or model risk management, refers to a systematic approach to manage the potential risks associated with the use of models and, more specifically, quantitative models built on data. Since models are based on a wide range of assumptions and predictions, it's essential to recognize the possibility of errors and acknowledge its impact on business decisions. The goal of model risk management is to provide a well-defined and structured approach to identifying, assessing, and mitigating risks associated with model use. The importance of model risk management for institutions that leverage quantitative risk models in their decisioning strategies cannot be overstated. Without proper risk management models, businesses are vulnerable to significant consequences, such as financial losses, regulatory enforcement actions and reputational damage. Model risk management: essential elements The foundation of model risk management includes standards and processes for model development, validation, implementation and ongoing monitoring. This includes: Policies and procedures that provide a clear framework for model use and the associated risks. Model inventory and management that captures all models used in an organization. Model development and implementation that documents the policies for developing and implementing models, defining critical steps and role descriptions. Validation and ongoing monitoring to ensure the models meet their stated objectives and to detect drift. In addition to these essential elements, a model risk management framework must integrate an ongoing system of transparency and communication to ensure that each stakeholder in model risk governance is aware of the policies, processes and decisions that support model use. Active engagement with modelers, validators, business stakeholders, and audit functions, among other stakeholders, is essential and should be included in the process. How we can help Experian® provides solutions and risk mitigation tools to help organizations of all sizes establish a solid model risk management framework to meet regulatory and model risk governance requirements, improve overall model performance and identify and mitigate potential risk. We provide services for back testing, benchmarking, sensitivity analysis and stress testing. In addition, our experts can review your organization’s current model risk management practices, conduct a gap analysis and assist with audit preparations. Learn more *This article includes content created by an AI language model and is intended to provide general information.

Online identity verification has become a basic necessity for everyday life. Consumers today might expect to upload a picture of their driver's license or answer security questions before creating a new account. And it's crucial to them — 63% say it's extremely or very important for businesses to be able to recognize them online. While many organizations have a consumer recognition strategy, moving from strategy to action and then getting the desired result isn't easy. That's particularly true when you're working to create seamless experiences for customers while fighting increasingly sophisticated fraudsters. Why is online identity verification challenging? Identity verification in the physical world might be as simple as checking a government-issued ID card — and perhaps an additional form of identification (or two) when the stakes are higher. Verification becomes more complicated as you move into the digital realm, especially when you need to automate decisions. There are many specific challenges to overcome, but some of the main ones fall into four categories. Finding the right friction: In an ideal world, every legitimate user will flow through your verification checks with ease. In reality, you may need to introduce some roadblocks to comply with know your customer (KYC) rules and prevent fraud. Finding the friction-right balance can be tricky. Accessing and using data: Using expanded data sources, such as behavior and device info, can improve outcomes without adding friction. But simply having more data isn’t the goal. You need to be able to organize, process and use the data in a compliant manner to quickly and accurately verify identities. Fighting fraud: You’re up against formidable foes who consistently test your systems for weaknesses and share the results with other fraudsters. You have to be able to spot first-party fraud, identity thieves and synthetic identities. Securing the data: Accessing and storing customer data is vital for a successful identity verification system, but it’s your responsibility to securely protect customers’ data. It also may be a legal requirement, and you need to be mindful of all the applicable regulations. These aren't fixed challenges that you can overcome in a single hurdle. Consumer preferences, fraud tactics and regulations are continually evolving, and your identity verification platform needs to keep up. Potential benefits throughout the customer lifecycle Companies that want to create, manage and continuously identify consumers are starting to take an enterprise-wide approach that relies on creating a single-customer view. The idea is to have a single identity that you can expand as you learn more about a person’s preferences and behavior. Otherwise, business units can wind up with fragmented views that lead to jumbled messaging, errors and missed opportunities. While it can be difficult to implement well, the single-view approach can also be powerful in action: Targeting and onboarding: Marketing, acquisition and onboarding aren’t necessarily handled by the same teams, but a smooth process can create a lasting good impression. There are also recent developments that can provide pre-fill capabilities with their identification verification solutions, which can create a nearly friction-free onboarding process. Prevent fraud: The single-view approach also lets you leverage cross-device and real-time data to detect and prevent fraud, and determine the right-size verification method. Using identity graphs to verify identities in real-time can also help you detect fraud, including account takeovers and first-party fraud. Customer experience: Consistently identifying customers can improve their experience — particularly when different departments can easily access and update the same identification material. In turn, this can lead to brand loyalty and the potential to upsell and cross-sell customers. The need for accurate verification is growing as people spend more time living and shopping online. Only 16% of consumers are confident businesses can consistently recognize them online, which also means there’s an opportunity to surprise and delight the skeptics. What do consumers want? Most people want to be recognized as they move throughout their digital lives. But data breaches and identity theft continuously make headlines, and people aren't ignorant of the dangers of sharing their personal information. In fact, consumers ranked identity theft (80%) as their top online security concern, a sizable +20% jump from the previous year. Finding the right balance of privacy, security and due diligence is important for earning customers' trust. However, the best approach to online identity verification may depend on who your customers are and how they interact with your products and services. Finding a great online identity verification partner Knowing how important online identity verification can be for the success of your business, you need to be sure that the digital identity solutions providers you partner with can meet your current and future needs. A good fit can: Give you access to multidimensional data: You can use online and offline data to support your digital identity verification systems. Some vendors can also help you use internal data,deterministic dataand outputs from probabilistic models to improve your results. Scale to meet future challenges: Many businesses are exploring how to use machine learning and artificial intelligencefor identity resolution and verification. These can be especially powerful when combined with robust data sources and may become more important as additional data sources come online. Protect your business: Identity verification solutions need to help you comply with the regulatory requirements and detect fraud with low false-positive rates to protect your business. First and foremost, you want to work with a partner who knows thatidentity is personal. Your customers are more than data points, and putting their needs and wants first will ultimately help you earn their trust and business. Learn more about Experian’s customer-centric identity verification solutions. Learn more

This article was updated on January 23, 2024. Sometimes you have to break from tradition and look to modern solutions to address modern problems. As consumers increasingly expect fast-paced digital experiences, lenders are tapping into advances in computing power to enhance their operations. According to a 2022 Experian study, 66% of businesses believe advanced analytics, including machine learning and artificial intelligence, are going to rapidly change the way they do business.1 While some may feel wary about trusting automated systems, remember that you're in control of the strategy. Automation comes in after to help take over monotonous and complex or error-prone tasks. As a result, you can free up resources for work that isn't as well-suited for automation, such as analyzing results and revising strategies. The benefits of automation within loan origination From initial screenings to determining a final decision or credit limit, automation can offer benefits throughout the loan origination process. And lenders of all sizes are exploring opportunities for automation to help them: Manage an overwhelming number of applications: Lenders may be struggling to respond to an increased demand for credit, particularly if they're also dealing with staffing shortages and rely on manual inputs and reviews. Automation can remove some of the burden from employees and lead to faster decisions. Increase consistency and accuracy: Transposing information from applications and making calculations by hand can result in errors or inconsistent results. Modern automated systems can help ensure information is accurate, uniform and up to date. Create scalable processes: Automated processes are easier to scale than a strategy that relies on consistent manual reviews and frequent back-and-forth with customers. Improve customers' experiences: Fast, accurate and fair decisions make for happy customers. However, 58% don't feel that businesses completely meet their expectations for their online experience.2 What's more, 91% of online applications are abandoned before completion.3 More loans, a consistent scalable process and happy customers can all drive revenue growth. When integrated throughout the underwriting journey, automation can also help you increase conversion rates and expand your lending universe without taking on more risk. What does an optimized and automated loan origination process look like? Modern loan origination software offers flexibility, security, speed and robust integrations. These can be cloud-based systems that vendors create and manage on your behalf, or lenders that have the resources and capabilities may be able to bring (or build) them in house. Strategy first Automating parts of your origination process can save you time and money, but you have to start with a specific strategy. For example, you might consider your model's outputs and decide on denial and approval cut-off points — you can then automate those approvals and denials. You can also test, revise, and optimize strategies based on your desired results. Digital applications Let consumers apply when and how they want, even if it means pausing part-way through and continuing on a different device later. Remove potentially time-consuming steps by letting consumers upload and sign documents digitally, and use AI-driven automated systems to review the documents for accuracy.4 Integration with various data sources You need good data—and lots of it—to get the most out of an automated system. Some platforms can automatically connect and use internal data alongside third-party data sources, such as alternative data, credit bureau data and credit attributes. Identity, income and fraud checks Automated platforms can work with verification tools to quickly confirm the applicant's employment and income, confirm their identity and perform fraud checks. The process can take minutes rather than days or weeks, letting you quickly move applicants through to the next stage of the process. Decisions based on optimized models Automated decision engines use your strategy and the available data to quickly return a decision. Machine learning models can score consumers who aren't scorable by traditional credit models, expanding your potential customer base while furthering financial inclusion goals. They can also more accurately score applicants and narrow the band (and potentially the number of applications) that requires manual reviews.5 Automation in action: Atlas Credit, a small-dollar lender, wanted to modernize its lending with customized and automated systems. Experian helped them build a custom machine learning credit risk model and optimized their decision strategy and cutoffs. The results exceeded Atlas Credit's goals, and the company nearly doubled their loan approval rates while decreasing risk losses by 15 to 20 percent. Explainable results Automated, fast decisions based on machine learning and AI analytics might raise some compliance flags—but we've moved beyond black box models. You need to be aware of and follow all the applicable regulations, and you can use AI and machine learning in precise ways to increase your efficiency while having fully explainable and compliant results. Experian's automated offerings build on a history of success Experian has decades of experience helping lenders make accurate and timely credit decisions, and our flexible loan origination system can help you automate originations while managing risk. It starts with good data. While we're known for our consumer credit database that has information on over 245 million consumers, Experian can also give lenders access to alternative data, including alternative financial services, rental payment data and consumer-permission data. And we know how to incorporate your internal data to create strategies that will further your specific goals. From marketing to collections, our integrated offerings can help you use the data to automate and optimize decisions across the entire customer life cycle. And whether you want to take the reins or tap our data scientists for their expertise, there are options to fit your needs. Learn more about our suite of loan origination software solutions and Experian Decisioning for originations, our automated decision engine. Learn more 1Experian (2022). Explainability: ML and AI in credit decisioning2Experian (2022). North America findings from the 2022 Decisioning Survey 3Experian (2023). eBook: The Ultimate Guide to Competitive Growth 4Ibid.5Experian (2022). Driving Growth During Economic Uncertainty with AI/ML Strategies

In today’s highly competitive landscape, credit card issuers face the challenge of optimizing portfolio profitability while also effectively managing their overall risk. Financial institutions successfully navigating the current market put more focus on proactively managing their credit limits. By appropriately assigning initial credit limits and actively overseeing current limits, these firms are improving profitability, reducing potential risk, and creating a better customer experience. But how do you get started with this important tool? Let’s explore how and why proactive credit limit management could impact your business. The importance of proactive credit limit management Enhanced profitability: Assigning the optimal credit limit that caters to a customer’s spending behavior while also considering their capacity to repay can stimulate increased credit card usage without taking on additional risk. This will generate higher transaction volumes, increase interest income, promote top-of-wallet use, and improve wallet share, all positively impacting the institution’s profitability. Mitigating risk exposure: A proactive review of the limits assigned within a credit card portfolio helps financial institutions assess their exposure to overextended credit usage or potential defaults. Knowing when to reduce a credit limit and assigning the right amount can help financial institutions mitigate their portfolio risk. Minimizing default rates: Accurately assigning the right credit limit reduces the likelihood of customers defaulting on payments. When an institution aligns their credit limits with a cardholder's financial capability, it reduces the probability of customers exceeding their spending capacity and defaulting on payments. Improving the customer experience: A regular review of a credit card portfolio can help financial institutions find opportunities to proactively increase credit limits. This reduces the need for a customer to call in and request a higher credit limit and can increase wallet share and customer loyalty. Strategies for effective credit limit management Utilizing advanced analytics: Leveraging machine learning models and mathematically optimized decision strategies allows financial institutions to better assess risk and determine the optimal limit assignment. By analyzing spending patterns, credit utilization, and repayment behavior, institutions can dynamically adjust credit limits to match evolving customer financial profiles. Regular review and adjustments: As part of portfolio risk management, implementing a system for a recurring review and adjustment of credit limits is crucial. It ensures that credit limits are still aligned with the customer's financial situation and spending habits, while also reducing the risk of default. Customization and flexibility: Personalized credit limits tailored to individual customer needs improve customer satisfaction and loyalty. Proactively increasing limits based on improved creditworthiness or income reassessment can foster stronger customer relationships. Protect profitability and control risk exposure Using the right data analytics, processing regular reviews, and customizing limits to individual customer needs helps reduce risk exposure while maximizing profitability. As the economic landscape evolves, institutions that prioritize proactive credit limit management will gain a competitive edge by fostering responsible customer spending behavior, minimizing default rates, and optimizing their bottom line. With Experian, automating your credit limit management process is easy Experian’s Ascend Intelligence ServicesTM Limit provides you with the optimal credit limits at the customer level to generate a higher share of plastic spend, reduce portfolio risk, and proactively meet customer expectations. Let us help automate your credit limit management process to better serve your customers and quickly respond to the volatile market. To find out more, please visit our website. Ready for a demo? Contact us now!

It is a New Year and a new start. How about a new job? That is what thousands of employees will consider over the next month. It is also a time for employers to attract new talents, but they must be aware of different types of employment fraud. The rise of remote work has significantly increased the prevalence of remote hiring practices, from the initial job application to the onboarding process and beyond. Unfortunately, this shift has also opened the door to a surge in imposter employees, also known as ‘candidate fraud,’ posing a significant concern for organizations. How does employment identity theft happen? Instances of potential job candidates utilizing real-time deepfake video and deepfake audio, along with personally identifiable information (PII), during remote interviews to secure positions within American companies have been on the rise. The Federal Bureau of Investigation (FBI) reports that fraudulent individuals often acquire PII through fake job opening posts, which enable them to gather candidate information and resumes. Surprisingly, the tools necessary for impersonation on live video calls do not require sophisticated or expensive hardware or software. Employment identity theft can occur in several ways. Here are a few examples: Inaccurate credentials: Employers may inadvertently hire someone with false or stolen credentials if they fail to conduct comprehensive background checks. When the employer discovers the deception, it can be challenging to trace the true identity of the person they unknowingly hired. Limited-term job offers: Some industries offer temporary job opportunities in distant locations. Individuals with criminal backgrounds may steal victims' identities to apply for these jobs, hoping that their crimes will go unnoticed until after the job is complete. Perpetrated by colleagues: In rare instances, jealous colleagues or coworkers can commit employment identity theft. They may steal a coworker's information during a data breach and sell it on the dark web or use the victim's credentials to frame them for fraudulent workplace actions. Preventing employment identity theft In addition to the reported cases of imposter employee fraud, it is crucial to acknowledge the potential for other scams that exploit new technologies and the prevalence of remote work. Malicious cyber attackers could secure employment using stolen credentials, enabling them to gain unauthorized access to sensitive data or company systems. A proficient hacker possessing the necessary IT skills may find it relatively easy to leverage social engineering techniques during the hiring process. Consequently, the reliability of traditional methods for employee verification, such as face-to-face interactions and personal recognition, is diminishing in the face of remote work and the technological advancements that enable individuals to manipulate their appearance, voice, and identity. To mitigate risks associated with hiring imposters, it is imperative to incorporate robust measures into the recruitment process. Here are some key considerations: Establish clear policies and employment contracts: Clearly communicate your organization's policies regarding moonlighting in employment contracts, employee handbooks, or other official documents. Confidentiality and non-compete agreements: Implement confidentiality and non-compete agreements to protect your company's sensitive information and intellectual property. Monitoring: Automate employment and income verification of your employees. Provide training on cybersecurity best practices: Educate employees about cyber-attacks and identity scams, such as phishing scams, through seminars and workplace training sessions. Implement robust security measures: Use firewalls, encrypt sensitive employee information, and limit access to personal data. Minimize the number of employees who have access to this information. Thoroughly screen new employees: Verify the accuracy of Social Security numbers and other information during the hiring process. Conduct comprehensive background checks, including checking bank account information and credit reports and fight against synthetic identities. Offer identity theft protection as a benefit: Consider providing identity theft protection services to your employees as part of their benefits package. These services can detect and alert victims of potential identity theft, facilitating a fast response. The new era of remote work necessitates a fresh perspective on the hiring process. It is crucial to reevaluate HR practices and leverage AI fraud detection technologies to ensure that the individuals you hire, and employ are who they claim to be, guarding against the infiltration of imposters. Navigating employment fraud with effective solutions Employment fraud presents significant risks and challenges for employers, including conflicts of interest, reputation damage, and breaches of confidentiality. By taking the right preventative measures, you can safeguard your organization and employees. Streamlining the hiring process is essential to remain competitive. But how do you balance the need for speed and ease of use with essential ID checks? By combining the best data with our automated ID verification processes, Experian helps you protect your business and onboard new talents efficiently. Our best-in-class solutions employ device recognition, behavioral biometrics, machine learning and global fraud databases to spot and block suspicious activity before it becomes a problem. Learn more about preventing employement fraud *This article includes content created by an AI language model and is intended to provide general information.

Model explainability has become a hot topic as lenders look for ways to use artificial intelligence (AI) to improve their decision-making. Within credit decisioning, machine learning (ML) models can often outperform traditional models at predicting credit risk. ML models can also be helpful throughout the customer lifecycle, from marketing and fraud detection to collections optimization. However, without explainability, using ML models may result in unethical and illegal business practices. What is model explainability? Broadly defined, model explainability is the ability to understand and explain a model's outputs at either a high level (global explainability) or for a specific output (local explainability).1 Local vs global explanation: Global explanations attempt to explain the main factors that determine a model's outputs, such as what causes a credit score to rise or fall. Local explanations attempt to explain specific outputs, such as what leads to a consumer's credit score being 688. But it's not an either-or decision — you may need to explain both. Model explainability can also have varying definitions depending on who asks you to explain a model and how detailed of a definition they require. For example, a model developer may require a different explanation than a regulator. Model explainability vs interpretability Some people use model explainability and interpretability interchangeably. But when the two terms are distinguished, model interpretability may refer to how easily a person can understand and explain a model's decisions.2 We might call a model interpretable if a person can clearly understand: The features or inputs that the model uses to make a decision. The relative importance of the features in determining the outputs. What conditions can lead to specific outputs. Both explainability and interpretability are important, especially for credit risk models used in credit underwriting. However, we will use model explainability as an overarching term that encompasses an explanation of a model's outputs and interpretability of its internal workings below. ML models highlight the need for explainability in finance Lenders have used credit risk models for decades. Many of these models have a clear set of rules and limited inputs, and they might be described as self-explanatory. These include traditional linear and logistic regression models, scorecards and small decision trees.3 AI analytics solutions, such as ML-powered credit models, have been shown to better predict credit risk. And most financial institutions are increasing their budgets for advanced analytics solutions and see their implementation as a top priority.4 However, ML models can be more complex than traditional models and they introduce the potential of a “black box." In short, even if someone knows what goes into and comes out of the model, it's difficult to explain what's happening without an in-depth analysis. Lenders now have to navigate a necessary trade-off. ML-powered models may be more predictive, but regulatory requirements and fair lending goals require lenders to use explainable models. READ MORE: Explainability: ML and AI in credit decisioning Why is model explainability required? Model explainability is necessary for several reasons: To comply with regulatory requirements: Decisions made using ML models need to comply with lending and credit-related, including the Fair Credit Reporting Act (FCRA) and Equal Credit Opportunity Act (ECOA). Lenders may also need to ensure their ML-driven models comply with newer AI-focused regulations, such as the AI Bill of Rights in the U.S. and the E.U. AI Act. To improve long-term credit risk management: Model developers and risk managers may want to understand why decisions are being made to audit, manage and recalibrate models. To avoid bias: Model explainability is important for ensuring that lenders aren't discriminating against groups of consumers. To build trust: Lenders also want to be able to explain to consumers why a decision was made, which is only possible if they understand how the model comes to its conclusions. There's a real potential for growth if you can create and deploy explainable ML models. In addition to offering a more predictive output, ML models can incorporate alternative credit data* (also known as expanded FCRA-regulated data) and score more consumers than traditional risk models. As a result, the explainable ML models could increase financial inclusion and allow you to expand your lending universe. READ MORE: Raising the AI Bar How can you implement ML model explainability? Navigating the trade-off and worries about explainability can keep financial institutions from deploying ML models. As of early 2023, only 14 percent of banks and 19 percent of credit unions have deployed ML models. Over a third (35 percent) list explainability of machine learning models as one of the main barriers to adopting ML.5 Although a cautious approach is understandable and advisable, there are various ways to tackle the explainability problem. One major differentiator is whether you build explainability into the model or try to explain it post hoc—after it's trained. Using post hoc explainability Complex ML models are, by their nature, not self-explanatory. However, several post hoc explainability techniques are model agnostic (they don't depend on the model being analyzed) and they don't require model developers to add specific constraints during training. Shapley Additive Explanations (SHAP) is one used approach. It can help you understand the average marginal contribution features to an output. For instance, how much each feature (input) affected the resulting credit score. The analysis can be time-consuming and expensive, but it works with black box models even if you only know the inputs and outputs. You can also use the Shapley values for local explanations, and then extrapolate the results for a global explanation. Other post hoc approaches also might help shine a light into a black box model, including partial dependence plots and local interpretable model-agnostic explanations (LIME). READ MORE: Getting AI-driven decisioning right in financial services Build explainability into model development Post hoc explainability techniques have limitations and might not be sufficient to address some regulators' explainability and transparency concerns.6 Alternatively, you can try to build explainability into your models. Although you might give up some predictive power, the approach can be a safer option. For instance, you can identify features that could potentially lead to biased outcomes and limit their influence on the model. You can also compare the explainability of various ML-based models to see which may be more or less inherently explainable. For example, gradient boosting machines (GBMs) may be preferable to neural networks for this reason.7 You can also use ML to blend traditional and alternative credit data, which may provide a significant lift — around 60 to 70 percent compared to traditional scorecards — while maintaining explainability.8 READ MORE: Journey of an ML Model How Experian can help As a leader in machine learning and analytics, Experian partners with financial institutions to create, test, validate, deploy and monitor ML-driven models. Learn how you can build explainable ML-powered models using credit bureau, alternative credit, third-party and proprietary data. And monitor all your ML models with a web-based platform that helps you track performance, improve drift and prepare for compliance and audit requests. *When we refer to “Alternative Credit Data," this refers to the use of alternative data and its appropriate use in consumer credit lending decisions, as regulated by the Fair Credit Reporting Act. Hence, the term “Expanded FCRA Data" may also apply and can be used interchangeably. 1-3. FinRegLab (2021). The Use of Machine Learning for Credit Underwriting 4. Experian (2022). Explainability: ML and AI in credit decisioning 5. Experian (2023). Finding the Lending Diamonds in the Rough 6. FinRegLab (2021). The Use of Machine Learning for Credit Underwriting 7. Experian (2022). Explainability: ML and AI in credit decisioning 8. Experian (2023). Raising the AI Bar

Meeting Know Your Customer (KYC) regulations and staying compliant is paramount to running your business with ensured confidence in who your customers are, the level of risk they pose, and maintained customer trust. What is KYC?KYC is the mandatory process to identify and verify the identity of clients of financial institutions, as required by the Financial Conduct Authority (FCA). KYC services go beyond simply standing up a customer identification program (CIP), though that is a key component. It involves fraud risk assessments in new and existing customer accounts. Financial institutions are required to incorporate risk-based procedures to monitor customer transactions and detect potential financial crimes or fraud risk. KYC policies help determine when suspicious activity reports (SAR) must be filed with the Department of Treasury’s FinCEN organization. According to the Federal Financial Institutions Examinations Council (FFIEC), a comprehensive KYC program should include:• Customer Identification Program (CIP): Identifies processes for verifying identities and establishing a reasonable belief that the identity is valid.• Customer due diligence: Verifying customer identities and assessing the associated risk of doing business.• Enhanced customer due diligence: Significant and comprehensive review of high-risk or high transactions and implementation of a suspicious activity-monitoring system to reduce risk to the institution. The following organizations have KYC oversight: Federal Financial Institutions Examinations Council (FFIEC), Federal Reserve Board, Federal Deposit Insurance Corporation (FDIC), national Credit Union Administration (NCUA), Office of the Comptroller of the Currency (OCC) and the Consumer Financial Protection Bureau (CFPB). How to get started on building your Know Your Customer checklist 1. Define your Customer Identification Program (CIP) The CIP outlines the process for gathering necessary information about your customers. To start building your KYC checklist, you need to define your CIP procedure. This may include the documentation you require from customers, the sources of information you may use for verification and the procedures for customer due diligence. Your CIP procedure should align with your organization’s risk appetite and be comply with regulations such as the Patriot Act or Anti-money laundering laws. 2. Identify the customer's information Identifying the information you need to gather on your customer is key in building an effective KYC checklist. Typically, this can include their first and last name, date of birth, address, phone number, email address, Social Security Number or any government-issued identification number. When gathering sensitive information, ensure that you have privacy and security controls such as encryption, and that customer data is not shared with unauthorized personnel. 3. Determine the verification method There are various methods to verify a customer's identity. Some common identity verification methods include document verification, facial recognition, voice recognition, knowledge-based authentication, biometrics or database checks. When selecting an identity verification method, consider the accuracy, speed, cost and reliability. Choose a provider that is highly secure and offers compliance with current regulations. 4. Review your checklist regularly Your KYC checklist is not a one and done process. Instead, it’s an ongoing process that requires periodic review, updates and testing. You need to periodically review your checklist to ensure your processes are up to date with the latest regulations and your business needs. Reviewing your checklist will help your business to identify gaps or outdated practices in your KYC process. Make changes as needed and keep management informed of any changes. 5. Final stage: quality control As a final step, you should perform a quality control assessment of the processes you’ve incorporated to ensure they’ve been carried out effectively. This includes checking if all necessary customer information has been collected, whether the right identity verification method was implemented, if your checklist matches your CIP and whether the results were recorded correctly. KYC is a vital process for your organization in today's digital age. Building an effective KYC checklist is essential to ensure compliance with regulations and mitigate risk factors associated with fraudulent activities. Building a solid checklist requires a clear understanding of your business needs, a comprehensive definition of your CIP, selection of the right verification method, and periodic reviews to ensure that the process is up to date. Remember, your customers' trust and privacy are at stake, so iensuring that your security processes and your KYC checklist are in place is essential. By following these guidelines, you can create a well-designed KYC checklist that reduces risk and satisfies your regulatory needs. Taking the next step Experian offers identity verification solutions as well as fully integrated, digital identity and fraud platforms. Experian’s CrossCore & Precise ID offering enables financial institutions to connect, access and orchestrate decisions that leverage multiple data sources and services. By combining risk-based authentication, identity proofing and fraud detection into a single, cloud-based platform with flexible orchestration and advanced analytics, Precise ID provides flexibility and solves for some of financial institutions’ biggest business challenges, including identity and fraud as it relates to digital onboarding and account take over; transaction monitoring and KYC/AML compliance and more, without adding undue friction. Learn more *This article includes content created by an AI language model and is intended to provide general information.

The online gaming industry has experienced tremendous growth in recent years, with millions of players engaging in immersive virtual worlds and competitive gameplay. Unfortunately, this surge in popularity has also sparked an increase in online gaming fraud. Unscrupulous individuals have sought to exploit the industry through fraudulent activities, leading to financial losses and reputational damage for gaming vendors.According to a recent study conducted by Lloyds Bank, children are spending more time playing online games than ever before – over five million children between the ages of three and 15 are now regularly playing games online, up from approximately 4.6 million in 2019.Fraudsters, always ready to take advantage of opportunities presented by new trends, are now increasingly targeting this rising demographic. Gaming vendors have a responsibility to shield minors from fraud in online gaming by implementing robust safety measures, educating young players and their parents, and actively monitoring and addressing fraudulent activities. A vulnerable target That same study from Lloyds revealed that over a third (36%) of parents are concerned about the possibility of their children falling victim to gaming fraud and losing money. In today's tech-savvy world, the ease of payment authorization has only exacerbated these concerns. All it takes for a child to make a payment is to key in their parents' online store username and password. It is a practice fraught with danger. Parents can only do so much to safeguard their children while gaming, and despite their best efforts, there will always remain a lingering possibility of encountering scammers. Gaming vendors should establish robust age verification processes during account creation to ensure that minors are not exposed to age-inappropriate content. Additionally, they should incorporate comprehensive parental controls that allow parents to regulate their children's online activities, including chat limitations, spending controls, and access to certain features.But contrary to common assumptions, the gaming population is not restricted to teenagers or young adults. With an average age of 35, gamers have significant purchasing power and actively participate in the gaming ecosystem. They spend an average of over six hours per week gaming, dedicating nearly an hour each day to their preferred gaming experiences. This engagement is spread across all age groups and financial profiles, making the gaming community a vast market to attract cybercrime. Types of fraud in online gaming In 2022, the revenue from the worldwide gaming market was estimated at almost 347 billion U.S. dollars, with the mobile gaming market generating an estimated 248 billion U.S. dollars of the total. The gaming market is constantly evolving, and technological advancements are opening new possibilities for game developers to create more immersive and engaging experiences.But alarming reports indicate that scammers have honed in on the younger demographic of gamers, leveraging their innocence to exploit their finances and identities. Identity theft (67%) and hacking (61%) rank as the two most prevalent forms of fraud experienced by young gamers, according to the Lloyds Bank study. Here are some different types of online gaming fraud: Account hacking: Hackers employ various techniques like phishing, keylogging, and credential stuffing to gain unauthorized access to players' accounts. Once compromised, accounts could be used for fraudulent activities, including unauthorized in-game transactions or selling virtual assets for real money. Chargeback fraud: This occurs when players make legitimate purchases within a game using real money and then issue chargebacks, falsely claiming that the transaction was unauthorized or fraudulent. This results in financial losses for gaming vendors as they lose the revenue and virtual goods/services provided to the player. Virtual asset fraud: Virtual assets, such as in-game currency, items, or characters, hold economic value. Fraudsters engage in scams involving fake virtual asset transactions or market manipulation, exploiting players' desires to acquire rare or high-value items. Match-fixing and cheating: Competitive gaming is at the heart of many online games. Fraudsters seek to manipulate matches, exploit glitches, or use cheat software to gain an unfair advantage over others. This undermines the integrity of the gaming experience and discourages fair competition. The game changer for online platforms: fraud prevention strategies Given the anticipated growth of these threats in the foreseeable future, it is imperative that online platforms prioritize the protection of young gamers and their parents. In line with the enhanced safeguards and anti-fraud initiatives observed in banks and financial institutions, it is high time for game companies to elevate their security and consumer protection measures by adopting the following guidelines: Implement strong account security measures: Encourage players to create unique, complex passwords, and consider implementing multifactor authentication solutions. Regularly educate players about common hacking techniques and promote safe browsing habits to prevent phishing attempts. Utilize fraud detection systems: Invest in advanced fraud detection tools that employ machine learning algorithms and biometrics templates to identify suspicious activities and patterns. These systems can flag potentially fraudulent transactions, allowing you to take appropriate measures promptly. Monitor and analyze user behavior: Keep an eye on players' activities and digital identity, such as unusual login patterns, high-value transactions, or frequent chargebacks. Analyze gameplay data, interactions, and purchasing behavior to identify patterns indicative of fraud or cheating. Secure payment processing systems: Choose reputable payment gateways that prioritize security measures. Employ tokenization and encryption technologies to safeguard players' payment information during transactions. Regularly test and update your payment system's security infrastructure. Raise player awareness: Educate your player community about common fraud techniques and the importance of securing their accounts with identity authentication. Share security tips through newsletters, blog posts, and in-game messaging. Foster a culture of vigilance and encourage players to report any suspicious activities. Foster fair gameplay and zero tolerance policy: Implement robust anti-cheat measures and regularly update your game to address vulnerabilities and exploits. Promote fair competition and enforce a zero-tolerance policy against cheating, match-fixing, and other forms of unfair gameplay. Leveling-up Ultimately, the ability to protect players online could be the ultimate gamechanger for gaming platforms. By embracing identity verification mechanisms that rely on secure and privacy-centric facial recognition, online fraud and identity theft can be significantly curtailed. Moreover, the verification and onboarding processes can be streamlined, simplifying the user experience further. Just as bringing top-tier games on board is crucial, game platforms must ensure their customers engage in a secure gaming environment. Streamlining the onboarding and sign-in process is essential to remain competitive. But how do you balance the need for speed and ease of use with essential ID checks? By combining the best data with our automated ID verification checks, Experian helps you safeguard your business and onboard customers efficiently. Using passive, invisible checks when customers sign into their accounts helps to keep fraudsters at bay and protects legitimate players without the need for irritating security challenges. Experian’s best-in-class solutions employ device recognition, behavioral biometrics, machine learning and global fraud databases to spot and block suspicious activity before it becomes a problem. Learn more *This article leverages/includes content created by an AI language model and is intended to provide general information.

Fraud is a serious concern for everyone, including businesses and individuals. In fact, according to our 2023 U.S. Identity and Fraud Report, nearly two-thirds (64%) of consumers are very or somewhat concerned with online security, and over 50% of businesses have a high level of concern about fraud risk. The fraud landscape is constantly evolving, and staying vigilant against the latest trends is critical to safeguarding your organization and consumers. As we reflect on 2023, let’s look at the top fraud trends and their continued potential impact on your business. The evolution of new fraud trends When economic uncertainty reigns, a rise in fraud often follows. To begin with, consumers tend to be financially stressed in such periods and prone to making risky decisions. In addition, fraudsters are keenly aware of the opportunities inherent in unstable times and develop tactics to take advantage of them. For example, as consumers rein in spending and financial institutions struggle to maintain new account volumes, fraudsters might ramp up their new account and loan activities. Fraud is becoming more sophisticated. For instance, thanks to the rapid rise in the availability of artificial intelligence (AI) tools, fraudsters are increasingly able to impersonate companies and individuals with ease, as well as consolidate data from diverse sources and use it more efficiently. The most impactful fraud trends of 2023 The fraud trends that emerged in 2023 were diverse, though they all had one thing in common: fraudsters' keen ability to take advantage of new technologies and opportunities. And businesses are feeling the repercussions, with nearly 70% reporting that fraud losses have increased in recent years. Here are five trends we forecasted in the fraud and identity space that challenged fraud fighters on the front lines this year. Deposit and checking account fraud With everyone focused on fraud in the on-line channels, it is interesting that financial institutions reported more fraud occurring at brick-and-mortar locations. Preying on the good nature of helpful branch employees, criminals are taking risks by showing up in person to open accounts, pass bad deposits and try to work their way into other financial products. The Treasury Department reports complaints doubling YoY, after increasing more than 150% between 2020 and 2021. Synthetic identity fraud Not quite fake, not quite real, so-called synthetic or "Frankenstein" identities mash up real data with false information to create unique customer profiles that can outsmart retailers' or financial institutions' fraud control systems. With synthetic identity (SID) fraud real data is often stolen or purchased on the dark web and combined with other information — even Artificial Intelligence (AI)-created faces — so that fraudsters can build up a synthetic identity's credit score before taking advantage of them to borrow and spend money that will never be paid back. One major risk? As fraud rates rise due to the use of tactics like synthetic identities, it could become more challenging and expensive to access credit. Fake job postings and mule schemes Well-paying remote work was in high demand this year, creating opportunities for fraudsters to create fake jobs to harvest data such as Social Security numbers from unsuspecting applicants. Experian also predicts a continued rise in "mule" jobs, in which workers unknowingly sign on to do illegal work, such as re-shipping stolen goods. According to the Better Business Bureau, an estimated 14 million people get caught in a fake employment scam yearly. Job seekers can protect themselves by being skeptical of jobs that ask them to do work that appears suspicious, requires money, financial details, or personal information upfront. Peer-to-peer payment fraud Peer-to-peer payment tools are increasingly popular with consumers and fraudsters, who appreciate that they're both instant and irreversible. Experian expects to continue to see an increase in fraudulent activity on these payment systems, as fraudsters use social engineering techniques to deceive consumers into paying for nonexistent merchandise or even sharing access credentials. Stay safe while using peer-to-peer payment tools by avoiding common scams like requests to return accidental payments, opting for payment protection whenever possible and choosing other transaction methods like paying with a credit card. Social media shopping fraud Social media platforms are eager to make in-app shopping fun and friction-free for consumers — and many brands and shoppers are keen to get on board. In fact, approximately 58% of users in the U.S. have purchased a product after seeing it on social media. Unfortunately, these tools neglect effective identity resolution and fraud prevention, leaving sellers vulnerable to fraudulent purchases. And while buyers have some recourse when a purchase turns out to be a scam, it's wise to be cautious while shopping on social media platforms by researching sellers, only using credit cards and being cognizant of common scams, like when vendors on Facebook Marketplace ask for payment upfront. Employer text fraud Fraudulent text messages — also known as “smishing,” a mash-up of Short Messaging Service (SMS) and phishing — continues to rise. In fact, according to data security company Lookout, 2022 was the biggest year ever for such mobile phishing attacks, with more than 30 percent of personal and enterprise mobile phone users exposed every quarter. One modern example of these types of schemes? Expect to continue to see a rise in gift card fraud targeting companies. For example, an employee might receive a text from their "boss" asking them to purchase gift cards and relay the numbers. The fraudsters get to shop, and the company is left with the bill. Why fraud prevention and detection solutions matter Nearly two-thirds of consumers say they are "very" or "somewhat concerned" with online security, and more than 85 percent expect businesses to respond to their identity and fraud concerns. Addressing and preventing fraud — and communicating these fraud-prevention actions to customers — is an essential strategy for businesses that want to maintain customer trust, thereby decreasing churn and maximizing conversions on new leads. There's a financial imperative to address fraud as well. Businesses stand to lose a great deal of money without adequate fraud prevention strategies. Account takeover fraud, for example, is an increasing threat to financial institutions, which saw a 90 percent increase in account takeover losses from 2020 to 2021. By making account takeover fraud prevention a priority, financial institutions can alleviate risks and prevent major losses. How to build an effective fraud strategy in 2024 In 2024, fraud management solutions must be even more technically advanced than the fraudulent techniques they're combating. But more than that, they need to be appealing to consumers, who are likely to abandon signup or purchase attempts when they become too onerous. In fact, 37% of consumers have moved their business elsewhere due to a negative account opening experience. Worryingly for businesses, this number was even higher among high-income households and those aged 25 to 39. To succeed, effective fraud strategies must be seamless, low friction, data-driven and customer-focused. That means making use of up-to-date technologies that boost security while prioritizing a positive customer experience. Concerned about fraud? Let Experian help As we look back at the top fraud trends of 2023, it's clear that scammers are becoming increasingly sophisticated in their methods. Fraud can create huge risks for your business — but there are ways to act. Experian's suite of fraud prevention and identity verification tools can help you detect and combat fraud. Find out more about Experian's fraud risk management strategies and how they can help keep you and your customers safe. Learn more

Financial institutions are under increasing pressure to grow deposits and onboard more demand deposit accounts (DDA). But as demand increases, so do fraud attempts from scammers. While a robust mitigation effort is needed to stop fraud, this same effort can also drive away potential clients. In fact, 37 percent of U.S. adults said that they abandoned opening an account online due to experiencing friction. This leaves institutions in a unique quandary: how do they stop DDA fraud without scaring away potential clients? The answer lies in utilizing robust, machine learning tools that can help you navigate fraud attempts without increasing onboarding friction. Chris Ryan, Go to Market Lead for Experian Identity and Fraud, shares his thoughts on demand deposit account fraud and which decisioning tools can best combat it. Q: What is a demand deposit account and how is it used? "Demand deposit is just your basic checking account," Ryan explains." The funds are deposited and held by an institution, which enables you to spend those assets or resources, whether it be through checks, debit cards, person-to-person, Automated Clearing House (ACH) — all the things we do every day as consumers to manage our operating budget." Q: What is demand deposit account fraud? "There are two different ways that demand deposit account fraud works," Ryan says. "One is with existing account holders, and the other is with the account opening process.” When fraud affects existing account holders, it typically involves tricking an account holder into sending money to a scammer or using fraudulent actions, like phishing emails or credit card skimmers, to gain access to their accounts. There is also a resurgence in fraud involving duplication, theft and forgery of paper checks, Ryan explains. Fraud impacting the account opening process occurs when scammers originate new DDAs. This can work in a variety of ways, such as these three examples: A scammer steals your identity and opens an account at the same bank where you have a home equity loan. They link their DDA to your line of credit, transferring your money into their new account and withdrawing the funds. A scammer uses a synthetic identity (SID) to open a fraudulent DDA. They will then use this new DDA to open more lucrative accounts that the institution cross-sells to them. A scammer uses a stolen or SID to open “mule” accounts to receive funds they dupe consumers into sending through fake relationship schemes, bogus merchandise sales and dozens of similar scams. While both types of fraud need to be dealt with, account opening fraud can have especially large repercussions for lenders or financial institutions. Q: What are the consequences of DDA fraud for organizations? "Fraud hurts in a number of ways," Ryan explains. "There are direct losses, which is the money that criminals take from our financial system. Under most circumstances, the financial institution replaces the money, so the consumer doesn’t absorb the loss, but the money is still gone. That takes money away from lending, community engagement and other investments we want banks to make. The direct losses are what most people focus on." But there are even more repercussions for institutions beyond losing money, and this can include the attempts that institutions put into place to stop the fraud. "Preventing fraud requires some friction for the end consumer," Ryan says. "The volume of fraudulent attempts is overwhelmingly large in the DDA space. This forces institutions to apply more friction. The friction is costly, and it often drives would-be-customers away. The results include high costs for the institutions and low booking rates. At the same time, institutions are hungry for deposit money right now. So, it's kind of a perfect storm." Q: What is the impact of DDA fraud on customer experience? Experian’s 2023 Identity and Fraud Report revealed that up to 37 percent of U.S. adults in the survey had abandoned a new account entirely in the previous six months because of the friction they encountered during onboarding. And 51 percent reported considering abandoning the process because of problems they encountered. Unfortunately, fraud mitigation and deposit fraud detection efforts can end up driving customers away. "People can be impatient," Ryan says, "and in the online world, a competing product is a mouse-click away. So, while it is tempting to ask new applicants for more information, or further proof of identity, that conflicts with their need for convenience and can impact their experience.” Companies looking for cheap and fast mitigation can end up impeding customers trying to onboard to sweep out the bad actors, Ryan explains. "How do you get the bad people without interrupting the good people?" Ryan asks. "That's the million-dollar question." Q: What are some other problems with how organizations traditionally combat DDA fraud? Unfortunately, traditional attempts to combat DDA fraud are inefficient due to the fragmentation of technology. Ryan says this was revealed by Liminal, an industry analyst think tank. "Nearly half of institutions use four-or-more-point solutions to manage identity and fraud-related risk," Ryan explains. "But all of those point solutions were meant to work on their own. They weren't developed to work together. So, there's a lot of overlap. And in the case of fraud, there's a high likelihood that the multiple solutions are going to find the same fraud. So, you create a huge inefficiency." To solve this challenge, institutions need to shift to integrated identity platforms, such as Experian CrossCore®. Q: How is Experian trying to change the way organizations approach DDA fraud? Experian is pushing a paradigm shift for institutions that will increase fraud detection efficiency and accuracy, without sacrificing customer experience. "Organizations need to start thinking of identity through a different lens," Ryan says. Experian has developed an identity graph that aggregates consumer information in a manner that reaches far beyond what an institution can create on its own. "Experian is able to bring the entire breadth of every identity presentation we see into an identity graph," Ryan says. "It's a cross-industry view of identity behavior." This is important because people who commit fraud manipulate data, and those manipulations can get lost in a busy marketplace. For example, Ryan explains, if you're newly married, you may have recently presented your identity using two different surnames: one under your maiden name and one under your married name. Traditional data sources may show that your identity was presented twice, but they won’t accurately reflect the underlying details; like the fact that different surnames were used. The same holds true for thousands of other details seen at each presentation but not captured in a way that enables changes over time to be visible, such as information related to IP addresses, email accounts, online devices, or phone numbers. "Our identity graph is unlocking the details behind those identity presentations," Ryan says. "This way, when a customer comes to us with a DDA application, we can say, 'That's Chris's identity, and he's consistently presenting the same information, and all that underlying data remains very stable.'" This identity graph, part of Experian's suite of fraud management solutions — also connects unique identity details to known instances of fraud, helping catch fraudulent attempts much faster than traditional methods. "Let's say you and your spouse share an address, phone numbers, all the identity details that married couples typically share," Ryan explains. "If an identity thief steals your identity and uses it along with a brand-new email and IP address not associated with your spouse, that might be concerning. However, perhaps you started a new job, and the email/IP data is legitimate. Or maybe it’s a personal email using a risky internet service provider that shares a format commonly used by a known ring of identity thieves. Traditional data might flag the email and IP information as new, but our identity graph would go several layers deeper to confirm the possible risks that the new information brings. Q: Why is this approach superior to traditional methods of fraud detection? "Historically, organizations were interested in whether an identity was real,” Ryan says. "The next question was if the provided data (I.e., addresses, date of birth, Social Security numbers, etc.) have been historically associated with the identity. Last, the question would be whether there’s known risk associated with any of the identity components.” The identity graph turns that approach upside down. "The identity graph allows us to pull in insights from past identity presentations, " Ryan says. "Maybe the current presentation doesn’t include a phone number. Our identity graph should still recognize previously provided phone numbers and the risks associated with them. Instead of looking at identity as a small handful of pieces of data that were given at the time of the presentation, we use the data given to us to get to the identity graph and see the whole picture." Q: How are businesses applying this new paradigm? The identity graph is part of Experian's Ascend Fraud Platform™ and a full suite of fraud management solutions. Experian's approach allows companies to clean out fraud that already occurred and stop new fraudulent actors before they're onboarded. "Ideally, you want to start with cleaning up the house, and then figure out how to protect the front door," Ryan says. In other words, institutions can start by applying this view to recently opened accounts to identify problematic identities that they missed. The next step would be to bring these insights into the new account onboarding process. Q: Is this new fraud platform accessible to both small and large businesses? The Ascend Fraud Platform will support several use cases that will bring value to a broad range of businesses, Ryan explains. It can not only enable Experian experts to build and deliver better tools but can enable self-serve analytical development too. "Larger organizations that have robust, internal data science capabilities will find that it’s an ideal environment for them to work in," Ryan says. "They can add their own internal data assets to ours, and then have a better place to develop analytics. Today, organizations spend months assembling data to develop analytics internally. Our Ascend Fraud Platform will reduce the timeline of the data assembly and analytical development process to weeks, and speed to market is critical when confronting continually changing fraud threats. "But for customers who have less robust analytical teams, we're able to do that on their behalf and bring solutions out to the marketplace for them," Ryan explains. Q: What type of return on investment (ROI) are businesses experiencing? "Some customers recover their investment in days," Ryan says. "Part of this is from mitigating fraud risks among recently opened accounts that slipped through existing defenses.” "In addition to reducing losses, institutions we're working with are also seeing potentially millions of dollars a month in additional bookings, as well as significant cost savings in their account opening processes," Ryan says. "We're able to help clients go back and audit the people who had fallen out of their process, to figure out how to fine-tune their tools to keep those people in," Ryan says. “By reducing risks among existing accounts, better protecting the front door against future fraud, and growing more efficiently, we’re helping clients Q: What are Experian's plans for this service? "We're working with top-tier financial institutions on the do-it-yourself techniques," Ryan says. "In parallel, we're launching our first offerings that are created for the broader marketplace. That will start with the portfolio review capability, along with making the most predictive attributes available through our integrated identity resolution platform. And while the Ascend Fraud Platform has a strong use case for DDA fraud, its uses extend beyond that to small business lending and other products. In fact, Experian offers an entire suite of fraud management solutions to help keep your DDA accounts secure and your customers happy. Experian can help optimize your DDA fraud detection Experian is revolutionizing the approach to combating DDA fraud, helping institutions create a faster onboarding process that retains more customers, while also stopping more bad actors from gaining access. It's a win-win for everyone. Experian's full suite of fraud management solutions can optimize your business's DDA fraud detection, from scrubbing your current portfolio to gatekeeping bad actors before they're onboarded. Learn more Speak with a specialist About our expert: Chris Ryan has over 20 years of experience in fraud prevention and uses this knowledge to identify the most critical fraud issues facing individuals and businesses in North America, and he guides Experian’s application of technology to mitigate fraud risk.

In today's fast-paced digital world, the risk of fraud across all industries is a constant threat. The traditional methods of fraud detection are no longer sufficient, as fraudsters become increasingly sophisticated in their attacks. However, with artificial intelligence (AI) and machine learning (ML) solutions, financial institutions can stay one step ahead of fraudsters. AI and machine learning-equipped fraud detection tools have the ability to identify suspicious activity and patterns of fraud that are imperceptible to the human brain. In this blog post, we’ll dive into the significance of AI and machine learning in fraud detection and how these solutions are uniquely equipped to handle the demands of modern-day risk management. Understanding artificial intelligence and machine learning AI and machine learning solutions are transformative technologies that are reshaping the landscape of many industries. AI, at its core, is a field of computer science that simulates human intelligence in machines, enabling them to learn from experience and perform tasks that normally require human intellect. Machine learning, a subset of AI, is the science of getting computers to learn and act like humans do, but with minimal human intervention. They can analyze vast amounts of data within seconds, identifying patterns and trends that would be impossible for a human to recognize. When it comes to fraud detection, this ability is invaluable. Advantages of fraud detection using machine learning AI and machine learning have several benefits that make them valuable in fraud detection. One significant advantage is that these technologies can recognize patterns that are too complex for humans to identify. By running through a vast set of data points, these solutions can pinpoint anomalous behavior, and thereby prevent financial losses. AI analytics tools are adept at monitoring complex networks, detecting the dispersion of attacks that may involve multiple individuals and entities, and correlating activity patterns that would otherwise be hidden. Machine learning algorithms can take these patterns and turn them into mathematical models that help identify instances of fraud before the damage takes place. Secondly, they continuously learn from new data, which allows them to become more efficient in identifying fraud as they process more data. Thirdly, they automate fraud mitigation processes, which significantly reduces the need for manual interventions that may consume valuable time and resources. Another significant benefit of machine learning is its analytics capabilities, which allow organizations to gain valuable insights into customer behavior and fraud patterns. With AI analytics, they can detect and investigate fraudulent activities in real-time, and combine it with other tools to help detect and mitigate fraud risk. For example, in financial services, AI fraud detection can help banks and financial service providers detect and prevent fraud in their systems, add value to their services and improve customer satisfaction. The future of fraud detection and machine learning The rate at which technology is evolving means that machine learning and AI fraud detection will become increasingly important in the future. In the next few years, we can expect a more sophisticated level of fraud detection using unmanned machine systems, robotics process automation, and more. Ultimately, this will improve the efficiency and effectiveness of fraud detection. AI-based fraud management solutions are taking center stage. Organizations must leverage advanced machine learning and AI analytics solutions to prevent and mitigate cyber risks and comply with regulatory mandates. The benefits extend far beyond the financial bottom line to improving the safety and security of customers. AI and machine learning solutions offer accurate, efficient and proactive routes to managing the risk of fraud in an ever-changing environment. How can Experian® help Integrating machine learning for fraud detection represents a significant advancement in cybersecurity. Fraud management solutions detect, prevent and manage fraud across all industries, including financial services, healthcare and telecommunications. With the advancement of technology, fraud management solutions now integrate machine learning to improve their processes. Experian® provides fraud prevention solutions, including machine learning models and AI analytics, which can help more effectively mitigate fraud risk, streamline fraud investigations and create a more secure digital environment for all. With Experian’s AI analytics, risk mitigation tools and fraud management solutions, organizations can stay one step ahead of fraudsters and protect their brand reputation, customer trustworthiness and corporate data. Embracing these solutions can save organizations from significant losses, reputational damage and regulatory scrutiny. To learn more about how to future-proof your business and safeguard your customers from fraud, check out Experian’s robust suite of fraud prevention solutions. Want to hear what our industry experts think? Check out this on-demand webinar on artificial intelligence and machine learning strategies. Learn more Watch webinar *This article includes content created by an AI language model and is intended to provide general information.

Sometimes logging into an account feels a bit like playing 20 questions. Security is vital for a positive customer experience, and engaging the right identity verification strategies is essential to proactive fraud prevention. For financial institutions and businesses, secure authentication is more important than ever. It is imperative for customer safety – which drives retention and loyalty – and your bottom line – as fraud has determinantal effects on and off the balance sheet. Information sharing has proliferated, as has the number of times consumers are prompted to provide access to sensitive information. While today’s consumer has grown accustomed to providing such information, there’s also a heightened demand for security. According to Experian’s 2023 U.S. Identity and Fraud Report, nearly two-thirds (64%) of consumers say they’re very or somewhat concerned with online safety, listing identity theft, stolen card information and online privacy as top concerns. Customers want to know who they are providing access to and whether that entity will have their safety in mind. From a business perspective, one way to ensure that only the right people can get in is by using (KBA). KBA takes traditional authentication methods, like passwords and Personal Identification Numbers (PINs), one step further by creating an additional layer of security through collecting private facts from each user. In this post, we'll look at how KBA works, what its benefits are as a form of identity verification, and how it can improve customer trust. Introducing Knowledge Based Authentication (KBA): What it is and how it works Knowledge Based Authentication can be part of a multifactor authentication solution and is one way to stay on top of privacy and security for your customers – existing and new. KBA is a feature designed to protect online accounts by verifying the account holder’s identity. It involves answering a series of personal questions, such as mother's maiden name or first pet's name, that only the account holder should know. This system has become increasingly popular due to its effectiveness in preventing fraud and identity theft. With KBA, businesses and individuals can have peace of mind that their information is protected by a reliable authentication system that is difficult for unauthorized users to breach. Benefits of implementing KBA and a multifactor authentication strategy By implementing KBA into your business, customers experience an additional layer of security by verifying the identity of users through personalized questions. This reduces the risk of fraud and enhances customer trust and confidence. Secondly, it improves the customer experience by making the authentication process faster and user-friendly. Lastly, KBA reduces costs by automating the authentication process and reducing the need for manual intervention. However, KBA is just one facet of an ideal strategy. Multifactor authentication provides confidence while reducing friction. Risk-based authentication tools allow organizations to assess risk to apply the appropriate level of security. Factors to consider adding to your authentication processes include: Generating unique one-time passwords (OTPs): By creating a new OTP for each transaction, you can increase the level of security. Confirm device ownership: A multifactored approach applies device intelligence checks to increase confidence that the message is reaching the correct user. Maintain low friction with secondary options: If the OTP fails or can’t be attempted by the user, working with a provider who allows an automatic default to another authentication service, such as a knowledge-based authentication solution, decreases end-user friction. Identifying potential security risks associated with KBA KBA relies on personal information that may easily be discovered via social media and other public records, which makes it vulnerable to fraud and identity theft. This highlights the need for a multilayered fraud and identity solution. The landscape of digital security is constantly changing, leveraging an arsenal of fraud and identity prevention strategies, like document verification, one-time passcode, and various identity authentication and verification measures, is critical for keeping your customers and business safe. Commonly used technologies for enhancing KBA security With the rising need for secure authentication, KBA systems have become increasingly popular. However, cyberthreats evolve at an alarming rate, making it imperative to stay current with the latest fraud schemes and how to enhance and supplement your security. Biometrics, like facial recognition and fingerprint scans, as a tactic is gaining traction, as evidenced by “85% of consumers report physical biometrics as the most trusted and secure authentication method they have recently encountered,” according to Experian’s 2023 U.S. Identity and Fraud Report. Additionally, machine learning algorithms detect patterns and anomalies in user behavior and flag any potential security breaches. Multi-factor authentication is another tool that adds an extra layer of security by requiring users to provide multiple forms of identification before logging in. Keeping up with these and other technological advancements can help ensure your KBA system stays one step ahead of potential cyberattacks. Interestingly, there’s a disconnect between the technologies consumers feel safe with and/or are prepared to use versus the technologies and strategies that organizations implement. According to the U.S. Identity and Fraud Report, biometrics are only currently used by 33% of businesses to detect and protect against fraud. An opportunity for business differentiation and driving customer loyalty through a better customer experience may be tapping into some of these lesser used – but sought after – technologies. Compliance with industry standards regarding KBA Ensuring that your system complies with industry standards regarding KBA is crucial for protecting sensitive information from unauthorized access. By implementing the following tips, you can stay ahead of the game and safeguard your organization's data. Analyze your system's current authentication methods and evaluate if they meet industry standards. Additionally, follow standard guidelines for data storage and encryption, limit access to only authorized personnel, and y current with regulations. Lastly, conduct frequent security audits and perform vulnerability tests to identify and address any potential threats. Knowledge-based authentication offers a robust security solution for businesses of all sizes, and incorporating KBA as part of a multifactor authentication strategy is a winning course of action. It provides an added layer of protection for personal data, encourages user accountability, and safeguards against unauthorized access. By leveraging appropriate KBA technologies and maintaining compliance with industry standards, it is possible to create a secure system for customers that gives you peace of mind for your business and bottom line. Experian can help you with knowledge-based authentication offerings, a multifactor authentication strategy and everything in between to enhance your existing authentication process without causing user fatigue. Increase your pass rates, confirm device ownership and add security to risky or high-value transactions, all while executing identity verification and fraud detection to protect your business from risk. The most important step is getting started. Learn more
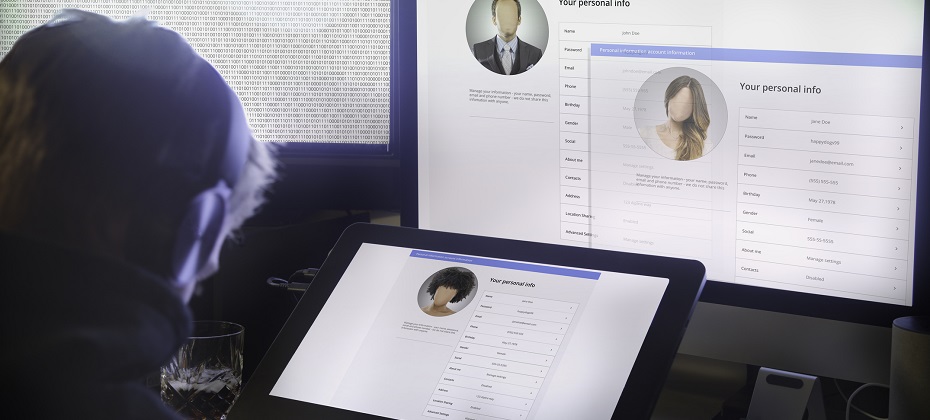
It's that magical time of the year! The holiday season is fast approaching, and folks everywhere are gearing up for festive travels and family reunions. Unfortunately, holiday travel can sometimes lead to unforeseen circumstances, such as fraudulent activities orchestrated by scammers who impersonate property owners on well-known vacation rental platforms. These fraudsters employ schemes designed to deceive unsuspecting travelers into making payments through unsecured channels, resulting in significant financial losses for the gullible victims. Digital identity and hotel fraud Airline and hotel fraud encompasses illicit activities aimed at airlines, hotels, booking platforms, and other travel accommodation services, including car rentals and excursions. These services often utilize loyalty programs to incentivize repeat patronage through point-based rewards. The widespread adoption of such loyalty programs has extended their appeal beyond the travel and hospitality sectors, consequently attracting fraudulent activities. Perpetrators of airline and hospitality fraud employ a range of tactics and different techniques to execute their schemes, leveraging various online forums, marketplaces, shops, and public messaging platforms. Hotels are custodians of valuable guest data, encompassing contact information and payment details. Their operational model involves serving a large pool of potential customers who are making limited visits. Consequently, compromising a hospitality employee's account could grant an identity thief access to millions of consumer records. Moreover, hotel employees are frequent targets of foreign governments aiming to procure confidential travel records to facilitate the tracking of specific individuals and groups. In contrast, restaurants primarily store transaction records with fewer customer details. However, the landscape is evolving as more establishments adopt online ordering capabilities and loyalty programs. At present, cybercriminals typically focus on the high volume of point-of-sale transactions. As travel booms, fraudsters find new paths According to a recent Deloitte survey, Intent to travel between Thanksgiving and mid-January is up across all age and income groups. While reconnecting with friends and family remains paramount to travel during the holidays, fewer Americans are restricting their travel to visiting loved ones. The share of travelers planning to stay in hotels surged to 56%. Fraudsters will always take advantage of current circumstances, and with more people traveling again, they have taken notice — and action. The following techniques have been identified as the most employed by cybercriminals to target customers of airlines, hotels, and hospitality-related organizations: Travel-themed phishing and fraudulent travel agency operations, sales, and advertisements of travel fraud-related tutorials. Sales of compromised networks, user accounts, and databases containing reward/loyalty points and personally identifiable information (PII) that could be utilized for social engineering, money laundering, and other attack vectors. Since the emergence of cyber-enabled crime, services and activities facilitating travel fraud have been extensively promoted and sought after by threat actors. Cybercriminals mainly leverage stolen card-not-present (CNP) data and reward/loyalty points obtained from compromised bank accounts to procure flights, accommodations, and other travel-related services. Furthermore, threat actors persistently refine their strategies for harvesting reward/loyalty points through compromised accounts, deceiving victims into disclosing their travel-related documentation and data and circulating updated guidelines for circumventing hotel and airline reservation services, amongst other activities. Protecting travelers and improving the customer experience Combatting hospitality and hotel fraud requires collaboration between industry stakeholders, government entities, and financial institutions. Travel professionals should focus on: Enhancing data security: Invest in robust cybersecurity measures to protect guest information, payment systems for CNP, and loyalty programs. Implementing identity verification: Utilize advanced technologies, such as biometric authentication and behavioral analytics, to verify guests' identities and prevent account fraud. Educating staff and guests: Provide comprehensive training to employees on recognizing and reporting suspicious activities. Educate guests about potential scams and advise them to book directly through official channels. Sharing information: Establish platforms to share intelligence and best practices to stay ahead of evolving fraud techniques. Acting with the right solution As the travel and hospitality industry continues to thrive, so does the risk of hospitality fraud. Travelers and hoteliers alike must remain vigilant to protect their finances from various fraud schemes prevalent today. By staying informed, taking proactive measures, and fostering collaborative efforts, we can create a safer and more secure environment within the travel industry. Experian’s identity verification solutions power advanced capabilities across the travel lifecycle. With trusted data and advanced analytics, you can gain a complete view of your future guest to improve risk management and offer an enhanced, frictionless customer experience. Learn more *This article leverages/includes content created by an AI language model and is intended to provide general information.