Search Results for: synthetic id

First-party fraud is an identity-centric risk that changes over time. And the fact that no one knows the true size of first-party fraud is not the problem. It’s a symptom. First-party fraud involves a person making financial commitments or defaulting on existing commitments using their own identity, a manipulated version of their own identity or a synthetic identity they control. With the identity owner involved, a critical piece of the puzzle is lost. Because fraud “treatments” tend to be all-or-nothing and rely on a victim, the consequences of applying traditional fraud strategies when first-party fraud is suspected can be too harsh and significantly damage the customer relationship. Without feedback from a victim, first-party fraud hides in plain sight — in credit losses. As a collective, we’ve created lots of subsets of losses that nibble around the edges of first-party fraud, and we focus on reducing those. But I can’t help thinking if we were really trying to solve first-party fraud, we would collectively be doing a better job of measuring it. As the saying goes, “If you can’t measure it, you can’t improve it.” Because behaviors exhibited during first-party fraud are difficult to distinguish from those of legitimate consumers who’ve encountered catastrophic life events, such as illness and unemployment, individual account performance isn’t typically a good measurement. First-party fraud is a person-level event rather than an account-level event and needs to be viewed as such. So why does first-party fraud slip through the cracks? Existing, third-party fraud prevention tools aren’t trained to detect it. Underwriting relies on a point-in-time assessment, leaving lenders blind to intentions that may change after booking. When first-party fraud occurs, the different organizations that suffer losses attach different names to it based on their account-level view. It’s hidden in credit losses, preventing you from identifying it for future analysis. As an industry, we aren’t going to be able to solve the problem of first-party fraud as long as three different organizations can look at an individual and declare, “Never pay!” “No. Bust-out!” “No! Charge-off!” So, what do we need to stop doing? Stop thinking that it’s a different problem based on when you enter the picture. Whether you opened an account five years ago or 5 minutes ago doesn’t change the problem. It’s still first-party fraud if the person who owns the identity is the one misusing it. Stop thinking that the financial performance of an account you maintain is the only relevant data. And what do we need to start doing? See and treat first-party fraud as a continuous Leverage machine learning techniques and robust data (including your own observations) to monitor for emerging risk over Apply multiple levels of treatments to respond and tighten controls/reduce exposure as risk Define first-party fraud using a broader set of elements beyond your individual observations.

Identity-related fraud exposure and losses are increasing, and the underlying schemes are becoming more complex. To make better decisions on the need for step-up authentication in this dynamic environment, you should take a layered approach to the services you need. Some of these services include: Identity verification and reverification checks for ongoing reaffirmation of your customer identity data quality and accuracy. Targeted identity risk scores and underlying attributes designed to isolate identity theft, first-party fraud and synthetic identity. Layered, passive or more active authentication, such as document verification, biometrics, knowledge-based authentication and alternate data sources. Bad guys are more motivated, and they’re getting better at identity theft and synthetic identity attacks. Fraud prevention needs to advance as well. Future-proof your investments. More fraud prevention strategies to consider>

The second full day of Experian Vision 2018 kicked off with an inspirational message from keynote speakers Capt. Mark Kelly and Former Congresswomen Gabby Giffords, rolled into a series of diverse breakout sessions, and concluded with Super Bowl-winning quarterback Aaron Rodgers sharing tales of sports, leadership and winning. Need a recap of some of the headlines from the day? Here you go ... Retail Apocalypse? Not so fast alarmists. Yes, there are media headlines around mergers, closings and consumers adopting new ways to shop, but let me give you three reasons as to why the retail sky is not falling. There were more store openings last year than closings, and that trend is expected to continue this year with an estimated 5,500 openings by December. There continues to be a positive sales trajectory. E-commerce sales are increasing. Big department stores have seen pains, but if brands are focused on connection, relevance and convenience, there is hope. Consumers continue to spend. Subprime auto bubble? Nope. Malinda Zabritski, Sr. Director of Experian Automotive Sales, says the media likes to fixate on the subprime, but subprime financing has been on the decline, reaching record lows. Deep subprime is at .65%. Additionally, delinquency rates have also tapered. The real message? Consumers are relying on auto lenders for financing, largely due to consumer preferences to lease. The market is healthy, and while it has slowed slightly, the market is still at 7% year-over-year growth. Consumer-permissioned data is not just a value-add for thin-file consumers. Take for instance the inclusion of demand deposit accounts (DDAs). David Shellenberger, Sr. Director of Scoring and Predictive Analytics for FICO, says people who have had long relationships with their checking accounts tend to be more stable and generally sport higher credit scores. Consumers with thick, mature files can also benefit with DDA data. Consumer-permissioned data is not just about turning a “no” to a “yes.” It can also take a consumer from near-prime to prime, or from prime to super-prime. Would you want to make a credit decision with less information or more? This was the question Paul DeSaulniers, Experian Sr. Director of Product, posed to the audience as he kicked off the session on alternative data. With an estimated 100 million U.S. consumers falling below “thick-file” credit status, there is a definite need to learn more about these individuals. By leveraging alternative credit data – like short-term lending product use, rental data, public records and consumer-permissioned data – a more holistic view of these consumers is available. A few more facts: While alternative finance users tend to be more subprime, 20% are prime or better. A recent data pull revealed 20% of approved credit card users also had alternative finance data on them as well. About 2/3 of households headed by young adults are rentals. Imagine a world where the mortgage journey takes only seven to 10 days. With data and technology, we are closer than you think. Future products are underway that could master the underwriting phase in just one day, leaving the remaining days dedicated for signing disclosures, documents and wiring funds. Processes need to be firmed up, but a vision has been set. The average 30- to 45-day mortgage journey could soon be a distant memory. 97% of online banking applications that are started are abandoned. Why? Filling out lengthy forms, especially on a mobile device, is not fun. New technology, such as Experian’s Instant Form Fill, is allowing consumers to provide a name, zip and last four numbers of their social security number for an instant form fill of the rest of the application. Additionally, voice assistants are expected to increasingly facilitate research on purchases big and small. A recent study revealed nearly half of consumers perceive voice assistants to be useful. Businesses have more fraud losses than ever before. Not surprising. What is scary? An estimated 54% of businesses said they are not confident in their ability to detect fraud. Another session reported that approximately 20% of credit charge-offs are synthetic IDs, a growing pain point for all businesses. Consumers, on the other hand, say they “want visible signs of security” and “no friction.” Tough to balance, but those are today’s expectations. More Vision 2018 insights can be accessed on #ExperianVision twitter feed. Vision 2019 will be in San Antonio, Texas next May 5-8.

Synthetic identity fraud is on the rise across financial services, ecommerce, public sector, health and utilities markets. The long-term impact of synthetic identity remains to be seen and will hinge largely upon forthcoming efforts across the identity ecosystem made up of service providers, institutions and agencies, data aggregators and consumers themselves. Making measurement more challenging is the fact that much of the assumed and confirmed losses are associated with credit risk and charge offs, and lack of common and consistent definitions and confirmation criteria. Here are some estimates on the scope of the problem: Losses due to synthetic identity fraud are projected to reach more than $800 million in 2017.* Average loss per account is more than $10,000.* U.S. synthetic credit card fraud is estimated to reach $1.257 billion in 2020.* As with most fraud, there is no miracle cure. But there are best practices, and topping that list is addressing both front- and back-end controls within your organization. Synthetic identity fraud webinar> *Aite Research Group

So many insights and learnings to report after the first full day of 2017 Vision sessions. From the musings shared by tech engineer and pioneer Steve Wozniak, to a panel of technology thought leaders, to countless breakout sessions on a wide array of business topics … here’s a look at our top 10 from the day. A mortgage process for the digital age. At last. In his opening remarks, Experian President of Credit Services Alex Lintner asked the audience to imagine a world when applying for a mortgage simply required a few clicks or swipes. Instead of being sent home to collect a hundred pieces of paper to verify employment, income and assets, a consumer could click on a link and provide a few credentials to verify everything digitally. Finally, lenders can make this a reality, and soon it will be the only way consumers expect to go through the mortgage process. The global and U.S. economies are stable. In fact, they are strong. As Experian Vice President of Analytics Michele Raneri notes, “the fundamentals and technicals look really solid across the countries.” While many were worried a year ago that Brexit would turn the economy upside down, it appears everything is good. Consumer confidence is high. The Dow Jones Index is high. The U.S. unemployment rate is at 4.7%. Home prices are up year-over-year. While there has been a great deal of change in the world – politically and beyond – the economy is holding strong. The rise of the micropreneur. This term is not officially in the dictionary … but it will be. What is it? A micropreneur is a business with 0 to 4 employees bringing in no more than $200k in annual revenue. But the real story is that numbers show microbusiness are improving on many fronts when it comes to contribution to the economy and overall performance compared to other small businesses. Keep an eye on these budding business people. Fraud is running fierce. Synthetic identity losses are estimated in the hundreds of millions annually, with 50% year-over year growth. Criminals are now trying to use credit cleaners to get tradelines removed from used Synthetic IDs. Oh, and it is essential for businesses to ready themselves for “Dark Web” threats. Experts advise to harden your defenses (and play offense) to keep pace with the criminal underground. As soon as you think you’ve protected everything, the criminals will find a gap. The cloud is cool and so are APIs. A panel of thought leaders took to the main stage to discuss the latest trends in tech. Experian Global CIO Barry Libenson said, “The cloud has changed the way we deliver services to our customers and clients, making it seamless and elastic.” Combine that with API, and the goal is to ultimately make all Experian data available to its customers. Experian President of Decision Analytics Steve Platt added, “We are enabling you to tap into what you need, when you need it.” No need to “rip and replace” all your tech. Expect more regulation – and less. A panel of regulatory experts addressed the fast-changing regulatory environment. With the new Trump administration settling in, and calls for change to Dodd-Frank and the Consumer Financial Protection Bureau (CFPB), it’s too soon to tell what will unfold in 2017. CFPB Director Richard Cordray may be making a run for governor of Ohio, so he could be transitioning out sooner than the scheduled close of his July 2018 term. The auto market continues to cruise. Experian’s auto expert, Malinda Zabritski, revealed the latest and greatest stats pertaining to the auto market. A few numbers to blow your mind … U.S. passenger cars and light trucks surpassed 17 million units for the second consecutive year Most new vehicle buyers in the U.S. are 45 years of age or older Crossover and sport utility vehicles remain popular, accounting for 40% of the market in 2016 – this is also driving up finance payments since these vehicles are more expensive. There are signs the auto market is beginning to soften, but interest rates are still low, and leasing is hot. Defining alternative data. As more in the industry discuss the need for alternative data to decision, it often gets labeled as something radical. But in reality, alternative data should be simple. Experian Sr. Director of Government Affairs Liz Oesterle defined it as “getting more financial data in the system that is predicted, validated and can be disputed.” #DeathtoPasswords – could it be a reality? It’s no secret we live in a digital world where we are increasingly relying on apps and websites to manage our lives, but let’s throw out some numbers to quantify the shift. In 2013, the average U.S. consumer had 26 online accounts. By 2015, that number increased to 118 online accounts. By 2020, the average person will have 207 online accounts. When you think about this number, and the passwords associated with these accounts, it is clear a change needs to be made to managing our lives online. Experian Vice President David Britton addressed his session, introducing the concept of creating an “ultimate consumer identity profile,” where multi-source data will be brought together to identify someone. It’s coming, and all of us managing dozens of passwords can’t wait. “The Woz.” I guess you needed to be there, but let’s just say he was honest, opinionated and notes that while he loves tech, he loves it even more when it enables us to live in the “human world.” Too much wonderful content to share, but more to come tomorrow …
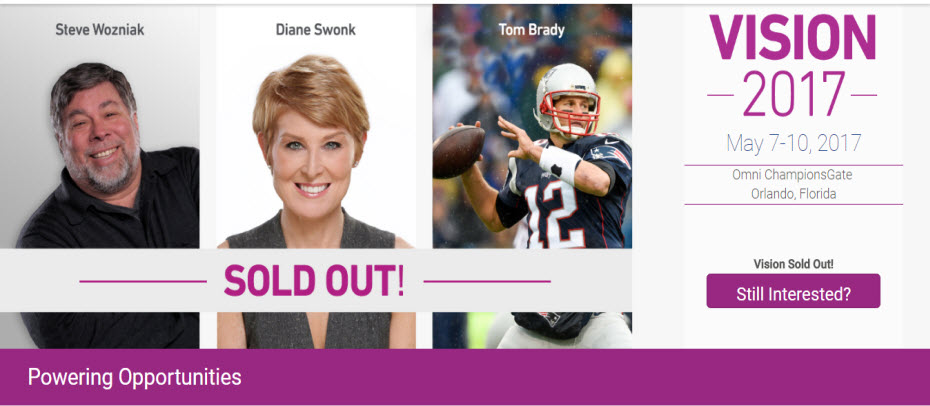
Experian’s annual Vision Conference, a four-day event designed to bring business leaders together to discuss the latest ideas and solutions surrounding targeting new markets, growing customer bases and profitability, reducing fraud and more, begins Sunday evening in Orlando, Florida. Over the course of the week, a total of 65 sessions will touch on newsworthy and breaking trends. Attendees will discover: The latest generational insights – including a first look at the coming-of-age Gen Z crowd – regarding credit scores, spend patterns and digital behaviors Multiple presentations on the economy, the mortgage market, student lending, small business forecasts and new developments in online marketplace lending Deep dives on fraud in relation to the epidemic of synthetic IDs, Know Your Customer (KYC) compliance strategies, maturing your organization to defeat fraud, and the dark web Regulatory round-ups touching on everything from the Military Lending Act (MLA), the Telephone Consumer Protection Act (TCPA), Current Expected Credit Loss (CECL) and what is emerging from the new administration Best-in-class sessions on data and analytics, modeling, virtual collections, trended data and credit marketing Intel on the state of commercial lending, the rise of the mircopreneur and the business credit profile across various life stages. Beyond a jam-packed schedule of breakout sessions, the conference will additionally host a series of general session speakers sure to educate and entertain. On Monday, Steve Wozniak, also known as “The Woz” takes the stage to talk about his experiences as co-founder of Apple Computer Inc. and his years in the emerging technology space. Diane Swonk, CEO of DS Economics, will address the crowd on Tuesday to provide details and analysis on the state of the global and U.S. economies. Finally, legendary quarterback and recent Super Bowl MVP and winner Tom Brady will speak on Wednesday to close out the event. Conference attendees can follow everything utilizing their Experian Vision app. Hot stats, pictures and event news will also be shared on multiple social handles using #ExperianVision.

It’s impossible to capture all of the insights and learnings of 36 breakout sessions and several keynote addresses in one post, but let’s summarize a few of the highlights from the first day of Vision 2016. 1. Who better to speak about the state of our country, specifically some of the threats we are facing than Leon Panetta, former Secretary of Defense and Director of the CIA. While we are at a critical crossroads in the United States, there is room for optimism and his hope that we can be an America in Renaissance. 2. Alex Lintner, Experian President of Consumer Information Services, conveyed how the consumer world has evolved, in large part due to technology: 67 percent of consumers made purchases across multiple channels in the last six months. More than 88M U.S. consumers use their smartphone to do some form of banking. 68 percent of Millennials believe within five years the way we access money will be totally different. 3. Peter Renton of Lend Academy spoke on the future of Online Marketplace Lending, revealing: Banks are recognizing that this industry provides them with a great opportunity and many are partnering with Online Marketplace Lenders to enter the space. Millennials are not the largest consumers in this space today, but they will be in the future. Sustained growth will be key for this industry. The largest platforms have everything they need in place to endure – even through an economic downturn.In other words, Online Marketplace Lenders are here to stay. 4. Tom King, Experian’s Chief Information Security Officer, addressed the crowds on how the world of information security is growing increasingly complex. There are 1.9 million records compromised every day, and sadly that number is expected to rise. What can businesses do? “We need to make it easier to make the bad guys go somewhere else,” says King. 5. Look at how the housing market has changed from just a few years ago: Inventory continues to be extraordinarily lean. Why? New home building continues to run at recession levels. And, 8.5 percent of homeowners are still underwater on their mortgage, preventing them from placing it on the market. In the world of single-family home originations, 2016 projections show that there will be more purchases, less refinancing and less volume. We may see further growth in HELOC’s. With a dwindling number of mortgages benefiting from refinancing, and with rising interest rates, a HELOC may potentially be the cheapest and easiest way to tap equity. 6. As organizations balance business needs with increasing fraud threats, the important thing to remember is that the customer experience will trump everything else. Top fraud threats in 2015 included: Card Not Present (CNP) First Party Fraud/Synthetic ID Application Fraud Mobile Payment/Deposit Fraud Cross-Channel FraudSo what do the experts believe is essential to fraud prevention in the future? Big Data with smart analytics. 7. The need for Identity Relationship Management can be seen by the dichotomy of “99 percent of companies think having a clear picture of their customers is important for their business; yet only 24 percent actually think they achieve this ideal.” Connecting identities throughout the customer lifecycle is critical to bridging this gap. 8. New technologies continue to bring new challenges to fraud prevention. We’ve seen that post-EMV fraud is moving “upstream” as fraudsters: Apply for new credit cards using stolen ID’s. Provision stolen cards into mobile wallet. Gain access to accounts to make purchases.Then, fraudsters are open to use these new cards everywhere. 9. Several speakers addressed the ever-changing regulatory environment. The Telephone Consumer Protection Act (TCPA) litigation is up 30 percent since the last year. Regulators are increasingly taking notice of Online Marketplace Lenders. It’s critical to consider regulatory requirements when building risk models and implementing business policies. 10. Hispanics and Millennials are a force to be reckoned with, so pay attention: Millennials will be 81 million strong by 2036, and Hispanics are projected to be 133 million strong by 2050. Significant factors for home purchase likelihood for both groups include VantageScore® credit score, age, student debt, credit card debt, auto loans, income, marital status and housing prices. More great insights from Vision coming your way tomorrow!

We all know that first party fraud is a problem. No one can seem to agree on the definitions of first party fraud and who is on the hook to find it, absorb the losses and mitigate the risk going forward. More often than not, first-party fraud cases and associated losses are simply combined with the relatively big “bucket” of credit losses. More importantly, the means of quickly detecting potential first-party fraud, properly segmenting it (as either true credit risk or malicious behavior) and mitigating losses associated with it usually lies within more general credit policies instead of with unique, targeted strategies designed to combat this type of fraud. In order to create a frame of reference, it’s helpful to have some quick — and yes, arguable — definitions: Synthetic identity: the fabrication of an identity with the intention of perpetrating fraudulent applications for, and access to, credit or other financial services Bust-out: the substantive building of positive credit history, followed by the intentional, high-velocity opening of several new accounts with subsequent line utilization and “never payment” Default payment: intentionally allowing credit lines to default to avoid payments Straight-roller: an account opened with immediate utilization followed by default without any attempt to make a payment Never pay: a form of straight-roller that becomes delinquent within the first few months of opening the account So what’s a risk manager to do? In my opinion, the best methods to consider in the fight against first-party fraud include analytical solutions that take multiple data points into consideration and focus on a risk-based approach. For my money, the four most important are: Models and scores developed with the proper set of identity and credit risk attributes derived from current and historic identity and account usage patterns (in other words, ANALYTICS) — Used at both the account opening and account management phases of the Customer Life Cycle, such analytics can be customized for each addressable market and specific first-party fraud threat The monitoring of individual identity elements at a portfolio level and beyond — This type of monitoring and LINK ANALYSIS allows organizations to detect the creation of synthetic identities Reasonable (e.g., one-to-one) identity and device associations over time versus a cluster of devices or coordinated attacks stemming from a single device — Knowing a customer’s device profile and behavioral usage with DEVICE INTELLIGENCE provides assurance that applications and account access are conducted legitimately Leveraging industry experts who have worked with other institutions to design and implement effective first-party fraud detection and loss-mitigation strategies — This kind of OPERATIONAL CONSULTING can save time and money in the long run and afford an opportunity to avoid mistakes By active use of these methods, you are applying a risk-based approach that will allow you to realize substantial savings in the forms of loss reduction and operational efficiencies associated with non-acquisition of high-risk first-party fraud applications, more effective credit line management of potentially high-risk accounts, better segmentation of treatment strategies and associated spend against high-risk identities, and removal of first-party fraud accounts from traditional collections processes that will prove futile. Download our recent White Paper, Data confidence realized: Leveraging customer intelligence in the age of mass data compromise, to understand how data and technology are needed to strengthen fraud risk strategies through comprehensive customer intelligence.

By: Ken Pruett I want to touch a bit on some of the third party fraud scenarios that are often top of mind with our customers: identity theft; synthetic identities; and account takeover. Identity Theft Identity theft usually occurs during the acquisition stage of the customer life cycle. Simply put, identity theft is the use of stolen identity information to fraudulently open up a new account. These accounts do not have to be just credit card related. For example, there are instances of people using others identities to open up wireless phone and utilities accounts Recent fraud trends show this type of fraud is on the rise again after a decrease over the past several years. A recent Experian study found that people who have better credit scores are more likely to have their identity stolen than those with very poor credit scores. It does seem logical that fraudsters would likely opt to steal an identity from someone with higher credit limits and available purchasing power. This type of fraud gets the majority of media attention because it is the consumer who is often the victim (as opposed to a major corporation). Fraud changes over time and recent findings show that looking at data from a historical perspective is a good way to help prevent identity theft. For example, if you see a phone number being used by multiple parties, this could be an indicator of a fraud ring in action. Using these types of data elements can make your fraud models much more predictive and reduce your fraud referral rates. Synthetic Identities Synthetic Identities are another acquisition fraud problem. It is similar to identity theft, but the information used is fictitious in nature. The fraud perpetrator may be taking pieces of information from a variety of parties to create a new identity. Trade lines may be purchased from companies who act as middle men between good consumers with good credit and perpetrators who creating new identities. This strategy allows the fraud perpetrator to quickly create a fictitious identity that looks like a real person with an active and good credit history. Most of the trade lines will be for authorized users only. The perpetrator opens up a variety of accounts in a short period of time using the trade lines. When creditors try to collect, they can’t find the account owners because they never existed. As Heather Grover mentioned in her blog, this fraud has leveled off in some areas and even decreased in others, but is probably still worth keeping an eye on. One concern on which to focus especially is that these identities are sometimes used for bust out fraud. The best approach to predicting this type of fraud is using strong fraud models that incorporate a variety of non-credit and credit variables in the model development process. These models look beyond the basic validation and verification of identity elements (such as name, address, and social security number), by leveraging additional attributes associated with a holistic identity -- such as inconsistent use of those identity elements. Account Takeover Another type of fraud that occurs during the account management period of the customer life cycle is account takeover fraud. This type of fraud occurs when an individual uses a variety of methods to take over an account of another individual. This may be accomplished by changing online passwords, changing an address or even adding themselves as an authorized user to a credit card. Some customers have tools in place to try to prevent this, but social networking sites are making it easier to obtain personal information for many consumers. For example, a person may have been asked to provide the answer to a challenge question such as the name of their high school as a means to properly identify them before gaining access to a banking account. Today, this piece of information is often readily available on social networking sites making it easier for the fraud perpetrators to defeat these types of tools. It may be more useful to use out of wallet, or knowledge-based authentication and challenge tools that dynamically generate questions based on credit or public record data to avoid this type of fraud.

The term “risk-based authentication” means many things to many institutions. Some use the term to review to their processes; others, to their various service providers. I’d like to establish the working definition of risk-based authentication for this discussion calling it: “Holistic assessment of a consumer and transaction with the end goal of applying the right authentication and decisioning treatment at the right time.” Now, that “holistic assessment” thing is certainly where the rubber meets the road, right? One can arguably approach risk-based authentication from two directions. First, a risk assessment can be based upon the type of products or services potentially being accessed and/or utilized (example: line of credit) by a customer. Second, a risk assessment can be based upon the authentication profile of the customer (example: ability to verify identifying information). I would argue that both approaches have merit, and that a best practice is to merge both into a process that looks at each customer and transaction as unique and therefore worthy of distinctively defined treatment. In this posting, and in speaking as a provider of consumer and commercial authentication products and services, I want to first define four key elements of a well-balanced risk based authentication tool: data, detailed and granular results, analytics, and decisioning. 1. Data: Broad-reaching and accurately reported data assets that span multiple sources providing far reaching and comprehensive opportunities to positively verify consumer identities and identity elements. 2. Detailed and granular results: Authentication summary and detailed-level outcomes that portray the amount of verification achieved across identity elements (such as name, address, Social Security number, date of birth, and phone) deliver a breadth of information and allow positive reconciliation of high-risk fraud and/or compliance conditions. Specific results can be used in manual or automated decisioning policies as well as scoring models, 3. Analytics: Scoring models designed to consistently reflect overall confidence in consumer authentication as well as fraud-risk associated with identity theft, synthetic identities, and first party fraud. This allows institutions to establish consistent and objective score-driven policies to authenticate consumers and reconcile high-risk conditions. Use of scores also reduces false positive ratios associated with single or grouped binary rules. Additionally, scores provide internal and external examiners with a measurable tool for incorporation into both written and operational fraud and compliance programs, 4. Decisioning: Flexibly defined data and operationally-driven decisioning strategies that can be applied to the gathering, authentication, and level of acceptance or denial of consumer identity information. This affords institutions an opportunity to employ consistent policies for detecting high-risk conditions, reconcile those terms that can be changed, and ultimately determine the response to consumer authentication results – whether it be acceptance, denial of business or somewhere in between (e.g., further authentication treatments). In my next posting, I’ll talk more specifically about the value propositions of risk-based authentication, and identify some best practices to keep in mind.

By: Heather Grover In my previous blog, I covered top of mind issues that our clients are challenged with related to their risk based authentication efforts and fraud account management. My goal in this blog is to share many of the specific fraud trends we have seen in recent months, as well as those that you – our clients and the industry as a whole – are experiencing. Management of risk and strategies to minimize fraud is on your mind. 1. Migration of fraud from Internet to call centers - and back again. Channel specific fraud is nothing new. Criminals prefer non-face-to-face channels because they can preserve anonymity, while increasing their number of attempts. The Internet has been long considered a risky channel, because many organizations have built defenses around transaction velocity checks, IP address matching and other tools. Once fraudsters were unable to pass through this channel, the call center became the new target, and path of least resistance. Not surprisingly, once the industry began to address the call center, fraud began to migrate, yet again. Increasingly we hear that the interception and compromise of online credentials due to keystroke loggers and other malware is on the rise. 2. Small business fraud on the rise. As the industry has built defenses in their consumer business, fraudsters have again migrated -- this time to commercial products. Historically, small business has not been a target for fraud, which is changing. We see and hear that, while similar to consumer fraud in many ways, small business fraud is often more difficult to detect many times due to “shell businesses” that are established. 3. Synthetic ID becoming less of an issue. As lenders tighten their criteria, not only are they turning down those less likely to pay, but their higher standards are likely affecting Synthetic ID fraud, which many times creates identities with similar characteristics that mirror “thin file” consumers. 4. Family fraud continues. We have seen consumers using the identities of members of their family in an attempt to gain and draw down credit. These occurrences are nothing new, but sadly this continues in the current economic environment. Desperate parents use their children’s identities to apply for new credit, or other family may use an elderly person’s dormant accounts with a goal of finding a short term lifeline in a bad credit situation. 5. Fraud increasing from specific geographic regions. Some areas are notorious for perpetrating fraud – not too long ago it was Nigeria and Russia. We have seen and are hearing that the new hot spots are Vietnam and other Eastern Europe countries that neighbor Russia. 6. Falsely claiming fraud. There has been an increase of consumers who claim fraud to avoid an account going into delinquency. Given the poor state of many consumers credit status, this pattern is not unexpected. The challenge many clients face is the limited ability to detect this occurrence. As a result, many clients are seeing an increase in fraud rates. This misclassification is masking what should be bad debt.

In today’s fast-evolving digital landscape, fraud prevention is no longer a reactive function, it’s a strategic imperative. As financial institutions, fintechs and government agencies face increasingly sophisticated threats, the need for scalable, transparent and AI-powered solutions has never been greater. Experian stands at the forefront of this transformation, delivering proven technology, unmatched data intelligence and regulatory-ready innovation that empowers organizations to stay ahead of fraud. One platform. Every fraud challenge. Experian’s fraud prevention ecosystem delivers scale, speed and sophistication. Unlike fragmented solutions that require patchwork integrations, Experian offers a unified platform that spans the entire fraud lifecycle from identity verification to transaction monitoring and case management. With the exciting acquisition of NeuroID, Experian is delivering more value than ever before with our shared commitment to staying ahead of emerging fraud threats. Embedding NeuroID’s behavioral expertise into Experian’s data systems and platforms is transformative. Together, we’re redefining what fraud prevention can look like in a real-time, AI-driven world. – Kathleen Peters, Chief Innovation Officer, Experian With tools like NeuroID, FraudNet and Precise ID, Experian delivers real-time decisioning and orchestration across diverse use cases. These technologies are not just buzzwords, they’re battle-tested engines driving measurable impact across millions of daily decisions. Data dominance that drives accuracy Experian’s proprietary datasets and global consortia provide unparalleled access to fraud intelligence. This data advantage enables clients to detect anomalies faster, reduce false positives and optimize fraud strategies with precision. Experian supports over five billion fraud events annually across the largest banks, fintechs and government agencies. That’s 10x more fraud and identity use cases than most competitors can manage across industries and institutions of all sizes. AI innovation with guardrails While many vendors are just beginning to explore AI, Experian has spent the last two decades embedding it into its core products and services. The launch of the Experian Assistant for Model Risk Management exemplifies this commitment. Integrated into the Ascend Platform and powered by ValidMind technology, this AI assistant streamlines model governance, enhances auditability, and accelerates deployment, all while remaining compliant with evolving regulations. Experian’s AI is not a black box. It’s explainable, auditable and developed with governance in mind. This transparency gives clients the confidence to innovate without compromising compliance. Compliance is built in, not bolted on Experian’s solutions are designed with compliance at the core. From FCRA and GLBA to KYC and CIP, Experian has a long-standing track record of aligning with regulatory frameworks. The company’s ability to demystify machine learning and make it transparent and explainable sets it apart in an industry where trust is paramount. As AI adoption accelerates, Experian’s governance models ensure that innovation doesn’t outpace accountability. Clients benefit from automated documentation, synthetic data generation and model transparency which are all essential for navigating today’s complex regulatory landscape. Empowering clients to own their outcomes Experian doesn’t just deliver tools, it empowers users. With self-service model building, clients can customize fraud strategies, optimize performance, and respond to threats in real time. This flexibility ensures that organizations aren’t just reacting to fraud, they’re proactively shaping their defenses. Experian’s fraud prevention solutions are designed to be intuitive, scalable, and user-centric, enabling teams to make smarter decisions faster. A global brand you can trust Trust is earned, not claimed. Experian’s decades-long commitment to data stewardship, innovation and client success has made it a globally recognized authority in fraud prevention. With thousands of enterprise clients and strategic partnerships, Experian delivers unmatched reliability and scale. From supporting the largest financial institutions to enabling fintech startups, Experian’s infrastructure is built to manage complexity with confidence. Thought leadership that moves the industry Experian continues to lead the conversation on fraud prevention and identity verification. As a sponsor of the 2025 Federal Identity Forum & Expo, Experian showcased its latest innovations in behavioral analytics and fraud detection, helping government agencies stay ahead of evolving threats. The company’s U.S. Identity & Fraud Report, now in its tenth year, provides actionable insights into shifting fraud patterns and consumer behavior reinforcing Experian’s role as a trusted thought leader. In a market flooded with noise, Experian delivers clarity. Its unified fraud prevention platform, backed by decades of AI innovation and regulatory expertise, empowers organizations to protect their customers, optimize operations, and lead with confidence. Experian isn’t just keeping up with the future of fraud prevention, it’s defining it. Learn more

In financial crime, fraudsters are always looking for new avenues to exploit. The mortgage industry has traditionally been a primary target for fraudsters. But with the 30-year fixed-mortgage rate average above 7.19% for the month of September, it has caused an inherent slowdown in the volume of home purchases. As a result, criminals are turning to other lucrative opportunities in mortgage transactions. They have evolved their techniques to capitalize on unsuspecting homeowners and lenders by shifting their focus from home purchases to Home Equity Line of Credit (HELOC), as they see it as a more compelling option. Understanding mortgage fraud Mortgage fraud occurs when individuals or groups intentionally misrepresent information during the mortgage application process for personal gain. The most common forms of mortgage fraud include income misrepresentation, false identity, property flipping schemes, and inflated property appraisals. Over the years, financial institutions and regulatory bodies have implemented robust measures to combat such fraudulent activities. As the mortgage industry adapts to counter established forms of fraud, perpetrators are constantly seeking new opportunities to circumvent detection. This has led to a shift in fraud trends, with fraudsters turning their focus to alternative aspects of the mortgage market. One area that has captured recent attention is HELOC fraud, also known as home equity loan fraud. HELOC fraud: An attractive target for fraudsters What is a HELOC? HELOCs are financial products that allow homeowners to borrow against the equity in their homes, often providing flexible access to funds. While HELOCs can be a valuable financial tool for homeowners, they also present an attractive opportunity for fraudsters due to their unique characteristics. HELOC fraud schemes An example of a home equity loan fraud scheme is a fraudster misrepresenting himself to deceive a credit union call center employee into changing a member’s address and phone number. Three days later, the fraudster calls back to reset the member’s online banking password, allowing the fraudster to login to the member’s account. Once logged in, the fraudster orders share drafts to be delivered to the new address they now control. The fraudster then forges three share drafts totaling $309,000 and funds them through unauthorized advances against the member’s HELOC through online banking platforms. Why HELOCs are becoming the next target for mortgage fraud Rising popularity: HELOCs have gained significant popularity in recent years, enticing fraudsters seeking out opportunities with larger potential payouts. Vulnerabilities in verification: The verification process for HELOCs might be less rigorous than traditional mortgages. Fraudsters could exploit these vulnerabilities to manipulate property valuations, income statements, or other critical information. Lack of awareness: Unlike conventional mortgages, there may be a lack of awareness among homeowners and lenders regarding the specific risks associated with HELOCs. This knowledge gap can make it easier for fraudsters to perpetrate their schemes undetected. Home equity loans do not have the same arduous process that traditional first mortgages do. These loans do not require title insurance, have less arduous underwriting processes, and do not always require the applicant to be physically present at a closing table to gain access to cash. The result is that those looking to defraud banks can apply for multiple HELOC loans simultaneously while escaping detection. Prevention and safeguards There are several preventive measures and fraud prevention solutions that can be established to help mitigate the risks associated with HELOCs. These include: Education and awareness: Homeowners and lenders must stay informed about the evolving landscape of mortgage fraud, including the specific risks posed by HELOCs. Awareness campaigns and educational materials can play a significant role in spreading knowledge and promoting caution. Enhanced verification protocols: Lenders should implement advanced verification processes and leverage data analytics and modeling thorough property appraisals, income verification, and rigorous background checks. Proper due diligence can significantly reduce the chances of falling victim to HELOC-related fraud. Collaboration and information sharing: Collaboration between financial institutions, regulators, and law enforcement agencies is essential to combat mortgage fraud effectively. Sharing information, best practices, and intelligence can help identify emerging fraud trends and deploy appropriate countermeasures. Acting with the right solution Mortgage fraud is a constant threat that demands ongoing vigilance and adaptability. As fraudsters evolve their tactics, the mortgage industry must stay one step ahead to safeguard homeowners and lenders alike. With concerns over HELOC-related fraud rising, it is vital to raise awareness, strengthen preventive measures, and foster collaboration to protect the integrity of the mortgage market. By staying informed and implementing robust safeguards, we can collectively combat and prevent mortgage fraud from disrupting the financial security of individuals and the industry. Experian mortgage is powering advanced capabilities across the mortgage lifecycle by gaining market intelligence, enhancing customer experience to remove friction and tapping into industry leading data sources to gain a complete view of borrower behavior. To learn more about our HELOC fraud prevention solutions, visit us online or request a call. *This article leverages/includes content created by an AI language model and is intended to provide general information.

The Federal Reserve (Fed) took a big step towards revolutionizing the U.S. payment landscape with the official launch of FedNow, a new instant payment service, on July 20, 2023. While the new payment network offers advantages, there are concerns that fraudsters may be quick to exploit the new real-time technology with fraud schemes like automated push payment (APP) fraud. How is FedNow different from existing payment networks? To keep pace with regions across the globe and accelerate innovation, the U.S. created a alternative to the existing payment network known as The Clearing House (TCH) Real-Time Payment Network (RTP). Fraudsters can use the fact that real-time payments immediately settle to launder the stolen money through multiple channels quickly. The potential for this kind of fraud has led financial regulators to consider measures to better protect against it. While both FedNow and RTP charge a comparable fee of 4.5 cents per originated transaction, the key distinction lies in their governance. RTP is operated by a consortium of large banks, whereas FedNow falls under the jurisdiction of the Federal Reserve Bank. This distinction could give FedNow an edge in the market. One of the advantages of FedNow is its integration with the extensive Federal Reserve network, allowing smaller local banks across the country to access the service. RTP estimates accessibility to institutions holding approximately 90% of U.S. demand deposit accounts (DDAs), but currently only reaches 62% of DDAs due to limited participation from eligible institutions. What are real-time payments? Real-time payments refer to transactions between bank accounts that are initiated, cleared, and settled within seconds, regardless of the time or day. This immediacy enhances transparency and instills confidence in payments, which benefits consumers, banks and businesses.Image sourced from JaredFranklin.com Real-time payments have gained traction globally, with adoptions from over 70 countries on six continents. In 2022 alone, these transactions amounted to a staggering $195 billion, representing a remarkable year-over-year growth of 63%. India leads the pack with its Unified Payments Interface platform, processing a massive $89.5 billion in transaction volume. Other significant markets include Brazil, China, Thailand, and South Korea. The fact that real-time payments cannot be reversed promotes trust and ensures that contracts are upheld. This also encourages the development of new methods to make processes more efficient, like the ability to pay upon receiving the goods or services. These advancements are particularly crucial for small businesses, which disproportionately bear the burden of delayed payments, amounting to a staggering $3 trillion globally at any given time. The launch of FedNow marks a significant milestone in the U.S. financial landscape, propelling the country towards greater efficiency, transparency, and innovation in payments. However, it also brings a fair share of challenges, including the potential for increased fraud. Are real-time payments a catalyst for fraud? As the financial landscape evolves with the introduction of real-time payment systems, fraudsters are quick to exploit new technologies. One particular form of fraud that has gained prominence is authorized push payment (APP) fraud. APP fraud is a type of scam where fraudsters trick individuals or businesses into authorizing the transfer of funds from their bank accounts to accounts controlled by the fraudsters. The fraudster poses as a legitimate entity and deceives the victim into believing that there is an urgent need to transfer money. They gain the victim's trust and provide instructions for the transfer, typically through online or telephone banking channels. The victim willingly performs the payment, thinking it is legitimate, but realizes they have been scammed when communication halts. APP fraud is damaging as victims authorize the payments themselves, making it difficult for banks to recover the funds. To protect against APP fraud, it's important to be cautious, verify the legitimacy of requests independently, and report any suspicious activity promptly. Fraud detection and prevention with real-time payments Advances in fraud detection software, including machine learning and behavioral analytics, make unusual urgent requests and fake invoices easier to spot — in real time — but some governments are considering legislation to ensure more support for victims. For example, in the U.K., frameworks like Confirmation of Payee have rolled out instant account detail checks against the account holder’s name to help prevent cases of authorized push payment fraud. The U.K.’s real-time payments scheme Pay.UK also introduced the Mule Insights Tactical Solution (MITS), which tracks the flow of fraudulent transactions used in money laundering through bank and credit union accounts. It identifies these accounts and stops the proceeds of crimes from moving deeper into the system – and can help victims recover their funds. While fraud levels related to traditional payments have slowly come down, real-time payment-related fraud has recently skyrocketed. India, one of the primary innovators in the space, recorded a 23% rise in fraud related to its real-time payments system in 2022. The same ACI report stated that the U.S., making up only 1.2% of all real-time payment transactions in 2022, had, for now, avoided the effects. However, “there is no reason to assume that without action, the U.S. will not follow the path to crisis levels of APP scams as seen in other markets.” FedNow currently has no specific plans to bake fraud detection into their newly launched technology, meaning the response is left to financial institutions. Fight instant fraud with instant answers Artificial Intelligence (AI) holds tremendous potential in combating the ever-present threat of fraud. With AI technologies, financial institutions can process vast amounts of data points faster and enhance their fraud detection capabilities. This enables them to identify and flag suspicious transactions that deviate from the norm, mitigating identity risk and safeguarding customer accounts. The ability of AI-powered systems to ingest and analyze real-time information empowers institutions to stay one step ahead in the battle against account takeover fraud. This type of fraud, which poses a significant challenge to real-time payment systems, can be better addressed through AI-enabled tools. With ongoing monitoring of account behavior, such as the services provided by FraudNet, financial institutions gain a powerful weapon against APP fraud. In addition to behavioral analysis, location data has emerged as an asset in the fight against fraud. Incorporating location-based information into fraud detection algorithms has proven effective in pinpointing suspicious activities and reducing fraudulent incidents. As the financial industry continues to grapple with the constant evolution of fraud techniques, harnessing the potential of AI, coupled with comprehensive data analysis and innovative technologies, becomes crucial for securing the integrity of financial transactions. Taking your next step in the fight against fraud Ultimately, the effectiveness of fraud prevention measures depends on the implementation and continuous improvement of security protocols by financial institutions, regulators, and technology providers. By staying vigilant and employing appropriate safeguards, fraud risks in real-time payment systems, such as FedNow, can be minimized. To learn more about how Experian can help you leverage fraud prevention solutions, visit us online or request a call. *This article leverages/includes content created by an AI language model and is intended to provide general information.

This article was updated on September 11, 2023. According to research, only 15% of American consumers have swapped out their go-to credit card in the past year and spend more money both online and offline with the card they designate as their top-of-wallet card. With over 578 million existing credit card accounts in the U.S., here are four top-of-wallet strategies to keep your card top of mind: Go digital In today’s digital world, the rules of customer engagement are changing – and card issuers must develop their digital capabilities, including identity resolution, to keep pace. Cardholders enjoy (and expect) the convenience of being able to apply for credit, track their purchases, make payments and view their monthly statements on-the-go. Another popular phenomenon? Digital wallets. Also known as e-wallets, these house digital versions of credit or debit cards and are stored in an app or a mobile device. Digital wallets can be used in conjunction with mobile payment systems, allowing customers to store digital coupons and pay for purchases with their smartphones. Financial institutions that digitally transform and adapt to these new dynamics can more efficiently service and retain their customers. Prioritize fraud prevention As customers’ affinity for e-commerce rises and cyberthieves grow smarter and more sophisticated, card issuers must improve their security measures and increase their focus on cutting-edge fraud management solutions. Not only should you be familiar with the many ways that criminals steal customer payment information, but you should ensure customers that you have multiple lines of defense against cyber threats. Many financial institutions have added digital “on/off switches,” allowing customers to remotely turn off their credit or debit card should they have misplaced it or suspect that they’re a victim of identity theft. With credit card fraud being the most prevalent in identity theft cases, failing to properly safeguard your customers impacts not only their experience but also your ability to grow revenue. Create a single customer view A single customer view is a consolidated, consistent and holistic representation of the data known by an organization about its customers. And according to Experian research, 68% of businesses are currently attempting to implement this type of strategy. By achieving a consolidated customer view, you can attain better consumer insight and fully understand your cardmembers’ needs and buying preferences. Careful tracking of all customer interactions enables you to target more accurately and implement effective marketing strategies. Provide incentives According to Experian research, 58% of consumers select credit cards based on rewards. The top incentives when selecting a rewards card include cashback, gas rewards and retail gift cards. Rewarding loyalty with ongoing benefits goes a long way to encourage customers to keep your credit card top of wallet but it’s also important to figure out what works – and what doesn’t. Bonus tip: Optimize credit limit management Managing credit limits is just as important as setting optimal credit limits from the get-go. Consumer credit needs will evolve over time along with their income and ability to pay. The key here is being able to identify qualified customers who can take on higher spending limits and also have a need. Leveraging advanced analytics models and a proactive credit limit management strategy can help you uncover areas of opportunity to increase wallet share and push your card toward that coveted top-of-wallet spot — or remain there. We recommend reviewing your credit limits at a regular cadence, but especially ahead of periods of increased spending such as the holiday season. In today’s competitive marketplace, getting your credit card top of wallet isn’t easy. That’s why we’re here to help. Experian’s comprehensive view of consumer credit data and best-in-class account management solutions help you target higher-spending customers and promote top-of-wallet use. Learn more