Latest Posts
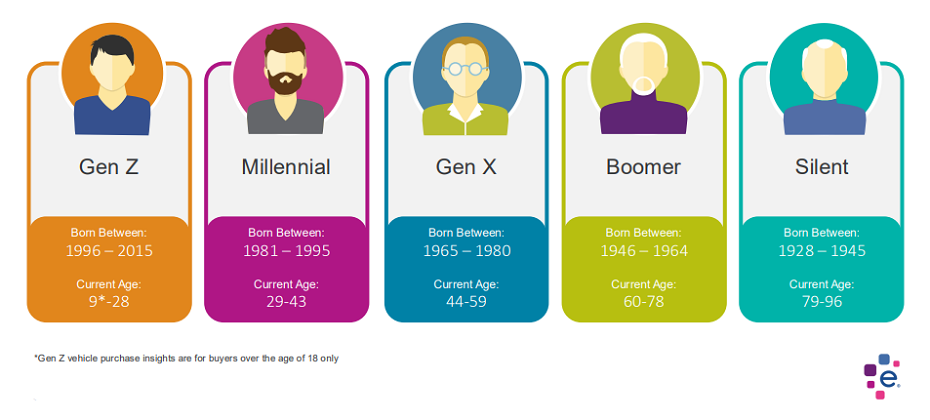
Quick Answer: New research on generational buying habits can help the auto industry better understand target audiences and improve marketing. The automotive industry is undergoing a rapid transformation, driven by technological advancements, changing consumer preferences, and a diverse marketplace. To navigate this complex landscape, understanding your target audience is key. This is where generational insights are indispensable. Why Generations Matter Each generation brings unique values, preferences, and buying behaviors to the table. Ignoring these differences can lead to ineffective marketing campaigns and missed opportunities. Different Needs and Priorities: Baby Boomers, Gen X, Millennials, and Gen Z have distinct needs and priorities when it comes to vehicles. For example, Baby Boomers may purchase more luxury vehicles, while Gen Z purchases a higher percentage of non-luxury vehicles. Communication Styles: Each generation responds differently to marketing messages. Traditional advertising might resonate with Baby Boomers, while social media and influencer marketing could be more effective for younger generations. Purchasing Behavior: The way people research and purchase cars has evolved significantly across generations. Understanding these differences can help you optimize your sales process. Leveraging Generational Insights To effectively leverage generational insights, consider the following: Conduct In-Depth Research: Gain a deep understanding of each generation's values, preferences, and buying habits. Use data analytics, surveys, and focus groups to gather insights. Create Targeted Messaging: Develop tailored messaging that resonates with each generation. Highlight the features and benefits that matter most to them. Choose the Right Channels: Select the most effective marketing channels for each generation. For example, television advertising might be less effective for Gen Z compared to social media. Personalize the Customer Experience: Offer personalized experiences that cater to the specific needs and preferences of each generation. Embrace Technology: Utilize technology to reach and engage different generations. For example, virtual showrooms or augmented reality experiences can appeal to younger consumers. Special Report: Generational Insights We've conducted in-depth research on generational buying habits for new and used vehicles. These insights can revolutionize your automotive marketing and sales strategies. Gain a competitive edge with our Automotive Consumer Trends Special Report: Generation Insights. Discover how to tailor your approach for maximum impact. Conclusion In today's competitive automotive market, understanding your target audience is essential for success. By incorporating generational insights into your marketing strategy, you can create more effective campaigns, build stronger customer relationships, and drive sales growth. Remember, a one-size-fits-all approach is unlikely to work. Embrace the diversity of your audience and tailor your message accordingly. Experian Automotive is here to help you with your marketing needs. If you’d like to learn more about our solutions and how we can support you, contact us below.

Quick Answer: Dealerships can avoid purchasing flood-damaged vehicles with Experian AutoCheck's Free Flood Risk Check. The used car market is tough right now. Unfortunately, recent floods in several areas have added another challenge: flood-damaged vehicles. These cars pose a big risk to dealerships. Buying one can lead to expensive repairs, unhappy customers, and damage to your reputation. Experian AutoCheck's Free Flood Risk Check can help. We've updated it with data from recent floods to give you a head start. Here's what the Free Flood Risk Check does: Quickly checks any car's flood risk with just the 17-digit VIN. Provides you with two levels of reporting: See if the car was registered in a region hit by a major FEMA disaster. Find potential flood damage based on Experian data (flood titles, auction records, etc.). Important things to remember: A "Yes" in the first report doesn't confirm flood damage, just that the car was in a flood zone. Even a clean second report isn't a guarantee - some flood damage goes unreported. For extra protection: Run a full Experian AutoCheck Vehicle History Report to uncover other issues like accidents or recalls. Have a mechanic thoroughly inspect any car before you buy it. By using Experian AutoCheck's Free Flood Risk Check and following these tips, you can dramatically reduce the risk of buying a flood-damaged car and protect your dealership. Ready to safeguard your dealership? Not an Experian AutoCheck subscriber?
Experian’s ninth annual report on identity and fraud highlights persistent worries among consumers and businesses about fraud, including growing threats from GenAI. In this report, we explore how the evolving fraud landscape is impacting identity verification, customer experience, and business priorities for the future. Our 2024 U.S. Identity and Fraud Report draws insights from surveys of over 2,000 U.S. consumers and 200 businesses. This year’s report dives into: Evolving consumer sentiment over security and experience Businesses’ investments to tackle growing fraud challenges Effective technology solutions to accurately identify and authenticate consumers The impact of GenAI on the fraud landscape To keep pace with the evolving landscape, businesses will need to apply a multi-faceted strategy that leverages multiple types of recognition and security to stop all types of fraud while allowing real customers through. To learn more about our findings and perspective, read the full 2024 U.S. Identity and Fraud Report, watch our on-demand webinar, or read the press release. Download Now Watch Webinar Read Press Release

Gen Z, or "Zoomers," born from 1997 to 2012, are molded by modern transformations. They have witnessed events from post-9/11 impacts to the rise of the internet and the COVID-19 crisis. As early adopters of technology, their lives are intertwined with smartphones, online shopping, social platforms, cloud services, emerging fintech, and artificial intelligence. They are called “digital natives” as they are the first generation to grow up with internet as part of their daily life. Research generally indicates that this post-millennial generation values practicality, favoring financial stability over entrepreneurial pursuits. They appreciate communication tailored to them and often employ social media to cultivate their personal brands. As a generation growing up immersed in technology, they tend to choose digital interactions, seeking to forge robust, secure, genuine, and unconstrained digital experiences. The challenge of identity verification Identity verification presents a considerable challenge for Generation Z. According to a Fortune survey, close to 50% of this demographic regrets not opening financial accounts earlier, citing a lack of readiness to join the financial ecosystem by the age of 18. Consequently, this has given rise to "digital ghosts"—people with minimal or nonexistent financial histories who face challenges when trying to utilize financial services. The 2009 Credit Card Accountability Responsibility and Disclosure Act mandates that individuals under 21 need a cosigner or show income proof to get a credit card, hindering their early financial involvement. Moreover, conventional identity checks are becoming less reliable due to the surge in identity theft. Innovative solutions for verifying Gen Z Verifying identities and preventing fraud among Gen Z presents unique challenges due to their digital-native status and limited credit histories. Here are some effective strategies and approaches that financial institutions can adopt to address these challenges: Leveraging alternative data sources Academic records leverage information from higher learning institutions such as universities, colleges, and vocational schools. This data can be vital for authenticating the identities of younger individuals who may lack a substantial credit history. Employment verification retrieve data confirming the identity and employment status, especially focusing on Gen Z who are new to the job market. Utility and telecom records leverage payment histories for utilities, phone bills, and other recurring services, which can provide additional layers of identity verification. Alternative financial data includes online small dollar lenders, online installment lenders, single payment, line of credit, storefront small dollar lenders, auto title and rent-to-own. Phone-Centric ID Phone-Centric Identity refers to technology that leverages and analyzes mobile, telecom, and other signals for the purposes of identity verification, identity authentication, and fraud prevention. Phone-Centric Identity relies on billions of signals from authoritative sources pulled in real time, making it a powerful proxy for digital identity and trust. Advance authentication technologies Behavioral biometrics analyze user behaviors such as typing patterns, navigation habits, and device usage. These subtle behaviors can help create a unique profile for each user, making it difficult for fraudsters to impersonate them. Adaptive risk-based authentication that adjusts the level of security based on the user's behavior, location, device, and other factors. For example, a higher level of verification might be required for transactions that are deemed unusual or high-risk. Real-time fraud detection AI and machine learning: Deploy AI and machine learning algorithms to analyze transaction patterns and detect anomalies in real-time. These technologies can identify suspicious activities and flag potential fraud. Fraud analytics: Use predictive analytics to assess the likelihood of fraud based on historical data and current behavior. This approach helps in proactively identifying and mitigating fraudulent activities. Secure digital onboarding Digital identity verification: Implement digital onboarding processes that include online identity verification with real-time document verification. Users can upload government-issued IDs and take selfies to confirm their identity. Video KYC (Know Your Customer): Use video calls to conduct KYC processes, allowing bank representatives to verify identities and documents remotely via automated identity verification. This method is secure and convenient for tech-savvy Gen Z customers. Make identity verification easy To authenticate identities and combat fraud within the Gen Z population, financial organizations need to implement a comprehensive strategy utilizing innovative technologies, non-traditional data, and strong protective protocols. Such actions will enable the creation of a trustworthy and frictionless banking environment that appeals to a generation adept in digital interactions, thereby establishing trust and encouraging enduring connections. To learn more about Experian’s automated identity verification solutions, visit our website. Learn more

In this article...Rise of AI in fraudulent activitiesFighting AI with AI Addressing fraud threatsBenefits of leveraging AI fraud detectionFinancial services use caseExperian's AI fraud detection solutions In a world where technology evolves at lightning speed, fraudsters are becoming more sophisticated in their methods, leveraging advancements in artificial intelligence (AI). According to our 2025 U.S. Identity and Fraud Report, 72% of businesses expect AI fraud to be among their top challenges by 2026. To combat emerging fraud threats, organizations are turning to AI fraud detection to stay ahead and protect their businesses and their customers, essentially fighting AI with AI. This blog post explores the evolving AI fraud and AI fraud detection landscape. The rise of AI in fraudulent activities Technology is a double-edged sword. While it brings numerous advancements, it also provides fraudsters with new tools to exploit. AI is no exception. Here are some ways fraudsters are utilizing AI: Automated bot attacks: Fraudsters employ AI to design automated scripts that launch large-scale attacks on systems. These scripts can perform credential stuffing, where stolen usernames and passwords are automatically tested across multiple sites to gain unauthorized access. Deepfakes and synthetic identities: Deepfake technology and the creation of synthetic identities are becoming more prevalent. Fraudsters use AI to manipulate videos and audio, making it possible to impersonate individuals convincingly. Similarly, synthetic identities blend real and fake information to create false personas. Phishing and social engineering: AI-driven phishing attacks are more personalized and convincing than traditional methods. By analyzing social media profiles and other online data, fraudsters craft tailored messages that trick individuals into revealing sensitive information. Watch now: Our 2025 Fraud Trends webinar explores how businesses can navigate rising risk, meet growing consumer expectations, and stay ahead of increasingly complex attacks. Fighting AI with AI in fraud detection To combat these sophisticated threats, businesses must adopt equally advanced measures. AI fraud detection offers a robust solution: Machine learning algorithms: Fraud detection machine learning algorithms analyze vast datasets to identify patterns and anomalies that indicate fraudulent behavior. These algorithms can continuously learn and adapt, improving their accuracy over time. Real-time monitoring: AI systems provide real-time monitoring of transactions and activities. This allows businesses to detect and respond to fraud attempts instantly, minimizing potential damage. Predictive analytics: Predictive analytics uses historical data to forecast future fraud trends. By anticipating potential threats, organizations can take proactive measures to safeguard their assets. Addressing fraud threats with AI fraud detection AI's versatility allows it to tackle various types of fraud effectively: Identity theft: According to our research, 68% of consumers rank identity theft as their top online concern. AI systems can help safeguard consumers by cross-referencing multiple data points to verify identities. They can spot inconsistencies that indicate identity theft, such as mismatched addresses or unusual login locations. Payment fraud: Coming in second to identity theft, 61% of consumers rank stolen credit card information as their top online concern. Payment fraud includes unauthorized credit card transactions and chargebacks. AI can be used in payment fraud detection to surface unusual spending patterns and flag suspicious transactions for further investigation. Account takeover: Account takeover fraud, one of the top-most encountered fraud events reported by U.S. businesses, occurs when fraudsters gain access to user accounts and conduct unauthorized activities.* AI identifies unusual login behaviors and implements additional security measures to prevent account breaches. Synthetic identity fraud: Synthetic identity fraud involves the creation of fake identities using real and fabricated information. AI fraud solutions detect these false identities by analyzing data inconsistencies and behavioral patterns. Benefits of leveraging AI fraud detection Implementing AI fraud detection offers numerous advantages: Enhanced accuracy: AI systems are highly accurate in identifying fraudulent activities. Their ability to analyze large datasets and detect subtle anomalies surpasses traditional methods. Cost savings: By preventing fraud losses, AI systems save businesses significant amounts of money. They also reduce the need for manual investigations, freeing up resources for other tasks. Improved customer experience: AI fraud detection minimizes false positives, ensuring genuine customers face minimal friction. This enhances the overall customer experience and builds trust in the organization. Scalability: AI systems can handle large volumes of data, making them suitable for organizations of all sizes. Whether you're a small business or a large enterprise, AI can scale to meet your needs. Financial services use case The financial sector is particularly vulnerable to fraud, making AI an invaluable tool for fraud detection in banking. Protecting transactions: Banks use AI to monitor transactions for signs of fraud. Machine learning algorithms analyze transaction data in real time, flagging suspicious activities for further review. Enhancing security: AI enhances security by implementing multifactor authentication and behavioral analytics. These measures make it more challenging for fraudsters to gain unauthorized access. Reducing fraud losses: By detecting and preventing fraudulent activities, AI helps banks reduce their fraud losses throughout the customer lifecycle. This not only saves money but also protects the institution's reputation. Experian's AI fraud detection solutions AI fraud detection is revolutionizing the way organizations combat fraud. Its ability to analyze vast amounts of data, detect anomalies, and adapt to new threats makes it an essential element of any comprehensive fraud strategy. Experian’s range of AI fraud detection solutions help organizations enhance their security measures, reduce fraud losses, authenticate identity with confidence, and improve the overall customer experience. If you're interested in learning more about how AI can protect your business, explore our fraud management solutions or contact us today. Learn More * Source: 2025 U.S. Identity and Fraud Report This article includes content created by an AI language model and is intended to provide general information.
With the noticeable uptick in delinquencies, credit unions face more significant hurdles in effectively managing overdue accounts. In this challenging financial landscape, it’s imperative that you refine your account management processes to remain competitive, preserve the well-being of your members, assure operational efficiency, and increase profitability. Implementing efficient collection approaches not only improves loss rates but also helps with member retention, which is the backbone of your success. Grab a cup of coffee and join our experts on August 22 @ 1:00 p.m. ET/ 10:00 a.m. PT, for an engaging conversation on credit union collection trends and successful account management strategies. Highlights include: Current landscape: Gain valuable insight and understanding into the current debt collection environment for credit unions. Navigating challenges: Discover effective tips and strategies to tackle obstacles in your business, improve loss rates, and enhance member retention. Real-time Q&A: Participate in a live Q&A session where our experts will address your questions. Watch on-demand

In this article...Recent trends in credit card debtThe rising tide of delinquenciesWhat is credit limit optimization?Benefits of credit limit optimizationEconomic indicators and CLO ImpactEnhanced profitability and risk mitigation This post was originally published on our Global Insights Blog. As credit card issuers grow, the size of their customer base expands, bringing both opportunities and challenges. One of the most critical challenges is managing growth while controlling default rates. Credit limit optimization (CLO) has emerged as a vital tool for banks and credit lenders to achieve this balance. By leveraging machine learning models and mathematical optimization, CLO enables lenders to tailor credit limits to individual customers, enhancing profitability while mitigating risk. Recent trends in credit card debt To understand the significance of CLO, it is essential to consider the current economic landscape. The first quarter of 2024 saw total household debt in the U.S. rise by $184 billion, reaching $17.69 trillion. While credit card balances declined slightly (a reflection of seasonal factors and consumer spending patterns), they remain a substantial component of household liabilities, with total credit card debt standing at approximately $1.26 trillion in early 2024. On average, American households hold around $10,479 in credit card debt, which is down from previous years but still significant. The average APR for credit cards in the first quarter of 2024 was 21.59%.* The rising tide of delinquencies In the first quarter of 2024, about 8.9% (annualized) of credit card balances transitioned into delinquency. This trend underscores the need for credit card issuers to adopt more sophisticated methods to assess credit risk and adjust credit limits accordingly. The rising rate of credit card delinquencies is a key driver behind the adoption of CLO strategies. What is credit limit optimization? Credit limit optimization uses advanced analytics to assess individual customers’ creditworthiness. By analyzing various data points, including payment history, income levels, spending patterns, and economic indicators, these tools can recommend optimal credit limits that maximize customer spending potential while minimizing the risk of default, all within the constraints set by the business in terms of its appetite for risk and capacity. For instance, a customer with a strong payment history and stable income might receive a higher credit limit, encouraging more spending and enhancing the lender’s revenue through interest and interchange fees. Conversely, customers showing signs of financial stress might see their credit limit reduced to prevent them from accumulating unmanageable debt. Benefits of credit limit optimization Improved profitability – By setting credit limits reflecting customers’ credit risk and spending potential, lenders can increase their revenue through higher interest and fee income. Reduced default rates – Lenders can significantly reduce the incidence of bad debt by identifying customers at risk of default and adjusting their credit limits accordingly. Improved customer satisfaction – Personalized credit limits can improve customer satisfaction, as customers are more likely to receive credit that matches their needs and financial situation. Regulatory compliance – CLO can help lenders comply with regulatory requirements by ensuring that credit limits are set based on objective, data-driven criteria. Economic indicators and CLO Impact Several economic indicators provide context for the importance of CLO in the current market. For instance, the Federal Reserve reported that in 2023, fewer than half of adult credit cardholders carried a balance on their cards, down from previous years. This indicates a more cautious approach to credit use among consumers, likely influenced by economic uncertainty and rising interest rates. Moreover, the disparity in credit card debt across different states highlights the varying economic conditions and the need for tailored credit strategies. States like New Jersey have some of the highest average credit card debts, while states like Mississippi have the lowest. This regional variation underscores lenders’ need to adopt flexible, data-driven approaches to credit limit setting. Enhanced profitability and risk mitigation Credit limit optimization is critical for credit card issuers aiming to balance growth and risk management. As economic conditions evolve and consumer behaviors shift, the ability to set personalized credit limits will become increasingly important. By leveraging advanced analytics and machine learning, CLO enhances profitability and contributes to a more stable and resilient financial system. One such solution is Experian’s Ascend Intelligence Services™ Limit, which provides an optimized strategy designed to enhance the precision and effectiveness of credit limit assignments. Ascend Intelligence Services™ Limit combines best-in-class bureau data with machine learning to simulate the impact of different credit limits in real time. This capability allows lenders to quickly test and refine their credit limit strategies without the lengthy trial-and-error period traditionally required. Ascend Intelligence Services Limit enables lenders to set credit limits that align with their business objectives and risk tolerance. By providing insights into the likelihood of default and potential revenue for each credit limit scenario, Ascend Intelligence Services Limit helps design optimal limit strategies. This not only maximizes revenue but also minimizes the risk of defaults by ensuring credit limits are appropriate for each customer’s financial situation. In a landscape marked by rising delinquencies and varying regional debt levels, the strategic use of CLO like Ascend Intelligence Services Limit represents a forward-thinking approach to credit management, benefiting both lenders and consumers. Learn More * HOUSEHOLD DEBT AND CREDIT REPORT (Q1 2024) – Federal Reserve Bank of New York

In this article...What is credit card fraud?Types of credit card fraudWhat is credit card fraud prevention and detection?How Experian® can help with card fraud prevention and detection With debit and credit card transactions becoming more prevalent than cash payments in today’s digital-first world, card fraud has become a significant concern for organizations. Widespread usage has created ample opportunities for cybercriminals to engage in credit card fraud. As a result, millions of Americans fall victim to credit card fraud annually, with 52 million cases reported last year alone.1 Preventing and detecting credit card fraud can save organizations from costly losses and protect their customers and reputations. This article provides an overview of credit card fraud detection, focusing on the current trends, types of fraud, and detection and prevention solutions. What is credit card fraud? Credit card fraud involves the unauthorized use of a credit card to obtain goods, services or funds. It's a crime that affects individuals and businesses alike, leading to financial losses and compromised personal information. Understanding the various forms of credit card fraud is essential for developing effective prevention strategies. Types of credit card fraud Understanding the different types of credit card fraud can help in developing targeted prevention strategies. Common types of credit card fraud include: Card not present fraud occurs when the physical card is not present during the transaction, commonly seen in online or over-the-phone purchases. In 2023, card not present fraud was estimated to account for $9.49 billion in losses.2 Account takeover fraud involves fraudsters gaining access to a victim's account to make unauthorized transactions. In 2023, account takeover attacks increased 354% year-over-year, resulting in almost $13 billion in losses.3,4 Card skimming, which is estimated to cost consumers and financial institutions over $1 billion per year, occurs when fraudsters use devices to capture card information from ATMs or point-of-sale terminals.5 Phishing scams trick victims into providing their card information through fake emails, texts or websites. What is credit card fraud prevention and detection? To combat the rise in credit card fraud effectively, organizations must implement credit card fraud prevention strategies that involve a combination of solutions and technologies designed to identify and stop fraudulent activities. Effective fraud prevention solutions can help businesses minimize losses and protect their customers' information. Common credit card fraud prevention and detection methods include: Fraud monitoring systems: Banks and financial institutions employ sophisticated algorithms and artificial intelligence to monitor transactions in real time. These systems analyze spending patterns, locations, transaction amounts, and other variables to detect suspicious activity. EMV chip technology: EMV (Europay, Mastercard, and Visa) chip cards contain embedded microchips that generate unique transaction codes for each purchase. This makes it more difficult for fraudsters to create counterfeit cards. Tokenization: Tokenization replaces sensitive card information with a unique identifier or token. This token can be used for transactions without exposing actual card details, reducing the risk of fraud if data is intercepted. Multifactor authentication (MFA): Adding an extra layer of security beyond the card number and PIN, MFA requires additional verification such as a one-time code sent to a mobile device, knowledge-based authentication or biometric/document confirmation. Transaction alerts: Many banks offer alerts via SMS or email for every credit card transaction. This allows cardholders to spot unauthorized transactions quickly and report them to their bank. Card verification value (CVV): CVV codes, typically three-digit numbers printed on the back of cards (four digits for American Express), are used to verify that the person making an online or telephone purchase physically possesses the card. Machine learning and AI: Advanced algorithms can analyze large datasets to detect unusual patterns that may indicate fraud, such as sudden large transactions or purchases made in different geographic locations within a short time frame. Advanced algorithms can analyze large datasets to detect unusual patterns that may indicate fraud, such as sudden large transactions or purchases made in different geographic locations within a short time frame. Behavioral analytics: Monitoring user behavior to detect anomalies that may indicate fraud. Education and awareness: Educating consumers about phishing scams, identity theft, and safe online shopping practices can help reduce the likelihood of falling victim to credit card fraud. Fraud investigation units: Financial institutions have teams dedicated to investigating suspicious transactions reported by customers. These units work to confirm fraud, mitigate losses, and prevent future incidents. How Experian® can help with card fraud prevention and detection Credit card fraud detection is essential for protecting businesses and customers. By implementing advanced detection technologies, businesses can create a robust defense against fraudsters. Experian® offers advanced fraud management solutions that leverage identity protection, machine learning, and advanced analytics. Partnering with Experian can provide your business with: Comprehensive fraud management solutions: Experian’s fraud management solutions provide a robust suite of tools to prevent, detect and manage fraud risk and identity verification effectively. Account takeover prevention: Experian uses sophisticated analytics and enhanced decision-making capabilities to help businesses drive successful transactions by monitoring identity and flagging unusual activities. Identifying card not present fraud: Experian offers tools specifically designed to detect and prevent card not present fraud, ensuring secure online transactions. Take your fraud prevention strategies to the next level with Experian's comprehensive solutions. Explore more about how Experian can help. Learn More Sources 1 https://www.security.org/digital-safety/credit-card-fraud-report/ 2 https://www.emarketer.com/chart/258923/us-total-card-not-present-cnp-fraud-loss-2019-2024-billions-change-of-total-card-payment-fraud-loss 3 https://pages.sift.com/rs/526-PCC-974/images/Sift-2023-Q3-Index-Report_ATO.pdf 4 https://www.aarp.org/money/scams-fraud/info-2024/identity-fraud-report.html 5 https://www.fbi.gov/how-we-can-help-you/scams-and-safety/common-scams-and-crimes/skimming This article includes content created by an AI language model and is intended to provide general information.

Getting customers to respond to your credit offers can be difficult. With the advent of artificial intelligence (AI) and machine learning (ML), optimizing credit prescreen campaigns has never been easier or more efficient. In this post, we'll explore the basics of prescreen and how AI and ML can enhance your strategy. What is prescreen? Prescreen involves evaluating potential customers to determine their eligibility for credit offers. This process takes place without the consumer’s knowledge and without any negative impact on their credit score. Why optimize your prescreen strategy? In today's financial landscape, having an optimized prescreen strategy is crucial. Some reasons include: Increased competition: Financial institutions face stiff competition in acquiring new customers. An optimized prescreen strategy helps you stand out by targeting the right individuals with tailored offers, increasing the chances of conversion. Customer expectations: Modern customers expect personalized and relevant offers. An effective prescreen strategy ensures that your offers resonate with the specific needs and preferences of potential customers. Strict budgets: Organizations today are faced with a limited marketing budget. By determining the right consumers for your offers, you can minimize prescreen costs and maximize the ROI of your campaigns. Regulatory compliance: Compliance with regulations such as the Fair Credit Reporting Act (FCRA) is essential. An optimized prescreen strategy helps you stay compliant by ensuring that only eligible individuals are targeted for credit offers. Financial inclusion: 49 million American adults don’t have conventional credit scores. An optimized prescreen strategy allows you to send offers to creditworthy consumers who you may have missed due to a lack of traditional credit history. How AI and ML can enhance your strategy AI and ML can revolutionize your prescreen strategy by offering advanced analytics and custom response modeling capabilities. AI-driven data analytics AI analytics allow financial institutions to analyze vast amounts of data quickly and accurately. This enables you to identify patterns and trends that may not be apparent through traditional analysis. By leveraging data-centric AI, you can gain deeper insights into customer behavior and preferences, allowing for more precise targeting and increased response rates. LEARN MORE: Explore the benefits of AI for credit unions. Custom response modeling Custom response models enable you to better identify individuals who fall within your credit criteria and are more likely to respond to your credit offers. These models consider various factors such as credit history, spending habits, and demographic information to predict future behavior. By incorporating custom response models into your prescreen strategy, you can select the best consumers to engage, including those you may have previously overlooked. LEARN MORE: AI can be leveraged for numerous business needs. Learn about generative AI fraud detection. Get started today Incorporating AI and ML into your prescreen campaigns can significantly enhance their effectiveness and efficiency. By leveraging Experian's Ascend Intelligence Services™ Target, you can better target potential customers and maximize your marketing spend. Our optimized prescreen solution leverages: Full-file credit bureau data on over 245 million consumers and over 2,100 industry-leading credit attributes. Exclusive access to the industry's largest alternative datasets from nontraditional lenders, rental data inputs, full-file public records, and more. 24 months of trended data showing payment patterns over time and over 2,000 attributes that help determine your next best action. When it comes to compliance, Experian leverages decades of regulatory experience to provide the documentation needed to explain lending practices to regulators. We use patent-pending ML explainability to understand what contributed most to a decision and generate adverse action codes directly from the model. For more insights into Ascend Intelligence Services Target, view our infographic or contact us at 855 339 3990. View infographic This article includes content created by an AI language model and is intended to provide general information.

This series will dive into our monthly State of the Economy report, providing a snapshot of the top monthly economic and credit data for those in financial services to proactively shape their business strategies. While much of the economic data released this month remained steady, including continued downward progress in inflation and resilience in inflation-adjusted spending, June was a pivotal month for the labor market. With downward revisions to job creation over the past few months to an up-tick in unemployment, the potential for a sooner-than-expected rate cut increased. Data highlights from this month’s report include: While above economists’ expectations in June, job creation was 111,000 jobs shy of what was recorded in April and May, signaling some slowdown in the labor market. Inflation-adjusted spending and incomes increased in May, by 0.3% and 0.5%, respectively. Inflation eased more than economists expected, with annual headline inflation cooling from 3.3% to 3.0%. Check out our report for a deep dive into the rest of this month’s data, including the latest trends in job openings, new business survival rates, and bankcard delinquency rates. Download July's report To have a holistic view of our current environment, it’s important to view the economy from different angles and through different lenses. Watch our experts discuss the latest economic and credit trends in the next macroeconomic forecasting webinar and listen to our latest Econ to Action podcast. For more economic trends and market insights, visit Experian Edge.

For car dealers, the holy grail isn't a flashy sports car or a top-selling SUV. It's a simple whisper: "I'm thinking about getting a new car." Imagine if you could hear that murmur from every potential customer walking through your doors, online, or even driving down the street. That's the power of knowing who's in the market for a new car, and it's a game-changer for dealerships. Go beyond the cookie and website tracking and leverage the power of psychographic data and predictive analytics to know who is coming into the market in the next 30, 60, 90 days with the Experian Marketing Engine’s Affinity AutoAudiences. Boost Efficiency and ROI: Targeted Sales: No more shotgun blasts of marketing campaigns! Precisely target consumers considering a new car with personalized offers and incentives. Imagine tailoring financing proposals based on their budget and desired features, not guesswork. Inventory Optimization: Say goodbye to dusty lots filled with unsold models. Knowing market trends and individual preferences allows you to stock in-demand vehicles, maximizing sales and minimizing depreciation costs. Streamlined Sales Process: When a customer walks in already open to buying, the entire process becomes smoother. Focus on addressing their specific needs and preferences, leading to quicker deals and happier customers. Build Stronger Customer Relationships: Proactive Engagement: Instead of waiting for leads, reach out at the perfect moment. A friendly call or email during their research phase demonstrates attentiveness and builds trust, setting you apart from the competition. Personalized Recommendations: Forget one-size-fits-all pitches. Recommend models based on their lifestyle, budget, and driving habits. This shows genuine interest and builds rapport, increasing the likelihood of conversion. Enhanced Customer Experience: Cater to their specific needs before they even step onto the lot. Offer virtual test drives, online financing options, and even home delivery – all tailored to their preferences. This level of personalized service fosters loyalty and repeat business. Leverage the Power of Data: Knowing when a consumer is in the market for a new car isn't just about a head start, it's about building trust, offering convenience, and tailoring the entire experience to their needs. In a competitive market, this inside knowledge is the key to unlocking increased sales, stronger customer relationships, and ultimately, a thriving dealership. So, what are you waiting for? Start listening and turn those whispers into deals! Or

With rising consumer debt and an increasing number of consumers defaulting on loans, effective debt recovery strategies have never been more critical. Skip-tracing is the first-step in effective debt collection. This essential practice helps locate individuals who have become difficult to find, ensuring that you can recover outstanding debts efficiently. In this blog post, we'll explore skip-tracing best practices, offering valuable insights and practical tips and tools. Understanding and implementing these collection strategies can enhance your debt recovery efforts, improve overall efficiency, and increase your recovery rates. Understanding the importance of skip-tracing Skip-tracing is the process of locating individuals who have moved or otherwise become difficult to find. This technique is particularly important for financial institutions and debt collectors, enabling them to contact debtors and recover outstanding payments. Given the high stakes involved, mastering skip-tracing best practices is crucial for ensuring successful debt recovery. How to create an effective skip-tracing strategy 1. Use comprehensive skip-tracing data sources One of the foundational elements of an effective skip-tracing strategy is the use of comprehensive skip-tracing data sources. You can gather valuable information about a debtor's whereabouts by leveraging multiple databases, including public records, credit reports, and alternative data sources. The more data sources you utilize, the better chance of making right-party contact. 2. Prioritize data privacy While skip-tracing is essential for debt recovery, it's crucial to prioritize data privacy. Always adhere to the latest consumer contact debt collection regulations. This protects the individual's privacy and safeguards your organization from potential legal issues. 3. Stay updated with regulatory changes The regulatory landscape for debt collection and contacting consumers is constantly evolving. Staying updated with the latest changes ensures that your skip-tracing practices remain compliant with the law. Regularly review industry regulations, obtain proper consent from consumers and adjust your strategies accordingly. 4. Train your team Skip-tracing requires specialized skills and knowledge. Investing in regular training for your team ensures that they are equipped with the latest techniques and best practices. Offer workshops, webinars, and certification programs to keep your team up to date and improve their effectiveness. 5. Utilize skip-tracing software Skip-tracing software can significantly streamline the process and improve accuracy. Look for software solutions that offer comprehensive data integration, advanced search capabilities, and user-friendly interfaces. Implementing the right software can save time and resources while increasing right-party contact. 6. Monitor and evaluate performance Regularly monitoring and evaluating the performance of your skip-tracing efforts is essential for continuous improvement. Track key metrics such as right-party contact rates, time taken to locate individuals, contact method and cost. Use this data to identify areas for improvement and adjust your strategies accordingly. 7. Adapt to changing circumstances The world of debt management is dynamic, and circumstances can change rapidly. Be prepared to adapt your skip-tracing strategies to evolving situations. Whether it's changes in debtor behavior, new technology, or shifts in the regulatory landscape, staying flexible ensures that your skip-tracing efforts remain effective. Why choose Experian® for skip-tracing solutions Skip-tracing is a critical tool for financial institutions and debt collectors, enabling them to locate individuals and recover outstanding debts efficiently. Understanding and implementing collection best practices can improve your efforts and overall success rates. As a global leader in data and analytics, we offer extensive expertise and cutting-edge skip-tracing tools tailored to meet your unique needs. Comprehensive data integration: Our skip-tracing tools integrate data from multiple sources, including credit reports, alternative data, public records, and proprietary databases. This comprehensive approach ensures that you have access to accurate and up-to-date information, improving right-party contact. Recent and reliable data: While many data providers rely on static or stale data, our skip-tracing data is frequently updated, so you can avoid inaccurate, outdated information. More than 1.3 billion updates are made per month, including new phone numbers, new addresses, new employment, payment history, and more. Advanced technology: Our skip-tracing solutions leverage advanced technology, including AI and ML, to analyze data quickly and accurately. Our state-of-the-art algorithms identify patterns and connections to help you locate individuals more efficiently. Commitment to data privacy: We prioritize data privacy and adhere to the highest ethical standards. Our skip-tracing solutions are designed to protect personal information while ensuring compliance with industry regulations. You can trust us to handle data responsibly and ethically. Ready to take your skip-tracing efforts to the next level? Learn more Access white paper

Open banking has been leveraged for years in the U.S. The anticipated U.S. regulation under section 1033 of the Dodd-Frank Act, combined with the desire to expand lending universes, has increased interest and urgency among financial institutions to incorporate open banking flows into their workstreams. With technological improvements, increased data availability, and increasing consumer awareness around the benefits of data value exchange, financial service providers can use consumer-permissioned data to gain new insights. For example, access to bank account transactional data, permissioned appropriately, provides important attributes into risk, spend and income behaviors, and financial health, while equipping institutions with intelligence they can harness to help meet various business objectives. Current state of open banking Open Banking use cases are extensive and will continue to expand as access to permissioned data becomes more common. Second chance underwriting, where a lender retrieves additional insights to potentially reverse the primary declination, is the most prevalent use case in the market today. Where a consumer may have limited or no credit history, this application of cashflow attributes and scores in a decisioning flow can help many consumers access financial services where they cannot be fully underwritten on credit data alone. And it is not just consumer behavior and willingness to permission their data that will accelerate open banking in financial services. The technology enabling access, security, standardization, and categorization is equally critical. New and existing players across the ecosystem are rolling out new solutions to drive results for financial institutions. The benefits of open banking are vast as highlighted recently by Craig Focardi, Principal Analyst at Celent: “The final adoption of the CFPB’s proposed rule under Section 1033 will accelerate open banking in the US,” said Focardi. “Although open banking is operating effectively under existing consumer protection/privacy and related laws and regulations, this modern opening banking rule will enhance consumer control over their data for privacy and security, help consumers better manage their finances, and help them find the best products and banking relationships. For financial institutions, it will level the competitive playing field for smaller financial institutions, increase competition for customer relationships, and incentivize all financial institutions to invest in technology, data, and analytics to adopt open banking more quickly.” Despite the wealth of information that open banking can offer, institutions are at varying stages of maturity when it comes to using this data in production, with fintechs and challenger banks leading the way. However, most banks are researching and planning to take advantage of the insights unlocked through open banking – particularly cashflow data. But why is there not wider adoption when this ‘new’ data can offer such rich and actionable insights? The answer varies, but it is top of mind for risk officers, analysts and marketers. Some financial institutions are worried about application drop-off as consumers move through a data consent journey. Others are taking a wait-and-see approach as they are concerned about incorporating open banking flows only to see regulation upend the application of permissioned data. Regardless of readiness, most organizations are in various stages of testing new permissioned data sources to understand the implications. Experian has helped many financial institutions understand the power of consumer-permissioned data through analytics and specific tests leveraging client transactional data and our cash flow models. On aggregate, we see cashflow data perform well on its own in determining a consumer’s likelihood of going 60 days past due over 12 months; however, it is best used in combination with traditional and alternative credit data to achieve optimal performance of underwriting models. But what about consent? Will consumers be open to permissioning their data? From our research, we see that consumers are willing to give permission if the benefits are explained and they understand how their data will be used. In fact, 70% of consumers report they are likely to share banking data for better loan rates, financial tools, or personalized spending insights.1 Experian reveals new solutions for open banking We at Experian are excited about the benefits open banking can provide, including: Giving more control to consumers: Consumers are hungry for more control over their data. We have seen this ourselves with Experian Boost®. When the benefits of data sharing are properly explained, and consumers can control when and how that data is used, it is empowering and allows consumers the potential to unlock new financial opportunities. Improving risk assessment: As mentioned above, analysis shows that cash flow data (transactional open banking data) is very predictive on its own. Adding our credit data delivers even greater predictability, enabling lenders to score more consumers and offer the right products, services, and pricing. Augmenting existing strategies: Open banking is not a new strategy; it augments and improves many existing processes. Institutions do not need to start something from scratch; they can layer incremental data into existing processes for an improved risk assessment, deeper insights, and a better customer experience. Open banking is not a new strategy; it augments and improves many existing processes. Institutions do not need to start something from scratch; rather, they can layer incremental data into existing processes for an improved risk assessment, deeper insights, and a better customer experience. We’re helping institutions unlock the power of open banking data by transforming transaction data into precise categories, a foundational component of cashflow analytics that feeds into the calculation of attributes and scores. These new Cashflow Attributes can be easily plugged into existing underwriting, analytic, and account management use cases. Early indicators show that Cashflow Attributes can boost predictive accuracy by up to 20%, allowing lenders to drive revenue growth while mitigating risk.2 Open banking is emerging in the industry across various use cases. Many are only just realizing the potential insights and benefits this can have to consumers and their organizations. How will you leverage open banking? Learn more about how we're helping address open banking 1Atomik Research survey of 2,005 U.S. adults online, matching national demographics. Fieldwork: March 17-21, 2024. 2Experian analysis based on GINI predictability. GINI coefficient measures income or wealth inequality within a population, with 0 indicating perfect equality and 1 indicating perfect inequality, reflecting predictive capability.

Finding a balance between providing secure financial services and user-friendly experiences is no easy task. One of the biggest hurdles? Ensuring identity authentication is robust and reliable. Let's walk through the essentials of identity authentication, its importance, and what effective solutions look like. What is identity authentication? Identity authentication is the process of proving that an individual is who they claim to be. Unlike identity verification, which simply confirms that the provided identity information is valid, identity authentication goes a step further by ensuring that the person presenting the information is indeed its rightful owner. At its core, identity authentication relies on various methods to verify identities. These methods can range from simple password checks to more sophisticated technologies like biometrics and adaptive authentication. The goal is to create multiple layers of security that make it difficult for unauthorized users to gain access. Types of authentication methods Several types of identity authentication methods are used today. Passwords and PINs are the most basic forms, but they are increasingly being supplemented or replaced by more advanced solutions like multi-factor authentication (MFA) , biometric scans, and knowledge-based authentication (KBA). Each method has its advantages and limitations, making it crucial for financial institutions to choose the right mix. Authentication vs. verification While often used interchangeably, identity verification and identity authentication serve different purposes. Identity verification solutions confirm that the provided identity information matches public records, whereas identity authentication solutions ensure that the person presenting the information is its true owner. Identity verification is typically a one-time process conducted at the beginning of a relationship, such as when opening a new bank account. On the other hand, identity authentication is an ongoing process, ensuring that each login or transaction is carried out by a legitimate user. Though different, these processes are crucial for financial institutions. They work together to provide a robust security framework that minimizes the risk of fraud while offering a seamless user experience. READ: Learn how to overcome online identity verification challenges. Why it's important for financial institutions The importance of identity authentication for financial institutions cannot be overstated. With the rise of cyber threats and sophisticated fraud schemes like synthetic identity fraud, robust identity authentication measures are more critical than ever. Enhancing security. Effective authentication significantly enhances the security of financial transactions. By preventing unauthorized access, sensitive information and financial assets are safeguarded. Advanced solutions like multi-factor authentication solutions add extra layers of protection. Building trust with customers. Robust authentication also helps build trust with customers. When users feel confident that their accounts and personal information are secure, they are more likely to engage with the institution and utilize its services. Regulatory compliance. For financial institutions, compliance with regulatory standards is paramount. Many regulations now mandate strong identity authentication measures to protect against fraud and ensure the security of financial transactions. What to look for in an identity authentication solution The ideal solution should offer a balance between security, user experience, and cost-effectiveness. Adaptive authentication solutions use machine learning algorithms to assess the risk level of each transaction. This allows for a dynamic approach to authentication, where additional checks are only required when necessary. Multi-factor authentication (MFA) solutions add an extra layer of security by requiring users to provide multiple forms of identification. This could include something they know (password), something they have (smartphone), and something they are (biometric data). Knowledge-based authentication (KBA) solutions ask users to answer questions based on their personal information. This method is particularly useful for verifying identities during online transactions and account recoveries. Experian’s Knowledge IQSM offers KBA with over 70 credit- and noncredit-based questions to help you authenticate consumers by asking noninvasive questions that can be answered quickly by the true consumer. Comprehensive identity solutions take a holistic approach by integrating various methods and technologies. Experian’s identity solutions offer a range of services, from risk-based authentication to automated identity verification, ensuring comprehensive protection. Importance of user experience. While security is paramount, user experience should not be overlooked. The ideal identity authentication solution should be seamless and user-friendly, minimizing friction during the authentication process. READ: By adopting a consumer-centric approach to digital identity, organizations can offer customers a better experience while minimizing risk. How Experian can help Identity authentication is a critical component of modern financial institutions. By implementing robust and user-friendly solutions, organizations can enhance security, build customer trust, and comply with regulatory standards. Whether it's through adaptive authentication, multi-factor authentication, or knowledge-based authentication, the goal is to create a secure and seamless experience for users. Ready to take your identity strategy to the next level? Explore Experian’s identity solutions today and discover how they can help your institution achieve its security and user experience goals. Learn more This article includes content created by an AI language model and is intended to provide general information.

According to Experian’s Automotive Market Trends Report: Q1 2024, hybrids accounted for 11.8% of new vehicle registrations, an increase from 8.8% last year.