Tag: fraud

Know Your Customer (KYC) procedures are a requirement for banks and other financial institutions to collect and verify the identity of their customers. When a bank verifies the identity of another organization or its owners, the process may be called Know Your Business (KYB) instead. As part of banks’ anti-money laundering (AML) programs, KYC can help stop corruption, money laundering and terrorist financing. Creating and maintaining KYC programs is also important for regulatory compliance, reputation management and fraud prevention. READ: How to Build a Know Your Customer Checklist – Everything You Need to Know The three components of KYC programs Banks can largely determine how to set up their KYC and AML programs within the applicable regulatory guidelines. In the United States, KYC needs to happen when banks initially onboard a new customer. But it’s not a one-and-done event—ongoing customer and transaction monitoring is also important. Customer Identification Program (CIP) Creating a robust Customer Identification Program (CIP) is an essential part of KYC. At a minimum, a bank’s CIP requires it to collect the following information from new customers: Name Date of birth Address Identification number, such as a Social Security number (SSN) or Employer Identification Number (EIN) Banks' CIPs also have to use risk-based procedures to verify customers’ identities and form a reasonable belief that they know the customer's true identity.1 This might involve comparing the information from the application to the customer’s government-issued ID, other identifying documents and authoritative data sources, such as credit bureau databases. Additionally, the bank's CIP will govern how the bank: Retains the customer’s identifying information Compares customer to government lists Provides customers with adequate notices Banks can create CIPs that meet all the requirements in various ways, and many use third-party solutions to quickly collect data, detect forged or falsified documents and verify the provided information. INFOGRAPHIC: Streamlining the Digital Onboarding Process: Beating Fraud at its Game Customer due diligence (CDD) CIP and CDD overlap, but the CIP primarily verifies a customer’s identity while customer due diligence (CDD) helps banks understand the risk that each customer poses. To do this, banks try to understand what various types of customers do, what those customers’ normal banking activity looks like, and in contrast, what could be unusual or suspicious activity. Financial institutions can use risk ratings and scores to evaluate customers and then use simplified, standard or enhanced due diligence (EDD) processes based on the results. For example, customers who might pose a greater risk of laundering money or financing terrorism may need to undergo additional screenings and clarify the source of their funds. Ongoing monitoring Ongoing or continuous monitoring of customers’ identities and transactions is also important for staying compliant with AML regulations and stopping fraud. The monitoring can help banks spot a significant change in the identity of the customer, beneficial owner or account, which may require a new KYC check. Unusual transactions can also be a sign of money laundering or fraud, and they may require the bank to file a suspicious activity report (SAR). Why is KYC important in banking? Understanding and implementing KYC processes can be important for several reasons: Regulatory compliance: Although the specific laws and rules can vary by country or region, many banks are required to have AML procedures, including KYC. The fines for violating AML regulations can be in the hundreds of millions— a few banks have been fined over $1 billion for lax AML enforcement and sanctions breaching. Reputation management: In some cases, enforcement actions and fines were headline news. Banks that don’t have robust KYC procedures in place risk losing their customers' trust and respect. Fraud prevention: In addition to the regulatory requirements, KYC policies and systems can also work alongside fraud management solutions for banks. Identity verification at onboarding can help banks identify synthetic identities attempting to open money mule accounts or take out loans. Ongoing monitoring can also be important for identifying long-term fraud schemes and large fraud rings. ON-DEMAND WEBINAR: Fraud Strategies for a Positive Customer Experience KYC in a digital-first world Many financial institutions have been going through digital transformations. Part of that journey is updating the systems and tools in place to meet the expectations of customers and regulators. An Experian survey found that about half of consumers (51 percent) consider abandoning the creation of a new account because of friction or a less-than-positive experience — that increased to 69 percent for high-income households.2 The survey wasn’t specific to financial services, but friction could be a problem for banks wanting to attract new account holders. Just as access to additional data sources and machine learning help automate underwriting, financial institutions can use technological advances to add an appropriate amount of friction based on various risk signals. Some of these can be run in the background, such as an electronic Consent Based Social Security Number Verification (eCBSV) check to verify the customer’s name, SSN and date of birth match the Social Security Administration’s records. Others may require more customer involvement, such as taking a selfie that’s then compared to the image on their photo ID — Experian CrossCore® Doc Capture enables this type of verification. Experian is a leader in identity and data management Experian's identity verification solutions use proprietary and third-party data to help banks manage their KYC procedures, including identity verification and Customer Identification Programs. By bundling identity verification with fraud assessment, banks can stop fraudsters while quickly resolving identity discrepancies. The automated processes also allow you to offer a low-friction identity verification experience and use step-up authentications as needed. Learn more about Experian’s identity solutions. 1FDIC (2021). Customer Identification Program 2Experian (2023). Experian's 2023 Identity and Fraud Report

In the ever-expanding financial crime landscape, envision the most recent perpetrator targeting your organization. Did you catch them? Could you recover the stolen funds? Now, picture that same individual attempting to replicate their scheme at another establishment, only to be thwarted by an advanced system flagging their activity. The reason? Both companies are part of an anti-fraud data consortium, safeguarding financial institutions (FIs) from recurring fraud. In the relentless battle against fraud and financial crime, FIs find themselves at a significant disadvantage due to stringent regulations governing their operations. Criminals, however, operate without boundaries, collaborating across jurisdictions and international borders. Recognizing the need to level the playing field, FIs are increasingly turning to collaborative solutions, such as participation in fraud consortiums, to enhance their anti-fraud and Anti-Money Laundering (AML) efforts. Understanding consortium data for fraud prevention A fraud consortium is a strategic alliance of financial institutions and service providers united in the common goal of comprehensively understanding and combatting fraud. As online transactions surge, so does the risk of fraudulent activities. However, according to Experian’s 2023 U.S. Identity and Fraud Report, 55% of U.S. consumers reported setting up a new account in the last six months despite concerns around fraud and online security. The highest account openings were reported for streaming services (43%), social media sites and applications (40%), and payment system providers (39%). Organizations grappling with fraud turn to consortium data as a robust defense mechanism against evolving fraud strategies. Consortium data for fraud prevention involves sharing transaction data and information among a coalition of similar businesses. This collaborative approach empowers companies with enhanced data analytics and insights, bolstering their ability to combat fraudulent activities effectively. The logic is simple: the more transaction data available for analysis by artificial-intelligence-powered systems, the more adept they become at detecting and preventing fraud by identifying patterns and anomalies. Advantages of data consortiums for fraud and AML teams Participation in an anti-fraud data consortium provides numerous advantages for a financial institution's risk management team. Key benefits include: Case management resolution: Members can exchange detailed case studies, sharing insights on how they responded to specific suspicious activities and financial crime incidents. This collaborative approach facilitates the development of best practices for incident handling. Perpetrator IDs: Identifying repeat offenders becomes more efficient as consortium members share data on suspicious activities. Recognizing patterns in names, addresses, device fingerprints, and other identifiers enables proactive prevention of financial crimes. Fraud trends: Consortium members can collectively analyze and share data on the frequency of various fraud attempts, allowing for the calibration of anti-fraud systems to effectively combat prevalent types of fraud. Regulatory changes: Staying ahead of evolving financial regulations is critical. Consortiums enable FIs to promptly share updates on regulatory changes, ensuring quick modifications to anti-fraud/AML systems for ongoing compliance. Who should join a fraud consortium? A fraud consortium can benefit any organization that faces fraud risks and challenges, especially in the financial industry. However, some organizations may benefit more, depending on their size, type, and fraud exposure. Some of the organizations that should consider joining a fraud consortium are: Financial institutions: Banks, credit unions, and other financial institutions are prime targets for fraudsters, who use various methods such as identity theft, account takeover, card fraud, wire fraud, and loan fraud to steal money and information from them. Fintech companies: Fintech companies are innovative and disruptive players in the financial industry, who offer new and alternative products and services such as digital payments, peer-to-peer lending, crowdfunding, and robot-advisors. Online merchants: Online merchants are vulnerable to fraudsters, who use various methods such as card-not-present fraud, friendly fraud, and chargeback fraud to exploit their online transactions and payment systems. Why partner with Experian? What companies need is a consortium that allows FIs to collaboratively research anti-fraud and AML information, eliminating the need for redundant individual efforts. This approach promotes tighter standardization of anti-crime procedures, expedited deployment of effective anti-fraud/AML solutions, and a proactive focus on preventing financial crime rather than reacting to its aftermath. Experian Hunter is a sophisticated global application fraud and risk management solution. It leverages detection rules to screen incoming application data for identifying and preventing fraudulent activities. It matches incoming application data against multiple internal and external data sources, shared fraud databases and dedicated watch lists. It uses client-flexible matching rules to crossmatch data sources for highlighting data anomalies and velocity attempts. In addition, it looks for connections to previous suspected and known fraudulent applications. Hunter generates a fraud score to indicate a fraud risk level used to prioritize referrals. Suspicious applications are moved into the case management tool for further investigation. Overall, Hunter prevents application fraud by highlighting suspicious applications, allowing you to investigate and prevent fraud without inconveniencing genuine customers. To learn more about our fraud management solutions, visit us online or request a call. Learn more This article includes content created by an AI language model and is intended to provide general information.

Finding a reliable, customer-friendly way to protect your business against new account fraud is vital to surviving in today's digital-driven economy. Not only can ignoring the problem cause you to lose valuable money and client goodwill, but implementing the wrong solutions can lead to onboarding issues that drive away potential customers. The Experian® Identity and Fraud Report revealed that nearly 60 percent of U.S. businesses reported higher fraud losses in 2025, with many of these involving new account fraud. At the same time, problems with onboarding caused 52 percent of consumers to drop off and take their business elsewhere. In other words, your customers want protection, but they aren't willing to compromise their digital experience to get it. You need to find a way to meet both these needs when combating new account fraud. What is new account fraud? New account fraud occurs any time a bad actor creates an account in your system utilizing a fake or stolen identity. This process is referred to by different names, such as account takeover fraud, account creation fraud, or account opening fraud. Examples of some of the more common types of new account fraud include: Synthetic identity (ID) fraud: This type of fraud occurs when the scammer uses a real, stolen credential combined with fake credentials. For example, they might use someone's real Social Security number combined with a fake email. Identity theft: In this case, the fraudster uses personal information they stole to create a new scam account. Fake identity: With this type of fraud, scammers create an account with wholly fake credentials that haven't been stolen from any particular person. New account fraud may target individuals, but the repercussions spill over to impact entire organizations. In fact, many scammers utilize bots to attempt to steal information or create fake accounts en masse, upping the stakes even more. How does new account fraud work? New account fraud begins at a single weak security point, such as: Data breaches: A survey revealed that 61% of Americans have received at least one data breach notification in the past two years.1 Phishing scams: The fraudster creates an email or social media account that pretends to be from a legitimate organization or person to gain confidential information.2 Skimmers: These are put on ATMs or fuel pumps to steal credit or debit card information.2 Bot scrapers: These tools scrape information posted publicly on social media or on websites.2 Synthetic ID fraud: 80 percent of new account fraud is linked to synthetic ID fraud.3 The scammer just needs one piece of legitimate information. If they have a real Social Security number, they might combine it with a fake name and birth date (or vice versa). After the information is stolen, the rest of the fraud takes place in steps. The fake or stolen identity might first be used to open a new account, like a credit card or a demand deposit account. Over time, the account establishes a credit history until it can be used for higher-value targets, like loans and bank withdrawals. How can organizations prevent new account fraud? Some traditional methods used to combat new account fraud include: Completely Automated Public Turing Tests (CAPTCHAs): These tests help reduce bot attacks that lead to data breaches and ensure that individuals logging into your system are actual people. Multifactor authentication (MFA): MFA bolsters users' password protection and helps guard against account takeover. If a scammer tries to take over an account, they won't be able to complete the process. Password protection: Robust password managers can help ensure that one stolen password doesn't lead to multiple breaches. Knowledge-based authentication: Knowledge-based authentication can be combined with MFA solutions, providing an additional layer of identity verification. Know-your-customer (KYC) solutions: Businesses may utilize KYC to verify customers via government IDs, background checks, ongoing monitoring, and the like. Additional protective measures may involve more robust identity verification behind the scenes. Examples include biometric verification, government ID authentication, public records analysis, and more. Unfortunately, these traditional protective measures may not be enough, for many reasons: New account fraud is frequently being perpetrated by bots, which can be tougher to keep up with and might overwhelm systems. Institutions might use multiple security solutions that aren't built to work together, leading to overlap and inefficiency. Security measures may create so much friction in the account creation process that potential new customers are turned away. How we can help Experian's fraud management services provide a multi-layered approach that lets businesses customize solutions to their particular needs. Advanced machine learning analytics utilizes extensive, proprietary data to provide a unique experience that not only protects your company, but it also protects your customers' experience. Customer identification program (CIP): Experian's KYC solutions allow you to confidently identify your customers via a low-friction experience. The tools start with onboarding, but continue throughout the customer journey, including portfolio management. The tools also help your company comply with relevant KYC regulations. Cross-industry analysis of identity behavior: Experian has created an identity graph that aggregates consumer information in a way that gives companies access to a cross-industry view of identity behavior as it changes over time. This means that when a new account is opened, your company can determine behind the scenes if any part of the identity is connected to instances of fraud or presents actions not normally associated with the customer's identity. It's essentially a new paradigm that works faster behind the scenes and is part of Experian's Ascend Fraud Platform™. Multifactor authentication solutions: Experian's MFA solutions utilize low-friction techniques like two-factor authentication, knowledge-based authentication, and unique one-time password authentication during remote transactions to guard against hacking. Synthetic ID fraud protection: Experian's fraud management solutions include robust protection against synthetic ID fraud. Our groundbreaking technology detects and predicts synthetic identities throughout the customer lifecycle, utilizing advanced analytics capabilities. CrossCore®: CrossCore combines risk-based authentication, identity proofing, and fraud detection into one cloud platform, allowing for real-time decisions to be made with flexible decisioning workflows and advanced analytics. Precise ID®: The Precise ID platform lets customers choose the combination of fraud analytics, identification verification, and workflows that best meet their business needs. This includes machine-learned fraud risk models, robust consumer data assets, one-time passwords (OTPs), knowledge-based authentication (KBAs), and powerful insights via the Identity Element Network®. Interactive infographic: Building a multilayered fraud and identity strategy Account takeover fraud represents a significant threat to your business that you can't ignore. But with Experian's broad range of solutions, you can keep your systems secure while not sacrificing customer experience. Experian can keep your business secure from new account fraud Experian's innovative approach can streamline your new account fraud protection. Learn more about how our fraud management solutions can help you. Learn more References 1. https://www.prnewswire.com/news-releases/americans-are-on-high-alert-as-data-breach-fears-reach-a-breaking-point-302392550.html 2. "Identity Theft." USA.gov, December 6, 2023. https://www.usa.gov/identity-theft 3. Purcell, Michael. "Synthetic Identity Fraud: What is It and How to Combat It." Thomson Reuters, April 28, 2023. https://legal.thomsonreuters.com/blog/synthetic-identity-fraud-what-is-it-and-how-to-combat-it/

This article was updated on March 4, 2024. If you steal an identity to commit fraud, your success is determined by how long it takes the victim to find out. That window gets shorter as businesses get better at knowing when and how to reach an identity owner when fraud is suspected. In response, frustrated fraudsters have been developing techniques to commit fraud that does not involve a real identity, giving them a longer run-time and a bigger payday. That's the idea behind synthetic identity (SID) fraud — one of the fastest-growing types of fraud. Defining synthetic identity fraud Organizations tend to have different definitions of synthetic identity fraud, as a synthetic identity will look different to the businesses it attacks. Some may see a new account that goes bad immediately, while others might see a longer tenured account fall delinquent and default. The qualifications of the synthetic identity also change over time, as the fraudster works to increase the identity’s appearance of legitimacy. In the end, there is no person to confirm that fraud has occurred, in the very best case, identifying a synthetic identity is inferred and verified. As a result, inconsistent reporting and categorization can make tracking and fighting SID fraud more difficult. To help create a more unified understanding and response to the issue, the Federal Reserve and 12 fraud experts worked together to develop a definition. In 2021, the Boston Federal Reserve published the result, “Synthetic identity fraud is the use of a combination of personally identifiable information to fabricate a person or entity to commit a dishonest act for personal or financial gain."1 To break down the definition, personally identifiable information (PII) can include: Primary PII: Such as a name, date of birth (DOB), Social Security number (SSN) or another government-issued identifier. When combined, these are generally unique to a person or entity. Secondary PII: Such as an address, email, phone number or device ID. These elements can help verify a person or entity's identity. Synthetic identities are created when fraudsters establish an identity from scratch using fake PII. Or they may combine real and fake PII (I.e., a stolen SSN with a fake name and DOB) to create a new identity. Additionally, fraudsters might steal and use someone's SSN to create an identity - children, the elderly and incarcerated people are popular targets because they don't commonly use credit.4 But any losses would still be tied to the SID rather than the victim. Exploring the Impact of SID fraud The most immediate and obvious impact of SID fraud is the fraud losses. Criminals may create a synthetic identity and spend months building up its credit profile, opening accounts and increasing credit limits. The identities and behaviors are constructed to look like legitimate borrowers, with some having a record of on-time payments. But once the fraudster decides to monetize the identity, they can apply for loans and max out credit cards before ‘busting out’ and disappearing with the money. Aite-Novaric Group estimates that SID fraud losses totaled $1.8 billion in 2020 and will increase to $2.94 billion in 2024.2 However, organizations that do not identify SIDs may classify a default as a credit loss rather than a fraud loss. By some estimates, synthetic identity fraud could account for up to 20 percent of loan and credit card charge-offs, meaning the annual charge-off losses in the U.S. could be closer to $11 billion.3 Additionally, organizations lose time and resources on collection efforts if they do not identify the SID fraud. Those estimates are only for unsecured U.S. credit products. But fraudsters use synthetic identities to take out secured loans, including auto loans. As part of schemes used to steal relief funds during the pandemic, criminals used synthetic identities to open demand deposit accounts to receive funds. These accounts can be used to launder money from other sources and commit peer-to-peer payment fraud. Deposit account holders are also a primary source of cross-marketing for some financial institutions. Criminals can take advantage of vulnerable onboarding processes for deposit accounts where there’s low risk to the institution and receive offers for lending products. Building a successful SID prevention strategy Having an effective SID prevention strategy is more crucial than ever for organizations. Aside from fraud losses, consumers listed identity theft as their top concern when conducting activities online. And while 92% of businesses have an identity verification strategy in place, 63% of consumers are "somewhat confident" or "not very confident" in businesses' ability to accurately identify them online. Read: Experian's 2023 Identity and Fraud Report Many traditional fraud models and identity verification methods are not designed to detect fake people. And even a step up to a phone call for verification isn't enough when the fraudster will be the one answering the phone. Criminals also quickly respond when organizations update their fraud detection methods by looking for less-protected targets. Fraudsters have even signed their SIDs up for social media accounts and apps with low verification hurdles to help their SIDs pass identity checks.5 Understand synthetic identity risks across the lifecycle Synthetic Identities are dynamic. When lending criteria is tightened to synthetics from opening new accounts, they simply come back when they can qualify. If waiting brings a higher credit line, they’ll wait. It’s important to recognize that synthetic identity isn’t a new account or a portfolio management problem - it’s both. Use analytics that are tailored to synthetic identity Many of our customers in the financial services space have been trying to solve synthetic identity fraud with credit data. There’s a false sense of security when criteria is tightened and losses go down—but the losses that are being impacted tend to not be related to credit. A better approach to synthetic ID fraud leverages a larger pool of data to assess behaviors and data linkages that are not contained in traditional credit data. You can then escalate suspicious accounts to require additional reviews, such as screening through the Social Security Administration's Electronic Consent Based SSN Verification (eCBSV) system or more stringent document verification. Find a trusted partner Experian's interconnected data and analytics platforms offer lenders turnkey identity and synthetic identity fraud solutions. In addition, lenders can take advantage of the risk management system and continuous monitoring to look for signs of SIDs and fraudulent activity, which is important for flagging accounts after opening. These tools can also help lenders identify and prevent other common forms of fraud, including account takeovers, e-commerce fraud, child identity theft fraud and elderly fraud. Learn more about our synthetic identity fraud solutions. Learn more 1Federal Reserve Bank (2021). Defining Synthetic Identity Fraud 2Aite Novarica (2022). Synthetic Identity Fraud: Solution Providers Shining Light into the Darkness 3Experian (2022). Preventing synthetic identity fraud 4The Federal Reserve (2022). Synthetic Identity Fraud: What Is it and Why You Should Care? 5Experian (2022). Preventing synthetic identity fraud

Fraud and identity theft in the automotive industry continue to make headlines with the result bringing significant monetary losses for dealers. In 2022, more than 60% of automotive dealerships filed cases of identity theft losing three or more vehicles, with 84% saying there has been a noticeable increase in identity fraud since the pandemic. Even though dealers understand that fraud is on the rise, 66% stated they lacked adequate identity fraud protections [1]. In a recent episode of the Used Car Dealer Podcast, host Zach Klempf, spoke with Kanchana Sundaram, Experian's senior director of product and innovation for automotive, to discuss Fraud Protect, a new tool from Experian that helps dealers combat fraud. During the interview, Kanchana highlighted how dealers can use Fraud Protect to better identify potentially fraudulent behavior, without slowing down the sales process and still maintaining a positive experience for both them and the consumer. By leveraging the latest technology and advanced analytics, dealers are able to detect some of the most common fraud types that include: Third-party fraud: Fraudsters steal an individual’s identity to purchase a vehicle First-party fraud: A person knowingly misrepresents their identity or provides false information, often with the intention of not paying for the vehicle Synthetic identity fraud: Fraudsters create fake identities and build credit profiles over time before using them to finance a vehicle they do not intend to pay for The episode is now available across all major podcast platforms, click the link to watch: YouTube To learn more about Fraud Protect, visit Experian’s auto fraud prevention solutions webpage. For more information on the Used Car Dealer Podcast, visit https://www.sellyautomotive.com/podcast Facebook – @SellyAutomotive ‘X’ – @SellyAutomotive LinkedIn – @SellyAutomotive 1. https://www.elendsolutions.com/research/2022-Identity-Fraud-Survey-Report/

This article was updated on February 23, 2024. First impressions are always important – whether it’s for a job interview, a first date or when pitching a client. The same goes for financial services onboarding as it’s an opportunity for organizations to foster lifetime loyalty with customers. As a result, financial institutions are on the hunt now more than ever for frictionless online identity verification methods to validate genuine customers and maintain positive experiences during the online onboarding process. In a predominantly digital-first world, financial companies are increasingly focused on the customer experience and creating the most seamless online onboarding process. However, according to Experian’s 2023 Identity and Fraud Report, more than half of U.S. consumers considered dropping out during account opening due to friction and a less-than positive experience. And as technology continues to advance, digital financial services onboarding, not surprisingly, increases the demand for fraud protection and authentication methods – namely with digital identity (ID) verification processes. According to Experian’s report, 64% of consumers are very or somewhat concerned with online security, with identity theft being their top concern. So how can financial institutions guarantee a frictionless online onboarding experience while executing proper authentication methods and maintaining security and fraud detection? The answer? While a “frictionless” experience can seem like a bit of a unicorn, there are some ways to get close: Utilizing better data - Digital devices offer an extensive amount of data that’s useful in determining risk. Characteristics that allow the identification of a specific device, the behaviors associated with the device and information about a device’s owner can be captured without adding friction for the user. Analytics – Once the data is collected, advanced analytics uses information based on behavioral data, digital intelligence, phone intelligence and email intelligence to analyze for risk. While there’s friction in the initial ask for the input data, the risk prediction improves with more data. Document verification and biometric identity verification – Real-time document verification used in conjunction with facial biometrics, behavioral biometrics and other physical characteristics allows for rapid onboarding and helps to maintain a low friction customer journey. Financial institutions can utilize document verification to replace manual long-form applications for rapid onboarding and immediately verify new data at the point of entry. Using their mobile phones, consumers can photograph and upload identity documents to pre-fill applications. Document authenticity can be verified in real-time. Biometrics, including facial, behavioral, or other physical characteristics (like fingerprints), are low-touch methods of customer authentication that can be used synchronously with document verification. Optimize your financial services onboarding process Experian understands how critical identity management and fraud protection is when it comes to the online onboarding process and identity verification. That’s why we created layered digital identity verification and risk segmentation solutions to help legitimize your customers with confidence while improving the customer experience. Our identity verification solutions use advanced technology and capabilities to correctly identify and verify real customers while mitigating fraud and maintaining frictionless customer experiences. Learn more

While bots have many helpful purposes, they have unfortunately become a tool for malicious actors to gain fraudulent access to financial accounts, personal information and even company-wide systems. Almost every business that has an online presence will have to face and counter bot attacks. In fact, a recent study found that across the internet on a global scale, malicious bots account for 30 percent of automated internet activity.1 And these bots are becoming more sophisticated and harder to detect. What is a bot attack and bot fraud? Bots are automated software applications that carry out repetitive instructions mimicking human behavior.2 They can be either malicious or helpful, depending on their code. For example, they might be used by companies to collect data analytics, scan websites to help you find the best discounts or chat with website visitors. These "good" bots help companies run more efficiently, freeing up employee resources. But on the flip side, if used maliciously, bots can commit attacks and fraudulent acts on an automated basis. These might even go undetected until significant damage is done. Common types of bot attacks and frauds that you might encounter include: Spam bots and malware bots: Spam bots come in all shapes and sizes. Some might scrape email addresses to entice recipients into clicking on a phishing email. Others operate on social media sites. They might create fake Facebook celebrity profiles to entice people to click on phishing links. Sometimes entire bot "farms" will even interact with each other to make a topic or page appear more legitimate. Often, these spam bots work in conjunction with malware bots that trick people into downloading malicious files so they can gain access to their systems. They may distribute viruses, ransomware, spyware or other malicious files. Content scraping bots: These bots automatically scrape content from websites. They might do so to steal contact information or product details or scrape entire articles so they can post duplicate stories on spam websites. DDoS bots and click fraud bots: Distributed denial of service (DDoS) bots interact with a target website or application in such large numbers that the target can't handle all the traffic and is overwhelmed. A similar approach involves using bots to click on ads or sponsored links thousands of times, draining advertisers' budgets. Credential stealing bots: These bots use stolen usernames and passwords to try to log into accounts and steal personal and financial information. Other bots may try brute force password cracking to find one combination that works so they can gain unauthorized access to the account. Once the bot learns consumer’s legitimate username and password combination on one website, they can oftentimes use it to perform account takeovers on other websites. In fact, 15 percent of all login attempts across industries in 2022 were account takeover attacks.1 AI-generated bots: While AI, like ChatGPT, is vastly improving the technological landscape, it's also providing a new avenue for bots.3 AI can create audio and videos that appear so real that people might think they're a celebrity seeking funds. What are the impacts of bot attacks? Bot attacks and bot fraud can have a significant negative impact, both at an individual user level and a company level. Individuals might lose money if they're tricked into sending money to a fake account, or they might click on a phishing link and unwittingly give a malicious actor access to their accounts. On a company level, the impact of a bot attack can be even more widespread. Sensitive customer data might get exposed if the company falls victim to a malware attack. This can open the door for the creation of fake accounts that drain a company's money. For example, a phishing email might lead to demand deposit account (DDA) fraud, where a scammer opens a fraudulent account in a customer's name and then links it to new accounts, like new lines of credit. Malware attacks can also cause clients to lose trust in the company and take their business elsewhere.A DDoS attack can take down an entire website or application, leading to a loss of clients and money. A bot that attacks APIs can exploit design flaws to steal sensitive data. In some cases, ransomware attacks can take over entire systems and render them unusable. How can you stop bot attacks? With so much at risk, stopping bot attacks is vital. But some of the most typical defenses have core flaws. Common methods for stopping bot attacks include: CAPTCHAs: While CAPTCHAs can protect online systems from bot incursions, they can also create friction with the user process. Firewalls: To stop DDoS attacks, companies might reduce attack points by utilizing firewalls or restricting direct traffic to sensitive infrastructures like databases.4 Blocklists: These can prevent IPs associated with attacks from accessing your system entirely. Multifactor authentication (MFA): MFA requires two forms of identification or more before granting access to an account. Password protection: Password managers can ensure employees use strong passwords that are different for each access point. While the above methods can help, many simply aren't enough, especially for larger companies with many points of potential attacks. A piecemeal approach can also lead to friction on the user's side that may turn potential clients away. Our 2024 Identity and Fraud Report revealed that up to 38 percent of U.S. adults stopped creating a new account because of the friction they encountered during the onboarding process. And often, this friction is in place to try to stop fraudulent access. Incorporating behavioral analytics to combat attacks Another effective way to enhance bot detection is through the use of behavioral analytics. This technology helps track user activity and identify patterns that may suggest malicious bot behavior. By analyzing aspects such as typing speed, mouse movement and the way users interact with websites, businesses can gain real-time insights into whether a visitor is human or a bot. Behavioral analytics in fraud uses machine learning and advanced algorithms to continuously monitor and refine user behavior patterns. This allows businesses to identify bot attacks more accurately and prevent them before they cause harm. By analyzing real-time behaviors, such as how fast someone enters information or their browsing habits, businesses can flag suspicious activity that traditional methods might miss. Why partner with Experian? What companies need is fraud and bot protection with a positive customer experience. We provide account takeover fraud prevention solutions that can help protect your company from bot attacks, fraudulent accounts and other malicious attempts to access your sensitive data. Experian's approach embodies a paradigm shift where fraud detection increases efficiency and accuracy without sacrificing customer experience. We can help protect your company from bot attacks, fraudulent accounts and other malicious attempts to access your sensitive data. Learn more This article includes content created by an AI language model and is intended to provide general information. 1"Bad bot traffic accounts for nearly 30% of APAC internet traffic," SMEhorizon, June 13, 2023. https://www.smehorizon.com/bad-bot-traffic-accounts-for-nearly-30-of-apac-internet-traffic/2"What is a bot?" AWS. https://aws.amazon.com/what-is/bot/3Nield, David. "How ChatGPT — and bots like it — can spread malware," Wired, April 19, 2023. https://www.wired.com/story/chatgpt-ai-bots-spread-malware/4"What is a DDoS attack?" AWS. https://aws.amazon.com/shield/ddos-attack-protection/

Spoiler alert: Gen AI is everywhere, including the top of Experian’s list of fraud trends 2024. “The speed and complexity of fraud attacks due to new technology and sophisticated fraudsters is leaving both businesses and consumers at risk in 2024,” said Kathleen Peters, chief innovation officer at Experian Decision Analytics in North America. “At Experian, we’re constantly innovating to deliver data-driven solutions to help our customers fight fraud and to protect the consumers they serve.” To deter fraudulent activity in 2024, businesses and consumers must get tactical for their fraud fighting strategies. And for businesses, the need for more sophisticated fraud protection solutions leveraging data and technology is greater than ever before. Experian suggests consumers and businesses watch out for these big five rounding out our fraud trends 2024. Generative AI: Generative AI accelerates DIY fraud: Experian predicts fraudsters will use generative AI to accelerate “do-it-yourself” fraud ranging from deepfake content – think emails, voice and video – as well as code creation to set up scam websites. A previous blog post of ours highlighted four types of generative AI used for fraud, including fraud automation at scale, text content generation, image and video manipulation and human voice generation. The way around it? Fight AI fraud with AI as part of a multilayered fraud prevention solution. Fraud at bank branches: Bank branches are making a comeback. A growing number of consumers prefer visiting bank branches in person to open new accounts or get financial advice with the intent to conduct safer transactions. However, face-to-face verification is not flawless and is still susceptible to human error or oversight. According to an Experian report, 85% of consumers report physical biometrics as the most trusted and secure authentication method they’ve recently encountered, but the measure is only currently used by 32% of businesses to detect and protect against fraud. Retailers, beware: Not all returns are as they appear. Experian predicts an uptick in cases where customers claim to return their purchases, only for the business to receive an empty box in return. Businesses must be vigilant with their fraud strategy in order to mitigate risk of lost goods and revenue. Synthetic identity fraud will surge: Pandemic-born synthetic identities may have been dormant, but now have a few years of history, making it easier to elude detection leading to fraudsters using those dormant accounts to “bust out” over the next year. Cause-related and investment deception: Fraudsters are employing new methods that strike an emotional response from consumers with cause-related asks to gain access to consumers’ personal information. Experian predicts that these deceptive cause-related methods will surge in 2024 and beyond. How businesses and consumers feel about fraud in 2024 According to an Experian report, over half of consumers feel they’re more of a fraud target than a year ago and nearly 70% of businesses report that fraud losses have increased in recent years. Business are facing mounting challenges – from first-party fraud and credit washing to synthetic identity and the yet-to-be-known impacts generative AI may have on fraud schemes. Synthetic identity fraud has been mentioned in multiple Experian Fraud Forecasts and the threat is ever growing. As technology continues to enhance consumers’ connectedness, it also heightens the stakes for various fraud attacks. As highlighted by this list of fraud trends 2024, the ways that fraudsters are looking to deceive is increasing from all angles. “Now more than ever, businesses need to implement a multilayered approach to their identity verification and fraud prevention strategies that leverages the latest technology available,” said Peters. Consumers are increasingly at risk from sophisticated fraud schemes. Increases in direct deposit account and check fraud, as well as advanced technologies like deepfakes and AI-generated phishing emails, put consumers in a precarious position. The call to action for consumers is to remain vigilant of seemingly authentic interactions. Experian can help with your fraud strategy To learn more about Experian’s fraud prevention solutions, please visit https://www.experian.com/business/solutions/fraud-management. Download infographic Watch Future of Fraud webinar

This article was updated on February 12, 2024. The Buy Now, Pay Later (BNPL) space has grown massively over the last few years. But with rapid growth comes an increased risk of fraud, making "Buy Now, Pay Never" a crucial fraud threat to watch out for in 2024 and beyond. What is BNPL? BNPL, a type of short-term financing, has been around for decades in different forms. It's attractive to consumers because it offers the option to split up a specific purchase into installments rather than paying the full total upfront. The modern form of BNPL typically offers four installments, with the first payment at the time of purchase, as well as 0% APR and no hidden fees. According to an Experian survey, consumers cited managing spending (34%), convenience (31%), and avoiding interest payments (23%) as main reasons for choosing BNPL. Participating retailers generally offer BNPL at point-of-sale, making it easy for customers to opt-in and get instantly approved. The customer then makes a down payment and pays off the installments from their preferred account. BNPL is on the rise The fintech and online-payment-driven world is seeing a rise in the popularity of BNPL. According to Experian research, 3 in 4 consumers have used BNPL in 2023, with 11% using BNPL weekly to make purchases. The interest in BNPL also spans generations — 36% of Gen Z, 43% of Millennials, 32% of Gen X, and 12% of Baby Boomers have used this payment method. The risks of BNPL While BNPL is a convenient, easy way for consumers to plan for their purchases, experts warn that with lax checkout and identity verification processes it is a target for digital fraud. Experian predicts an uptick in three primary risks for BNPL providers and their customers: identity theft, first-party fraud, and synthetic identity fraud. WATCH: Fraud and Identity Challenges for Fintechs Victims of identity theft can be hit with charges from BNPL providers for products they have never purchased. First-party and synthetic identity risks will emerge as a shopper's buying power grows and the temptation to abandon repayment increases. Fraudsters may use their own or fabricated identities to make purchases with no intent to repay. This leaves the BNPL provider at the risk of unrecoverable monetary losses and can impact the business' risk tolerance, causing them to narrow their lending band and miss out on properly verified consumers. An additional risk lies with fraudsters who may leverage account takeover to gain access to a legitimate user's account and payment information to make unauthorized purchases. READ: Payment Fraud Detection and Prevention: What You Need to Know Mitigating BNPL risks Luckily, there are predictive credit, identity verification, and fraud prevention tools available to help businesses minimize the risks associated with BNPL. Paired with the right data, these tools can give businesses a comprehensive view of consumer payments, including the number of outstanding BNPL loans, total BNPL loan amounts, and BNPL payment status, as well as helping to detect and apply the relevant treatment to different types of fraud. By accurately identifying customers and assessing risk in real-time, businesses can make confident lending and fraud prevention decisions. To learn more about how Experian is enabling the protection of consumer credit scores, better risk assessments, and more inclusive lending, visit us or request a call. And keep an eye out for additional in-depth explorations of our Future of Fraud Forecast. Learn more Future of Fraud Forecast

It is a New Year and a new start. How about a new job? That is what thousands of employees will consider over the next month. It is also a time for employers to attract new talents, but they must be aware of different types of employment fraud. The rise of remote work has significantly increased the prevalence of remote hiring practices, from the initial job application to the onboarding process and beyond. Unfortunately, this shift has also opened the door to a surge in imposter employees, also known as ‘candidate fraud,’ posing a significant concern for organizations. How does employment identity theft happen? Instances of potential job candidates utilizing real-time deepfake video and deepfake audio, along with personally identifiable information (PII), during remote interviews to secure positions within American companies have been on the rise. The Federal Bureau of Investigation (FBI) reports that fraudulent individuals often acquire PII through fake job opening posts, which enable them to gather candidate information and resumes. Surprisingly, the tools necessary for impersonation on live video calls do not require sophisticated or expensive hardware or software. Employment identity theft can occur in several ways. Here are a few examples: Inaccurate credentials: Employers may inadvertently hire someone with false or stolen credentials if they fail to conduct comprehensive background checks. When the employer discovers the deception, it can be challenging to trace the true identity of the person they unknowingly hired. Limited-term job offers: Some industries offer temporary job opportunities in distant locations. Individuals with criminal backgrounds may steal victims' identities to apply for these jobs, hoping that their crimes will go unnoticed until after the job is complete. Perpetrated by colleagues: In rare instances, jealous colleagues or coworkers can commit employment identity theft. They may steal a coworker's information during a data breach and sell it on the dark web or use the victim's credentials to frame them for fraudulent workplace actions. Preventing employment identity theft In addition to the reported cases of imposter employee fraud, it is crucial to acknowledge the potential for other scams that exploit new technologies and the prevalence of remote work. Malicious cyber attackers could secure employment using stolen credentials, enabling them to gain unauthorized access to sensitive data or company systems. A proficient hacker possessing the necessary IT skills may find it relatively easy to leverage social engineering techniques during the hiring process. Consequently, the reliability of traditional methods for employee verification, such as face-to-face interactions and personal recognition, is diminishing in the face of remote work and the technological advancements that enable individuals to manipulate their appearance, voice, and identity. To mitigate risks associated with hiring imposters, it is imperative to incorporate robust measures into the recruitment process. Here are some key considerations: Establish clear policies and employment contracts: Clearly communicate your organization's policies regarding moonlighting in employment contracts, employee handbooks, or other official documents. Confidentiality and non-compete agreements: Implement confidentiality and non-compete agreements to protect your company's sensitive information and intellectual property. Monitoring: Automate employment and income verification of your employees. Provide training on cybersecurity best practices: Educate employees about cyber-attacks and identity scams, such as phishing scams, through seminars and workplace training sessions. Implement robust security measures: Use firewalls, encrypt sensitive employee information, and limit access to personal data. Minimize the number of employees who have access to this information. Thoroughly screen new employees: Verify the accuracy of Social Security numbers and other information during the hiring process. Conduct comprehensive background checks, including checking bank account information and credit reports and fight against synthetic identities. Offer identity theft protection as a benefit: Consider providing identity theft protection services to your employees as part of their benefits package. These services can detect and alert victims of potential identity theft, facilitating a fast response. The new era of remote work necessitates a fresh perspective on the hiring process. It is crucial to reevaluate HR practices and leverage AI fraud detection technologies to ensure that the individuals you hire, and employ are who they claim to be, guarding against the infiltration of imposters. Navigating employment fraud with effective solutions Employment fraud presents significant risks and challenges for employers, including conflicts of interest, reputation damage, and breaches of confidentiality. By taking the right preventative measures, you can safeguard your organization and employees. Streamlining the hiring process is essential to remain competitive. But how do you balance the need for speed and ease of use with essential ID checks? By combining the best data with our automated ID verification processes, Experian helps you protect your business and onboard new talents efficiently. Our best-in-class solutions employ device recognition, behavioral biometrics, machine learning and global fraud databases to spot and block suspicious activity before it becomes a problem. Learn more about preventing employement fraud *This article includes content created by an AI language model and is intended to provide general information.

Meeting Know Your Customer (KYC) regulations and staying compliant is paramount to running your business with ensured confidence in who your customers are, the level of risk they pose, and maintained customer trust. What is KYC?KYC is the mandatory process to identify and verify the identity of clients of financial institutions, as required by the Financial Conduct Authority (FCA). KYC services go beyond simply standing up a customer identification program (CIP), though that is a key component. It involves fraud risk assessments in new and existing customer accounts. Financial institutions are required to incorporate risk-based procedures to monitor customer transactions and detect potential financial crimes or fraud risk. KYC policies help determine when suspicious activity reports (SAR) must be filed with the Department of Treasury’s FinCEN organization. According to the Federal Financial Institutions Examinations Council (FFIEC), a comprehensive KYC program should include:• Customer Identification Program (CIP): Identifies processes for verifying identities and establishing a reasonable belief that the identity is valid.• Customer due diligence: Verifying customer identities and assessing the associated risk of doing business.• Enhanced customer due diligence: Significant and comprehensive review of high-risk or high transactions and implementation of a suspicious activity-monitoring system to reduce risk to the institution. The following organizations have KYC oversight: Federal Financial Institutions Examinations Council (FFIEC), Federal Reserve Board, Federal Deposit Insurance Corporation (FDIC), national Credit Union Administration (NCUA), Office of the Comptroller of the Currency (OCC) and the Consumer Financial Protection Bureau (CFPB). How to get started on building your Know Your Customer checklist 1. Define your Customer Identification Program (CIP) The CIP outlines the process for gathering necessary information about your customers. To start building your KYC checklist, you need to define your CIP procedure. This may include the documentation you require from customers, the sources of information you may use for verification and the procedures for customer due diligence. Your CIP procedure should align with your organization’s risk appetite and be comply with regulations such as the Patriot Act or Anti-money laundering laws. 2. Identify the customer's information Identifying the information you need to gather on your customer is key in building an effective KYC checklist. Typically, this can include their first and last name, date of birth, address, phone number, email address, Social Security Number or any government-issued identification number. When gathering sensitive information, ensure that you have privacy and security controls such as encryption, and that customer data is not shared with unauthorized personnel. 3. Determine the verification method There are various methods to verify a customer's identity. Some common identity verification methods include document verification, facial recognition, voice recognition, knowledge-based authentication, biometrics or database checks. When selecting an identity verification method, consider the accuracy, speed, cost and reliability. Choose a provider that is highly secure and offers compliance with current regulations. 4. Review your checklist regularly Your KYC checklist is not a one and done process. Instead, it’s an ongoing process that requires periodic review, updates and testing. You need to periodically review your checklist to ensure your processes are up to date with the latest regulations and your business needs. Reviewing your checklist will help your business to identify gaps or outdated practices in your KYC process. Make changes as needed and keep management informed of any changes. 5. Final stage: quality control As a final step, you should perform a quality control assessment of the processes you’ve incorporated to ensure they’ve been carried out effectively. This includes checking if all necessary customer information has been collected, whether the right identity verification method was implemented, if your checklist matches your CIP and whether the results were recorded correctly. KYC is a vital process for your organization in today's digital age. Building an effective KYC checklist is essential to ensure compliance with regulations and mitigate risk factors associated with fraudulent activities. Building a solid checklist requires a clear understanding of your business needs, a comprehensive definition of your CIP, selection of the right verification method, and periodic reviews to ensure that the process is up to date. Remember, your customers' trust and privacy are at stake, so iensuring that your security processes and your KYC checklist are in place is essential. By following these guidelines, you can create a well-designed KYC checklist that reduces risk and satisfies your regulatory needs. Taking the next step Experian offers identity verification solutions as well as fully integrated, digital identity and fraud platforms. Experian’s CrossCore & Precise ID offering enables financial institutions to connect, access and orchestrate decisions that leverage multiple data sources and services. By combining risk-based authentication, identity proofing and fraud detection into a single, cloud-based platform with flexible orchestration and advanced analytics, Precise ID provides flexibility and solves for some of financial institutions’ biggest business challenges, including identity and fraud as it relates to digital onboarding and account take over; transaction monitoring and KYC/AML compliance and more, without adding undue friction. Learn more *This article includes content created by an AI language model and is intended to provide general information.

Financial institutions are under increasing pressure to grow deposits and onboard more demand deposit accounts (DDA). But as demand increases, so do fraud attempts from scammers. While a robust mitigation effort is needed to stop fraud, this same effort can also drive away potential clients. In fact, 37 percent of U.S. adults said that they abandoned opening an account online due to experiencing friction. This leaves institutions in a unique quandary: how do they stop DDA fraud without scaring away potential clients? The answer lies in utilizing robust, machine learning tools that can help you navigate fraud attempts without increasing onboarding friction. Chris Ryan, Go to Market Lead for Experian Identity and Fraud, shares his thoughts on demand deposit account fraud and which decisioning tools can best combat it. Q: What is a demand deposit account and how is it used? "Demand deposit is just your basic checking account," Ryan explains." The funds are deposited and held by an institution, which enables you to spend those assets or resources, whether it be through checks, debit cards, person-to-person, Automated Clearing House (ACH) — all the things we do every day as consumers to manage our operating budget." Q: What is demand deposit account fraud? "There are two different ways that demand deposit account fraud works," Ryan says. "One is with existing account holders, and the other is with the account opening process.” When fraud affects existing account holders, it typically involves tricking an account holder into sending money to a scammer or using fraudulent actions, like phishing emails or credit card skimmers, to gain access to their accounts. There is also a resurgence in fraud involving duplication, theft and forgery of paper checks, Ryan explains. Fraud impacting the account opening process occurs when scammers originate new DDAs. This can work in a variety of ways, such as these three examples: A scammer steals your identity and opens an account at the same bank where you have a home equity loan. They link their DDA to your line of credit, transferring your money into their new account and withdrawing the funds. A scammer uses a synthetic identity (SID) to open a fraudulent DDA. They will then use this new DDA to open more lucrative accounts that the institution cross-sells to them. A scammer uses a stolen or SID to open “mule” accounts to receive funds they dupe consumers into sending through fake relationship schemes, bogus merchandise sales and dozens of similar scams. While both types of fraud need to be dealt with, account opening fraud can have especially large repercussions for lenders or financial institutions. Q: What are the consequences of DDA fraud for organizations? "Fraud hurts in a number of ways," Ryan explains. "There are direct losses, which is the money that criminals take from our financial system. Under most circumstances, the financial institution replaces the money, so the consumer doesn’t absorb the loss, but the money is still gone. That takes money away from lending, community engagement and other investments we want banks to make. The direct losses are what most people focus on." But there are even more repercussions for institutions beyond losing money, and this can include the attempts that institutions put into place to stop the fraud. "Preventing fraud requires some friction for the end consumer," Ryan says. "The volume of fraudulent attempts is overwhelmingly large in the DDA space. This forces institutions to apply more friction. The friction is costly, and it often drives would-be-customers away. The results include high costs for the institutions and low booking rates. At the same time, institutions are hungry for deposit money right now. So, it's kind of a perfect storm." Q: What is the impact of DDA fraud on customer experience? Experian’s 2023 Identity and Fraud Report revealed that up to 37 percent of U.S. adults in the survey had abandoned a new account entirely in the previous six months because of the friction they encountered during onboarding. And 51 percent reported considering abandoning the process because of problems they encountered. Unfortunately, fraud mitigation and deposit fraud detection efforts can end up driving customers away. "People can be impatient," Ryan says, "and in the online world, a competing product is a mouse-click away. So, while it is tempting to ask new applicants for more information, or further proof of identity, that conflicts with their need for convenience and can impact their experience.” Companies looking for cheap and fast mitigation can end up impeding customers trying to onboard to sweep out the bad actors, Ryan explains. "How do you get the bad people without interrupting the good people?" Ryan asks. "That's the million-dollar question." Q: What are some other problems with how organizations traditionally combat DDA fraud? Unfortunately, traditional attempts to combat DDA fraud are inefficient due to the fragmentation of technology. Ryan says this was revealed by Liminal, an industry analyst think tank. "Nearly half of institutions use four-or-more-point solutions to manage identity and fraud-related risk," Ryan explains. "But all of those point solutions were meant to work on their own. They weren't developed to work together. So, there's a lot of overlap. And in the case of fraud, there's a high likelihood that the multiple solutions are going to find the same fraud. So, you create a huge inefficiency." To solve this challenge, institutions need to shift to integrated identity platforms, such as Experian CrossCore®. Q: How is Experian trying to change the way organizations approach DDA fraud? Experian is pushing a paradigm shift for institutions that will increase fraud detection efficiency and accuracy, without sacrificing customer experience. "Organizations need to start thinking of identity through a different lens," Ryan says. Experian has developed an identity graph that aggregates consumer information in a manner that reaches far beyond what an institution can create on its own. "Experian is able to bring the entire breadth of every identity presentation we see into an identity graph," Ryan says. "It's a cross-industry view of identity behavior." This is important because people who commit fraud manipulate data, and those manipulations can get lost in a busy marketplace. For example, Ryan explains, if you're newly married, you may have recently presented your identity using two different surnames: one under your maiden name and one under your married name. Traditional data sources may show that your identity was presented twice, but they won’t accurately reflect the underlying details; like the fact that different surnames were used. The same holds true for thousands of other details seen at each presentation but not captured in a way that enables changes over time to be visible, such as information related to IP addresses, email accounts, online devices, or phone numbers. "Our identity graph is unlocking the details behind those identity presentations," Ryan says. "This way, when a customer comes to us with a DDA application, we can say, 'That's Chris's identity, and he's consistently presenting the same information, and all that underlying data remains very stable.'" This identity graph, part of Experian's suite of fraud management solutions — also connects unique identity details to known instances of fraud, helping catch fraudulent attempts much faster than traditional methods. "Let's say you and your spouse share an address, phone numbers, all the identity details that married couples typically share," Ryan explains. "If an identity thief steals your identity and uses it along with a brand-new email and IP address not associated with your spouse, that might be concerning. However, perhaps you started a new job, and the email/IP data is legitimate. Or maybe it’s a personal email using a risky internet service provider that shares a format commonly used by a known ring of identity thieves. Traditional data might flag the email and IP information as new, but our identity graph would go several layers deeper to confirm the possible risks that the new information brings. Q: Why is this approach superior to traditional methods of fraud detection? "Historically, organizations were interested in whether an identity was real,” Ryan says. "The next question was if the provided data (I.e., addresses, date of birth, Social Security numbers, etc.) have been historically associated with the identity. Last, the question would be whether there’s known risk associated with any of the identity components.” The identity graph turns that approach upside down. "The identity graph allows us to pull in insights from past identity presentations, " Ryan says. "Maybe the current presentation doesn’t include a phone number. Our identity graph should still recognize previously provided phone numbers and the risks associated with them. Instead of looking at identity as a small handful of pieces of data that were given at the time of the presentation, we use the data given to us to get to the identity graph and see the whole picture." Q: How are businesses applying this new paradigm? The identity graph is part of Experian's Ascend Fraud Platform™ and a full suite of fraud management solutions. Experian's approach allows companies to clean out fraud that already occurred and stop new fraudulent actors before they're onboarded. "Ideally, you want to start with cleaning up the house, and then figure out how to protect the front door," Ryan says. In other words, institutions can start by applying this view to recently opened accounts to identify problematic identities that they missed. The next step would be to bring these insights into the new account onboarding process. Q: Is this new fraud platform accessible to both small and large businesses? The Ascend Fraud Platform will support several use cases that will bring value to a broad range of businesses, Ryan explains. It can not only enable Experian experts to build and deliver better tools but can enable self-serve analytical development too. "Larger organizations that have robust, internal data science capabilities will find that it’s an ideal environment for them to work in," Ryan says. "They can add their own internal data assets to ours, and then have a better place to develop analytics. Today, organizations spend months assembling data to develop analytics internally. Our Ascend Fraud Platform will reduce the timeline of the data assembly and analytical development process to weeks, and speed to market is critical when confronting continually changing fraud threats. "But for customers who have less robust analytical teams, we're able to do that on their behalf and bring solutions out to the marketplace for them," Ryan explains. Q: What type of return on investment (ROI) are businesses experiencing? "Some customers recover their investment in days," Ryan says. "Part of this is from mitigating fraud risks among recently opened accounts that slipped through existing defenses.” "In addition to reducing losses, institutions we're working with are also seeing potentially millions of dollars a month in additional bookings, as well as significant cost savings in their account opening processes," Ryan says. "We're able to help clients go back and audit the people who had fallen out of their process, to figure out how to fine-tune their tools to keep those people in," Ryan says. “By reducing risks among existing accounts, better protecting the front door against future fraud, and growing more efficiently, we’re helping clients Q: What are Experian's plans for this service? "We're working with top-tier financial institutions on the do-it-yourself techniques," Ryan says. "In parallel, we're launching our first offerings that are created for the broader marketplace. That will start with the portfolio review capability, along with making the most predictive attributes available through our integrated identity resolution platform. And while the Ascend Fraud Platform has a strong use case for DDA fraud, its uses extend beyond that to small business lending and other products. In fact, Experian offers an entire suite of fraud management solutions to help keep your DDA accounts secure and your customers happy. Experian can help optimize your DDA fraud detection Experian is revolutionizing the approach to combating DDA fraud, helping institutions create a faster onboarding process that retains more customers, while also stopping more bad actors from gaining access. It's a win-win for everyone. Experian's full suite of fraud management solutions can optimize your business's DDA fraud detection, from scrubbing your current portfolio to gatekeeping bad actors before they're onboarded. Learn more Speak with a specialist About our expert: Chris Ryan has over 20 years of experience in fraud prevention and uses this knowledge to identify the most critical fraud issues facing individuals and businesses in North America, and he guides Experian’s application of technology to mitigate fraud risk.

In today's fast-paced digital world, the risk of fraud across all industries is a constant threat. The traditional methods of fraud detection are no longer sufficient, as fraudsters become increasingly sophisticated in their attacks. However, with artificial intelligence (AI) and machine learning (ML) solutions, financial institutions can stay one step ahead of fraudsters. AI and machine learning-equipped fraud detection tools have the ability to identify suspicious activity and patterns of fraud that are imperceptible to the human brain. In this blog post, we’ll dive into the significance of AI and machine learning in fraud detection and how these solutions are uniquely equipped to handle the demands of modern-day risk management. Understanding artificial intelligence and machine learning AI and machine learning solutions are transformative technologies that are reshaping the landscape of many industries. AI, at its core, is a field of computer science that simulates human intelligence in machines, enabling them to learn from experience and perform tasks that normally require human intellect. Machine learning, a subset of AI, is the science of getting computers to learn and act like humans do, but with minimal human intervention. They can analyze vast amounts of data within seconds, identifying patterns and trends that would be impossible for a human to recognize. When it comes to fraud detection, this ability is invaluable. Advantages of fraud detection using machine learning AI and machine learning have several benefits that make them valuable in fraud detection. One significant advantage is that these technologies can recognize patterns that are too complex for humans to identify. By running through a vast set of data points, these solutions can pinpoint anomalous behavior, and thereby prevent financial losses. AI analytics tools are adept at monitoring complex networks, detecting the dispersion of attacks that may involve multiple individuals and entities, and correlating activity patterns that would otherwise be hidden. Machine learning algorithms can take these patterns and turn them into mathematical models that help identify instances of fraud before the damage takes place. Secondly, they continuously learn from new data, which allows them to become more efficient in identifying fraud as they process more data. Thirdly, they automate fraud mitigation processes, which significantly reduces the need for manual interventions that may consume valuable time and resources. Another significant benefit of machine learning is its analytics capabilities, which allow organizations to gain valuable insights into customer behavior and fraud patterns. With AI analytics, they can detect and investigate fraudulent activities in real-time, and combine it with other tools to help detect and mitigate fraud risk. For example, in financial services, AI fraud detection can help banks and financial service providers detect and prevent fraud in their systems, add value to their services and improve customer satisfaction. The future of fraud detection and machine learning The rate at which technology is evolving means that machine learning and AI fraud detection will become increasingly important in the future. In the next few years, we can expect a more sophisticated level of fraud detection using unmanned machine systems, robotics process automation, and more. Ultimately, this will improve the efficiency and effectiveness of fraud detection. AI-based fraud management solutions are taking center stage. Organizations must leverage advanced machine learning and AI analytics solutions to prevent and mitigate cyber risks and comply with regulatory mandates. The benefits extend far beyond the financial bottom line to improving the safety and security of customers. AI and machine learning solutions offer accurate, efficient and proactive routes to managing the risk of fraud in an ever-changing environment. How can Experian® help Integrating machine learning for fraud detection represents a significant advancement in cybersecurity. Fraud management solutions detect, prevent and manage fraud across all industries, including financial services, healthcare and telecommunications. With the advancement of technology, fraud management solutions now integrate machine learning to improve their processes. Experian® provides fraud prevention solutions, including machine learning models and AI analytics, which can help more effectively mitigate fraud risk, streamline fraud investigations and create a more secure digital environment for all. With Experian’s AI analytics, risk mitigation tools and fraud management solutions, organizations can stay one step ahead of fraudsters and protect their brand reputation, customer trustworthiness and corporate data. Embracing these solutions can save organizations from significant losses, reputational damage and regulatory scrutiny. To learn more about how to future-proof your business and safeguard your customers from fraud, check out Experian’s robust suite of fraud prevention solutions. Want to hear what our industry experts think? Check out this on-demand webinar on artificial intelligence and machine learning strategies. Learn more Watch webinar *This article includes content created by an AI language model and is intended to provide general information.

Sometimes logging into an account feels a bit like playing 20 questions. Security is vital for a positive customer experience, and engaging the right identity verification strategies is essential to proactive fraud prevention. For financial institutions and businesses, secure authentication is more important than ever. It is imperative for customer safety – which drives retention and loyalty – and your bottom line – as fraud has determinantal effects on and off the balance sheet. Information sharing has proliferated, as has the number of times consumers are prompted to provide access to sensitive information. While today’s consumer has grown accustomed to providing such information, there’s also a heightened demand for security. According to Experian’s 2023 U.S. Identity and Fraud Report, nearly two-thirds (64%) of consumers say they’re very or somewhat concerned with online safety, listing identity theft, stolen card information and online privacy as top concerns. Customers want to know who they are providing access to and whether that entity will have their safety in mind. From a business perspective, one way to ensure that only the right people can get in is by using (KBA). KBA takes traditional authentication methods, like passwords and Personal Identification Numbers (PINs), one step further by creating an additional layer of security through collecting private facts from each user. In this post, we'll look at how KBA works, what its benefits are as a form of identity verification, and how it can improve customer trust. Introducing Knowledge Based Authentication (KBA): What it is and how it works Knowledge Based Authentication can be part of a multifactor authentication solution and is one way to stay on top of privacy and security for your customers – existing and new. KBA is a feature designed to protect online accounts by verifying the account holder’s identity. It involves answering a series of personal questions, such as mother's maiden name or first pet's name, that only the account holder should know. This system has become increasingly popular due to its effectiveness in preventing fraud and identity theft. With KBA, businesses and individuals can have peace of mind that their information is protected by a reliable authentication system that is difficult for unauthorized users to breach. Benefits of implementing KBA and a multifactor authentication strategy By implementing KBA into your business, customers experience an additional layer of security by verifying the identity of users through personalized questions. This reduces the risk of fraud and enhances customer trust and confidence. Secondly, it improves the customer experience by making the authentication process faster and user-friendly. Lastly, KBA reduces costs by automating the authentication process and reducing the need for manual intervention. However, KBA is just one facet of an ideal strategy. Multifactor authentication provides confidence while reducing friction. Risk-based authentication tools allow organizations to assess risk to apply the appropriate level of security. Factors to consider adding to your authentication processes include: Generating unique one-time passwords (OTPs): By creating a new OTP for each transaction, you can increase the level of security. Confirm device ownership: A multifactored approach applies device intelligence checks to increase confidence that the message is reaching the correct user. Maintain low friction with secondary options: If the OTP fails or can’t be attempted by the user, working with a provider who allows an automatic default to another authentication service, such as a knowledge-based authentication solution, decreases end-user friction. Identifying potential security risks associated with KBA KBA relies on personal information that may easily be discovered via social media and other public records, which makes it vulnerable to fraud and identity theft. This highlights the need for a multilayered fraud and identity solution. The landscape of digital security is constantly changing, leveraging an arsenal of fraud and identity prevention strategies, like document verification, one-time passcode, and various identity authentication and verification measures, is critical for keeping your customers and business safe. Commonly used technologies for enhancing KBA security With the rising need for secure authentication, KBA systems have become increasingly popular. However, cyberthreats evolve at an alarming rate, making it imperative to stay current with the latest fraud schemes and how to enhance and supplement your security. Biometrics, like facial recognition and fingerprint scans, as a tactic is gaining traction, as evidenced by “85% of consumers report physical biometrics as the most trusted and secure authentication method they have recently encountered,” according to Experian’s 2023 U.S. Identity and Fraud Report. Additionally, machine learning algorithms detect patterns and anomalies in user behavior and flag any potential security breaches. Multi-factor authentication is another tool that adds an extra layer of security by requiring users to provide multiple forms of identification before logging in. Keeping up with these and other technological advancements can help ensure your KBA system stays one step ahead of potential cyberattacks. Interestingly, there’s a disconnect between the technologies consumers feel safe with and/or are prepared to use versus the technologies and strategies that organizations implement. According to the U.S. Identity and Fraud Report, biometrics are only currently used by 33% of businesses to detect and protect against fraud. An opportunity for business differentiation and driving customer loyalty through a better customer experience may be tapping into some of these lesser used – but sought after – technologies. Compliance with industry standards regarding KBA Ensuring that your system complies with industry standards regarding KBA is crucial for protecting sensitive information from unauthorized access. By implementing the following tips, you can stay ahead of the game and safeguard your organization's data. Analyze your system's current authentication methods and evaluate if they meet industry standards. Additionally, follow standard guidelines for data storage and encryption, limit access to only authorized personnel, and y current with regulations. Lastly, conduct frequent security audits and perform vulnerability tests to identify and address any potential threats. Knowledge-based authentication offers a robust security solution for businesses of all sizes, and incorporating KBA as part of a multifactor authentication strategy is a winning course of action. It provides an added layer of protection for personal data, encourages user accountability, and safeguards against unauthorized access. By leveraging appropriate KBA technologies and maintaining compliance with industry standards, it is possible to create a secure system for customers that gives you peace of mind for your business and bottom line. Experian can help you with knowledge-based authentication offerings, a multifactor authentication strategy and everything in between to enhance your existing authentication process without causing user fatigue. Increase your pass rates, confirm device ownership and add security to risky or high-value transactions, all while executing identity verification and fraud detection to protect your business from risk. The most important step is getting started. Learn more
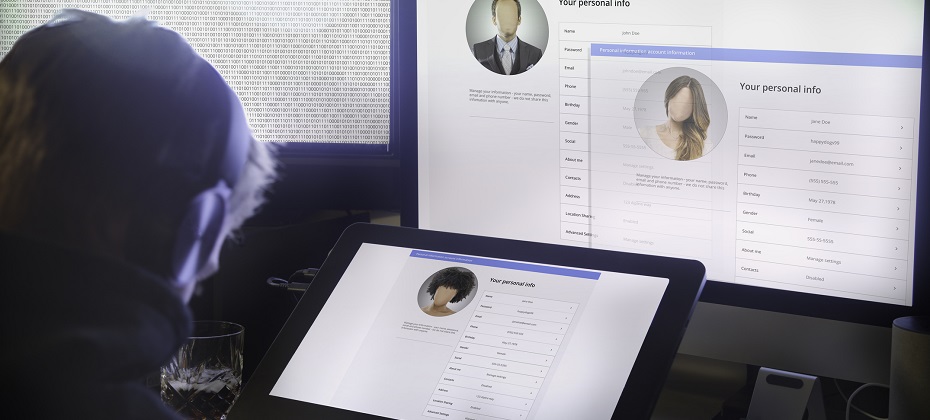
It's that magical time of the year! The holiday season is fast approaching, and folks everywhere are gearing up for festive travels and family reunions. Unfortunately, holiday travel can sometimes lead to unforeseen circumstances, such as fraudulent activities orchestrated by scammers who impersonate property owners on well-known vacation rental platforms. These fraudsters employ schemes designed to deceive unsuspecting travelers into making payments through unsecured channels, resulting in significant financial losses for the gullible victims. Digital identity and hotel fraud Airline and hotel fraud encompasses illicit activities aimed at airlines, hotels, booking platforms, and other travel accommodation services, including car rentals and excursions. These services often utilize loyalty programs to incentivize repeat patronage through point-based rewards. The widespread adoption of such loyalty programs has extended their appeal beyond the travel and hospitality sectors, consequently attracting fraudulent activities. Perpetrators of airline and hospitality fraud employ a range of tactics and different techniques to execute their schemes, leveraging various online forums, marketplaces, shops, and public messaging platforms. Hotels are custodians of valuable guest data, encompassing contact information and payment details. Their operational model involves serving a large pool of potential customers who are making limited visits. Consequently, compromising a hospitality employee's account could grant an identity thief access to millions of consumer records. Moreover, hotel employees are frequent targets of foreign governments aiming to procure confidential travel records to facilitate the tracking of specific individuals and groups. In contrast, restaurants primarily store transaction records with fewer customer details. However, the landscape is evolving as more establishments adopt online ordering capabilities and loyalty programs. At present, cybercriminals typically focus on the high volume of point-of-sale transactions. As travel booms, fraudsters find new paths According to a recent Deloitte survey, Intent to travel between Thanksgiving and mid-January is up across all age and income groups. While reconnecting with friends and family remains paramount to travel during the holidays, fewer Americans are restricting their travel to visiting loved ones. The share of travelers planning to stay in hotels surged to 56%. Fraudsters will always take advantage of current circumstances, and with more people traveling again, they have taken notice — and action. The following techniques have been identified as the most employed by cybercriminals to target customers of airlines, hotels, and hospitality-related organizations: Travel-themed phishing and fraudulent travel agency operations, sales, and advertisements of travel fraud-related tutorials. Sales of compromised networks, user accounts, and databases containing reward/loyalty points and personally identifiable information (PII) that could be utilized for social engineering, money laundering, and other attack vectors. Since the emergence of cyber-enabled crime, services and activities facilitating travel fraud have been extensively promoted and sought after by threat actors. Cybercriminals mainly leverage stolen card-not-present (CNP) data and reward/loyalty points obtained from compromised bank accounts to procure flights, accommodations, and other travel-related services. Furthermore, threat actors persistently refine their strategies for harvesting reward/loyalty points through compromised accounts, deceiving victims into disclosing their travel-related documentation and data and circulating updated guidelines for circumventing hotel and airline reservation services, amongst other activities. Protecting travelers and improving the customer experience Combatting hospitality and hotel fraud requires collaboration between industry stakeholders, government entities, and financial institutions. Travel professionals should focus on: Enhancing data security: Invest in robust cybersecurity measures to protect guest information, payment systems for CNP, and loyalty programs. Implementing identity verification: Utilize advanced technologies, such as biometric authentication and behavioral analytics, to verify guests' identities and prevent account fraud. Educating staff and guests: Provide comprehensive training to employees on recognizing and reporting suspicious activities. Educate guests about potential scams and advise them to book directly through official channels. Sharing information: Establish platforms to share intelligence and best practices to stay ahead of evolving fraud techniques. Acting with the right solution As the travel and hospitality industry continues to thrive, so does the risk of hospitality fraud. Travelers and hoteliers alike must remain vigilant to protect their finances from various fraud schemes prevalent today. By staying informed, taking proactive measures, and fostering collaborative efforts, we can create a safer and more secure environment within the travel industry. Experian’s identity verification solutions power advanced capabilities across the travel lifecycle. With trusted data and advanced analytics, you can gain a complete view of your future guest to improve risk management and offer an enhanced, frictionless customer experience. Learn more *This article leverages/includes content created by an AI language model and is intended to provide general information.