
Meeting Know Your Customer (KYC) regulations and staying compliant is paramount to running your business with ensured confidence in who your customers are, the level of risk they pose, and maintained customer trust.
What is KYC?
KYC is the mandatory process to identify and verify the identity of clients of financial institutions, as required by the Financial Conduct Authority (FCA).
KYC services go beyond simply standing up a customer identification program (CIP), though that is a key component. It involves fraud risk assessments in new and existing customer accounts. Financial institutions are required to incorporate risk-based procedures to monitor customer transactions and detect potential financial crimes or fraud risk. KYC policies help determine when suspicious activity reports (SAR) must be filed with the Department of Treasury’s FinCEN organization.
According to the Federal Financial Institutions Examinations Council (FFIEC), a comprehensive KYC program should include:
• Customer Identification Program (CIP): Identifies processes for verifying identities and establishing a reasonable belief that the identity is valid.
• Customer due diligence: Verifying customer identities and assessing the associated risk of doing business.
• Enhanced customer due diligence: Significant and comprehensive review of high-risk or high transactions and implementation of a suspicious activity-monitoring system to reduce risk to the institution.
The following organizations have KYC oversight: Federal Financial Institutions Examinations Council (FFIEC), Federal Reserve Board, Federal Deposit Insurance Corporation (FDIC), national Credit Union Administration (NCUA), Office of the Comptroller of the Currency (OCC) and the Consumer Financial Protection Bureau (CFPB).
How to get started on building your Know Your Customer checklist
1. Define your Customer Identification Program (CIP)
The CIP outlines the process for gathering necessary information about your customers. To start building your KYC checklist, you need to define your CIP procedure. This may include the documentation you require from customers, the sources of information you may use for verification and the procedures for customer due diligence. Your CIP procedure should align with your organization’s risk appetite and be comply with regulations such as the Patriot Act or Anti-money laundering laws.
2. Identify the customer’s information
Identifying the information you need to gather on your customer is key in building an effective KYC checklist. Typically, this can include their first and last name, date of birth, address, phone number, email address, Social Security Number or any government-issued identification number. When gathering sensitive information, ensure that you have privacy and security controls such as encryption, and that customer data is not shared with unauthorized personnel.
3. Determine the verification method
There are various methods to verify a customer’s identity. Some common identity verification methods include document verification, facial recognition, voice recognition, knowledge-based authentication, biometrics or database checks. When selecting an identity verification method, consider the accuracy, speed, cost and reliability. Choose a provider that is highly secure and offers compliance with current regulations.
4. Review your checklist regularly
Your KYC checklist is not a one and done process. Instead, it’s an ongoing process that requires periodic review, updates and testing. You need to periodically review your checklist to ensure your processes are up to date with the latest regulations and your business needs. Reviewing your checklist will help your business to identify gaps or outdated practices in your KYC process. Make changes as needed and keep management informed of any changes.
5. Final stage: quality control
As a final step, you should perform a quality control assessment of the processes you’ve incorporated to ensure they’ve been carried out effectively. This includes checking if all necessary customer information has been collected, whether the right identity verification method was implemented, if your checklist matches your CIP and whether the results were recorded correctly.
KYC is a vital process for your organization in today’s digital age. Building an effective KYC checklist is essential to ensure compliance with regulations and mitigate risk factors associated with fraudulent activities. Building a solid checklist requires a clear understanding of your business needs, a comprehensive definition of your CIP, selection of the right verification method, and periodic reviews to ensure that the process is up to date. Remember, your customers’ trust and privacy are at stake, so iensuring that your security processes and your KYC checklist are in place is essential. By following these guidelines, you can create a well-designed KYC checklist that reduces risk and satisfies your regulatory needs.
Taking the next step
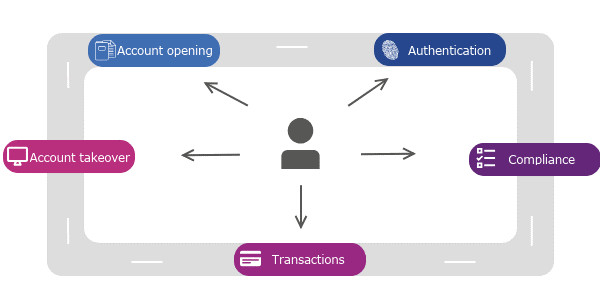
Experian offers identity verification solutions as well as fully integrated, digital identity and fraud platforms. Experian’s CrossCore & Precise ID offering enables financial institutions to connect, access and orchestrate decisions that leverage multiple data sources and services. By combining risk-based authentication, identity proofing and fraud detection into a single, cloud-based platform with flexible orchestration and advanced analytics, Precise ID provides flexibility and solves for some of financial institutions’ biggest business challenges, including identity and fraud as it relates to digital onboarding and account take over; transaction monitoring and KYC/AML compliance and more, without adding undue friction.
*This article includes content created by an AI language model and is intended to provide general information.


